incursion
@incursi0n
💩💩💩💩💩💩💩💩💩💩💩
github.com/incursi0n
ID: 1493617586608623618
15-02-2022 16:06:08
53 Tweet
7 Followers
110 Following




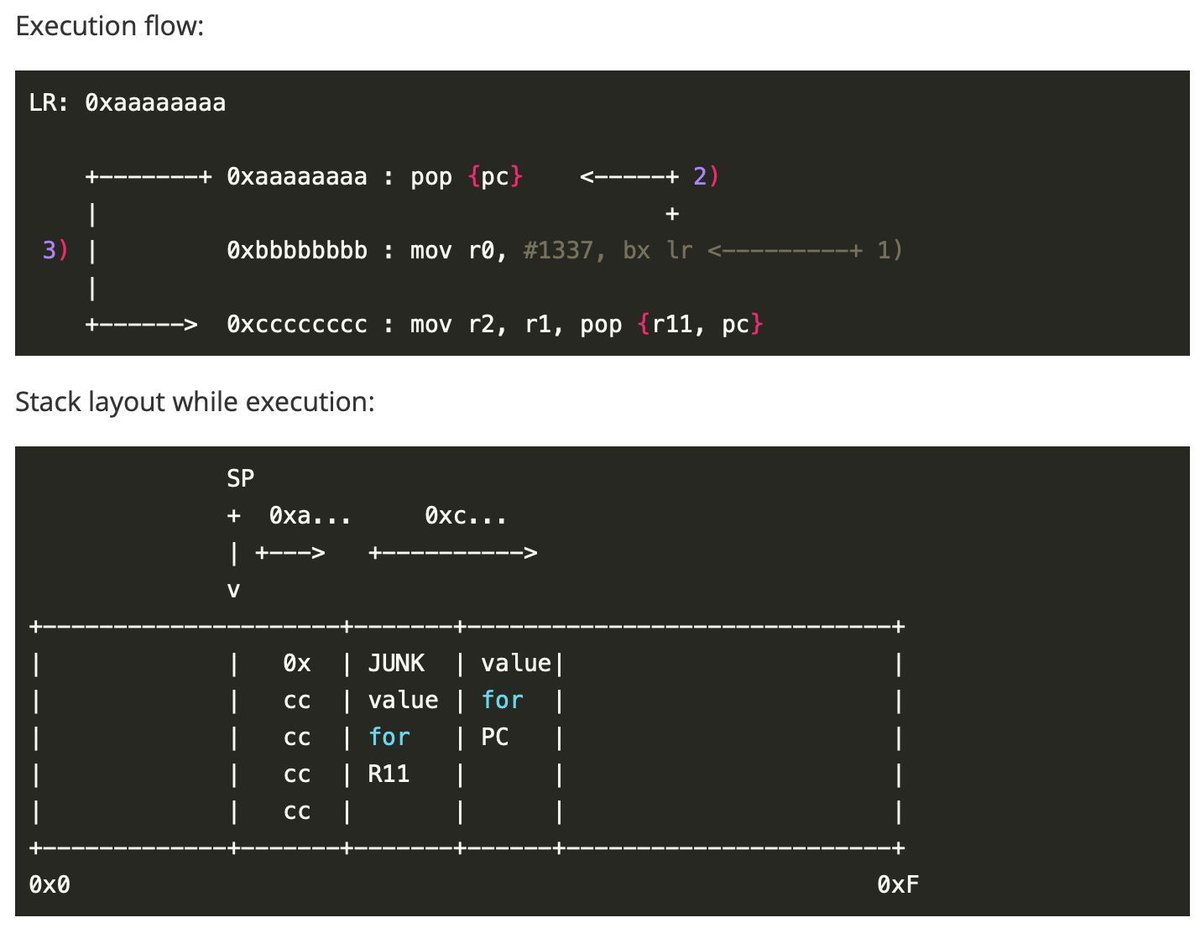
Short intro to ARM exploitation for beginners by 1. blog.3or.de/arm-exploitati… 2. blog.3or.de/arm-exploitati… 3. blog.3or.de/arm-exploitati… 4. blog.3or.de/arm-exploitati… Credits Dimitrios Slamaris #arm #infosec




Put up the slides for my Microsoft BlueHat 2024 presentation on improvements to OleView.NET github.com/tyranid/infose… You can also grab v1.15 of OleView.NET from the PS Gallery which has the new features to generate proxy clients on the fly.