Dimitrios Slamaris
@dim0x69
Cyber Cyber @ Bosch
ID: 138540427
https://blog.3or.de 29-04-2010 21:06:55
876 Tweet
1,1K Takipçi
405 Takip Edilen



Anybody already in Heidelberg TROOPERS Conference on sunday evening and up to a little meetup? :)

Extremely proud to announce some of the research I/we have been conducting over the last few months at the Hardware Security Research lab at Technology Innovation Institute. This is my first vulnerability and public CVE (CVE-2023-35818). Security advisory by the manufacturer: espressif.com/sites/default/…



Nice Introduction to embedded systems security and TrustZone Credits Dimitrios Slamaris embeddedsecurity.io #trustzone #cybersecurity


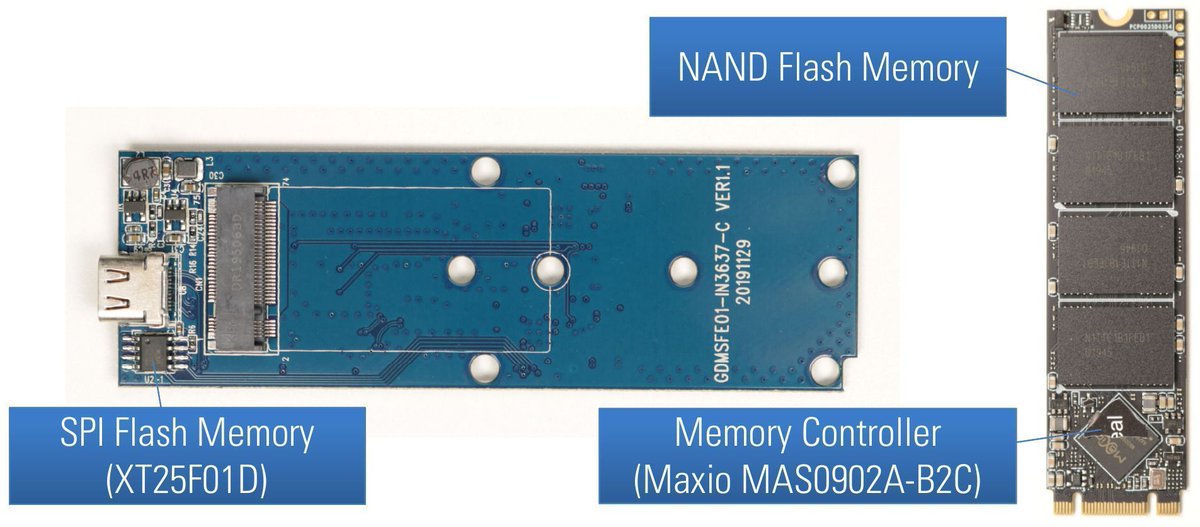
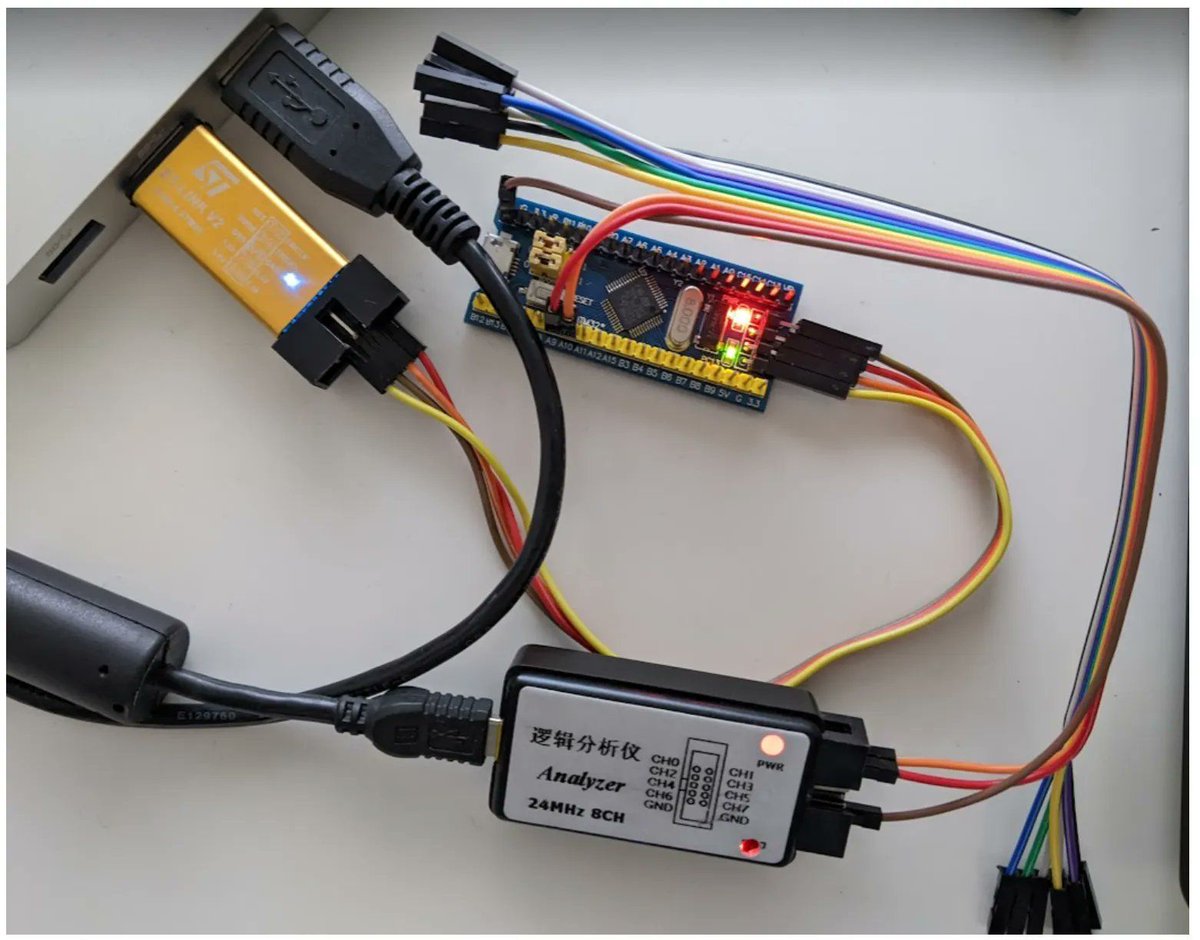
Reverse engineering of AES protected USB flash drives Excellent research Matthias Deeg blog.syss.com/posts/hacking-… blog.syss.com/posts/hacking-… #hardware #infosec #aes

ARM Exploitation - Defeating DEP - executing mprotect() : blog.3or.de/arm-exploitati… ARM Exploitation - Defeating DEP - execute system() : blog.3or.de/arm-exploitati… ARM Exploitation - Setup and Tools : blog.3or.de/arm-exploitati… ARM Exploitation: Return oriented Programming (Building

Embedded Systems Security and TrustZone : embeddedsecurity.io credits Dimitrios Slamaris

Excellent introduction guide to ARM TrustZone and embedded systems security by Dimitrios Slamaris embeddedsecurity.io #trustzone #infosec



if you're interested in securing embedded applications, this introduction to ARM Trustzone by Dimitrios Slamaris is insanely good: embeddedsecurity.io/sec-tz-basics


The award-winning Qualys Threat Research Unit (TRU) has discovered a critical vulnerability in OpenSSH, designated CVE-2024-6387 and aptly named "regreSSHion." This Remote Code Execution bug grants full root access, posing a significant exploitation risk. blog.qualys.com/vulnerabilitie…