
Maxime Meignan
@th3m4ks
This social network is really toxic, I left. Look for "themaks" on BlueSky and Infosec Exchange to reach me. Cheers
ID: 401069502
30-10-2011 00:42:55
202 Tweet
522 Followers
368 Following


Donjon CTF is now over. Congratulations to the winners: 1. meltdown 2. Izy Wallet (MANSOUR Cyril, Maxime Meignan, i27) 3. Idefix First 3 teams managed to solve all the challenges. Full scoreboard is available on the CTF site donjon-ctf.io See you next year!

🇫🇷🎙️ Nouvel épisode du podcast Hack'n Speak avec Maxime Meignan & Qazeer pour parler de leur outil EDRSandBlast 🚀 Une interview un peu plus technique que d'habitude où l'on parle du fonctionnement d'un EDR et des mécanismes de contournement 🔥 Bonne écoute 🎶anchor.fm/hacknspeak

Un titre et une miniature clickbait au possible ? En effet. Du fond ? Encore plus ! Vidéo à ne pas rater, pour tout public, que je recommande sans hésiter ! GG Romain du Marais


Aaand it's a wrap! EDRSandblast v1.1 and the slides from the DefCon30 DemoLab "EDR detection mechanisms and bypass techniques with EDRSandblast" with Maxime Meignan can now be found on GitHub: github.com/wavestone-cdt/… 1/2


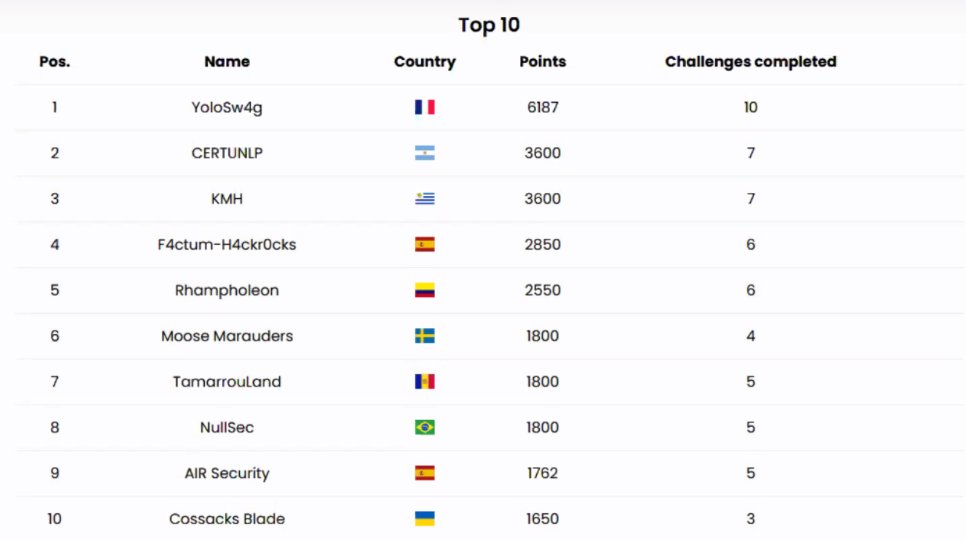
🚩 Wavestone France CTF team #YoloSw4g ranks first of 80+ teams at #CyberEx23! 🚩 Thanks INCIBE and OEA Ciberseguridad for the organization & challenges! 🚩 Congratz to Qazeer Maxime Meignan and Dlvl François for the great team we've been for the last 8 hours, now we go to a well-deserved sleep!

Continuing the #NtSetInformationProcess exploitation series, Maxime Meignan wrote an article on universal #EDR blinding through exploitation of NtSetInformationProcess and it's worth it riskinsight-wavestone.com/en/2023/10/a-u…


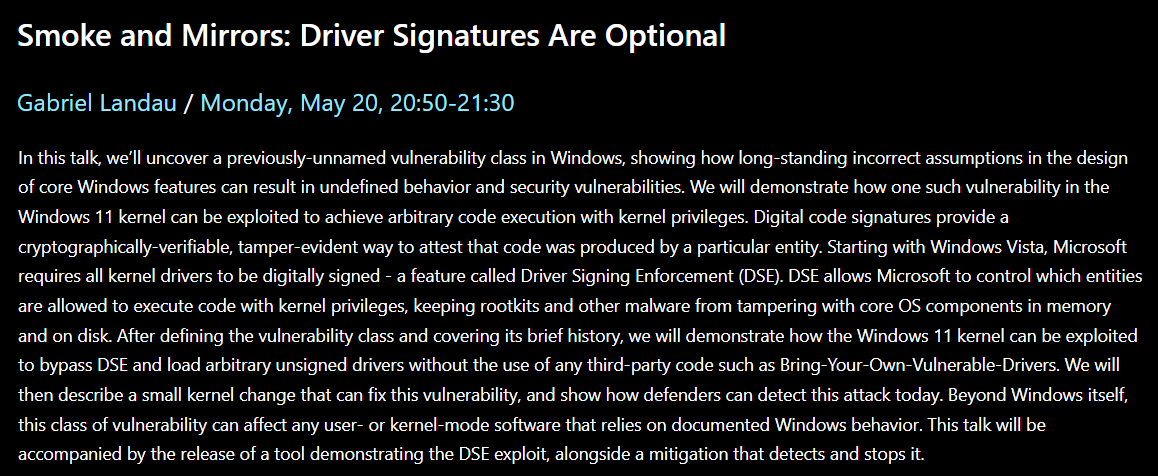
I'm thrilled to announce that I'll be presenting a previously-unnamed vulnerability class at BlueHat IL. Oh, and I'll be dropping 0day. Be sure to stop by, learn something new, pwn the kernel, and have a coffee. It should be a good time. microsoftrnd.co.il/bluehatil/conf…

the Cellebrite Labs French🇫🇷 team is recruiting! Don't miss the rare opportunity to join a team that specializes in breaking Android security boundaries (bootchain/trustzone/Secure Element/kernel and other goodies) for forensic purposes. ⤵️ 1/5

Nous avons quelques tickets pour #hexacon2024 à offrir, car certains collègues de Cellebrite Labs ne peuvent venir. Pour participer, il suffit de répondre à ce tweet, et nous sélectionnerons les gagnants demain (3 octobre) en début d'après-midi !



