Alexandre Borges
@ale_sp_brazil
Vulnerability Researcher and Exploit Developer
ID:60807822
https://linktr.ee/ale_sp_brazil 28-07-2009 04:15:36
7,9K Tweets
22,9K Followers
111 Following


In some situations during vulnerability research I've found functions flagged as functions of no return, so it may be useful to remember how to identify them and, eventually, fix problems. This picture is just a quick review.
#idapro #vulnerability #reverseengineering


In some situations during vulnerability research I've found functions flagged as functions of no return, so it may be useful to remember how to identify them and, eventually, fix problems. This picture is just a quick review.
#idapro #vulnerability #reverseengineering






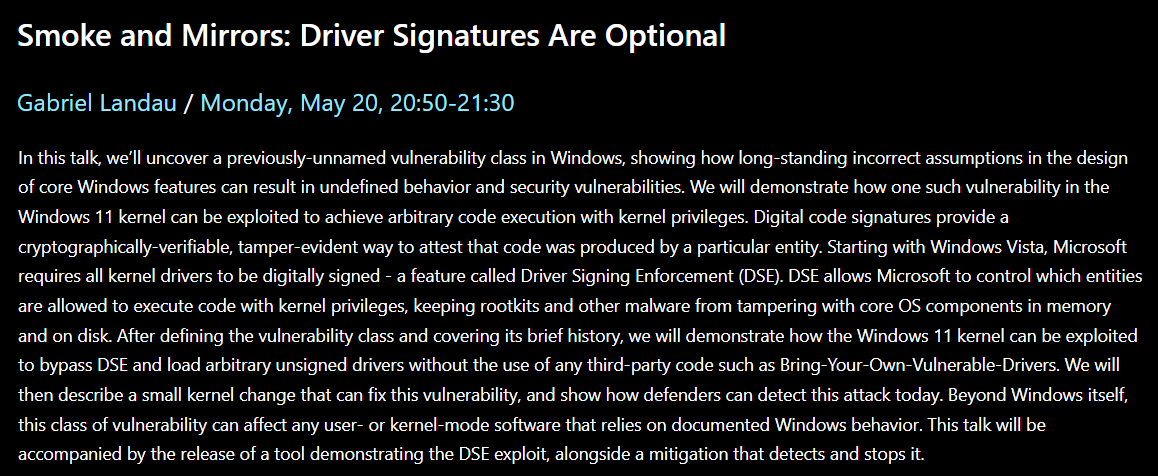
I'm thrilled to announce that I'll be presenting a previously-unnamed vulnerability class at BlueHat IL.
Oh, and I'll be dropping 0day. Be sure to stop by, learn something new, pwn the kernel, and have a coffee. It should be a good time.
microsoftrnd.co.il/bluehatil/conf…


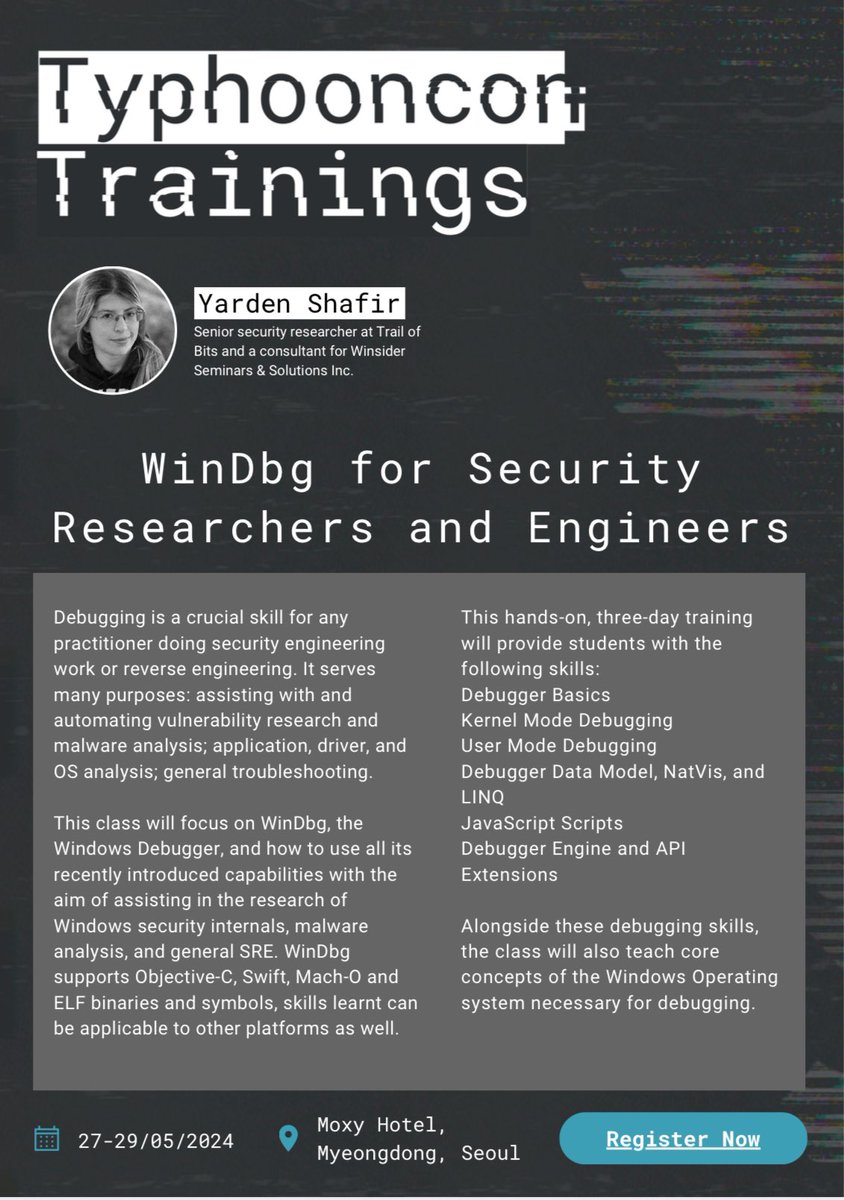
Join me tomorrow on the Off By One Security stream with special guest Pavel Yosifovich Pavel Yosifovich for a session on Windows Device Drivers Internals, ...and Some Additional Reversing! 19-April at 11AM PT. Looking forward to this one!
youtube.com/watch?v=7Trgnw…



Josh Stroschein | The Cyber Yeti Thanks for using PEbear! I know it is an old video, so it makes sense that you remap it this way. Just FYI, now the same thing can be done just by one click: youtube.com/watch?v=9Cqq44…

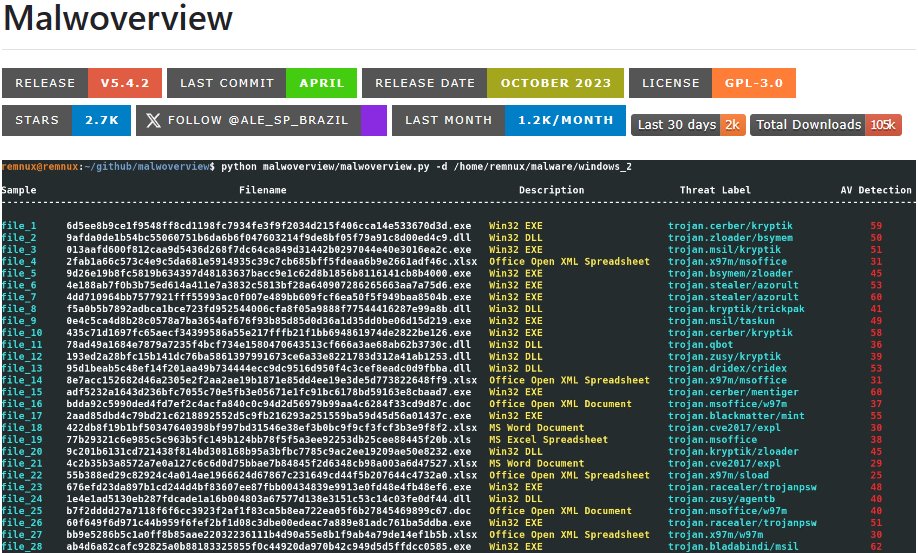
Antoine Cailliau Alexandre Dulaunoy @[email protected] Florian Roth Only executable files or any file format?
There are some datasets for specific formats, for example PDF:
corp.digitalcorpora.org/corpora/files/…
For MS Office: decalage.info/fr/download_ms…
Caveat: those datasets may contain some malicious files.
I'd be interested to find datasets for other formats.

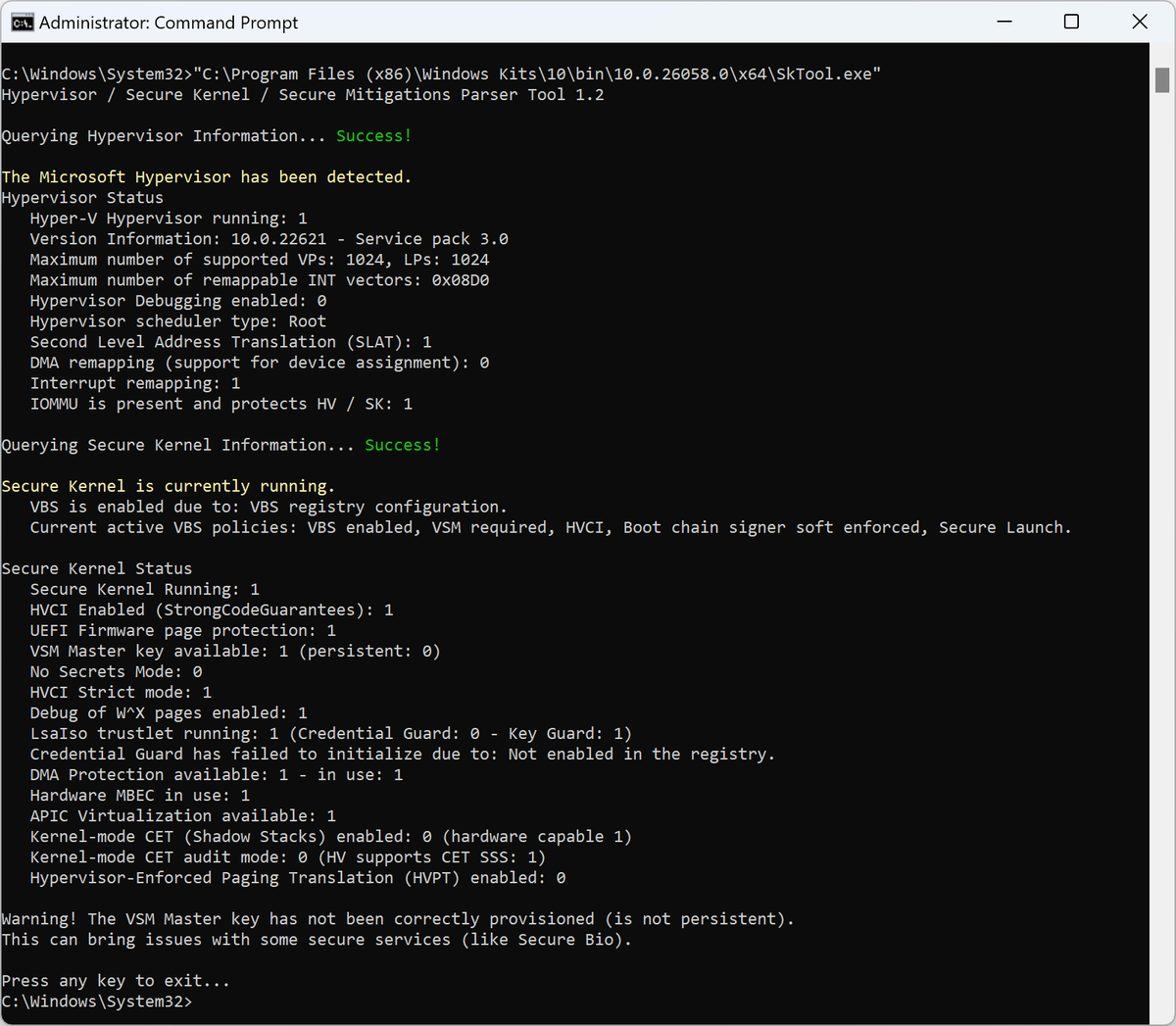
Shout out to Andrea Allievi for building SkTool. The easiest way to find out what Hypervisor / secure kernel features are enabled on a system


✍️🇻🇳My quick note about techniques employed by the threat actor in the phishing email to distribute #WarZoneRAT via #DBatLoader .
kienmanowar.wordpress.com/2024/04/09/qui…