Simon
@techevo_
Principal Threat Hunter @ WithSecure
bsky.app/profile/techev…
ID: 235278328
https://blog.techevo.uk 07-01-2011 20:03:48
175 Tweet
81 Followers
701 Following








I took a look at a #warmcookie infection, and wrote an investigation walk-through using a #PCAP from malware_traffic, check it out: blog.techevo.uk/analysis/netwo…





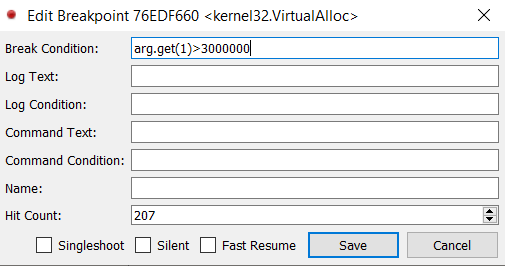
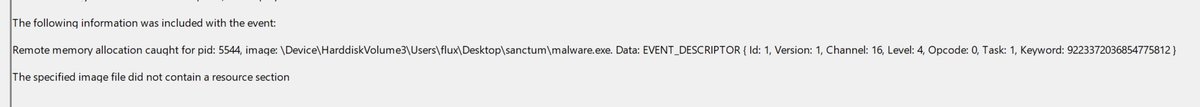
With some guidance from DebugPrivilege I've found a way to easily dump clear text implants even while they sleep. Bad day for sleep obfuscation 💤 blog.felixm.pw/rude_awakening…