jk42
@jkfourtwo
42!
ID: 812449727727935488
24-12-2016 00:08:04
1,1K Tweet
154 Followers
479 Following






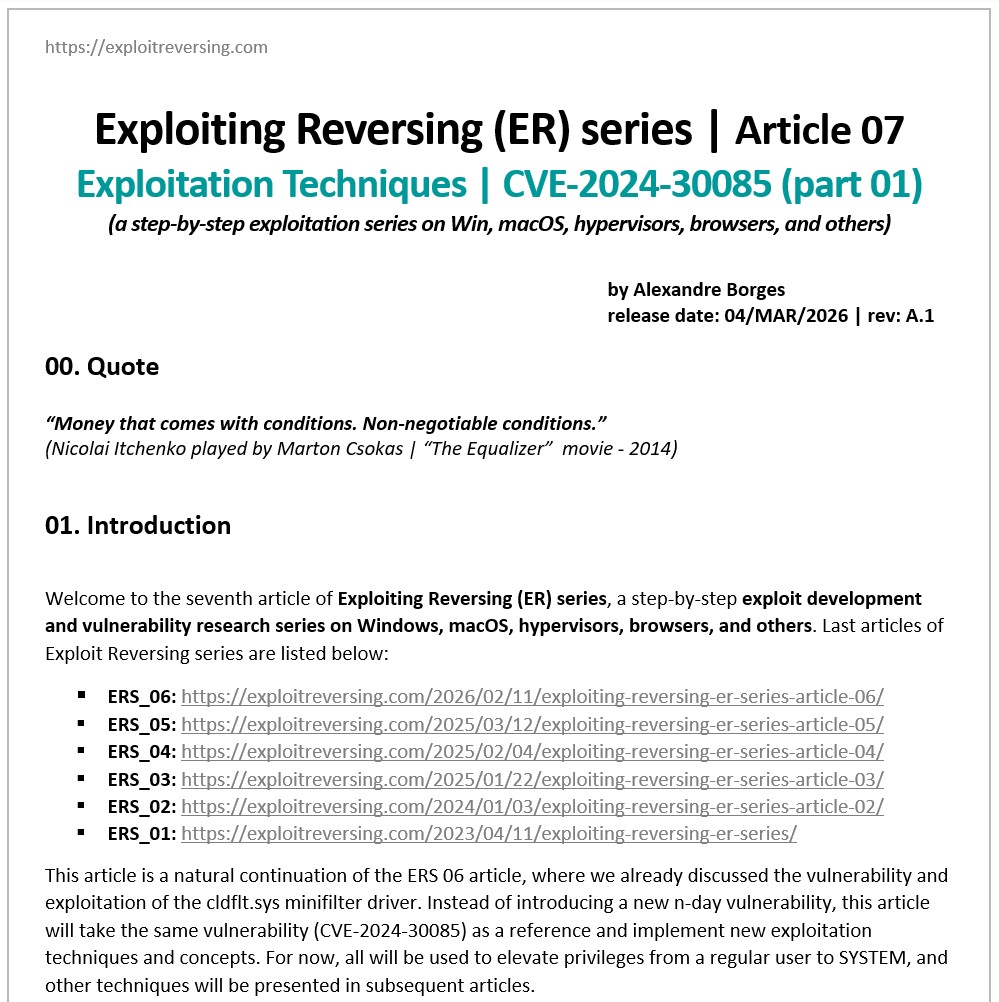
I recommend reading this, it's very decent content 💙 Thank you Thomas Roccia 🤘 my friend for sharing this valuable content! 🙏 But read it all, slowly, carefully — the title is strong and some can just skim and leave thinking reverse engineering is dead, replaced by AI… which is not






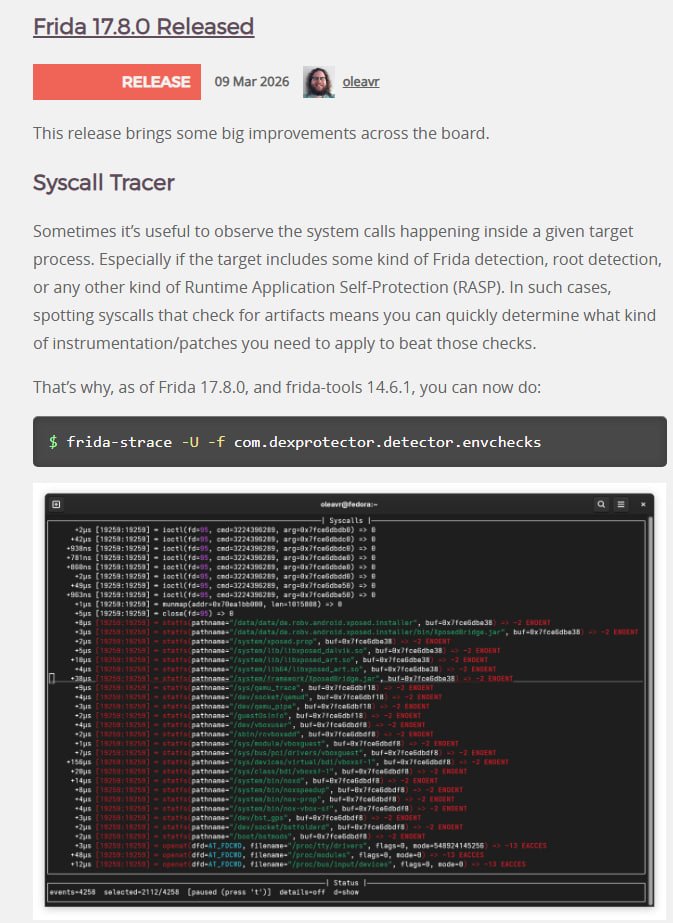
Speakeasy emulator v2b1 is here! 🚀 Massive upgrade thanks to Willi Ballenthin. Modernized codebase using Unicorn 2. Now handles complex multi-stage unpacking and deep system introspection. API traces on par with sandbox analysis. github.com/mandiant/speak… pypi.org/project/speake…