
i5nipe
@i5nipe
Cyber Security Enthusiast | OSCP+ | eMAPT | eCPPTv2
ID: 1336490304602591236
https://blog.i5nipe.com 09-12-2020 01:58:26
156 Tweet
619 Followers
400 Following

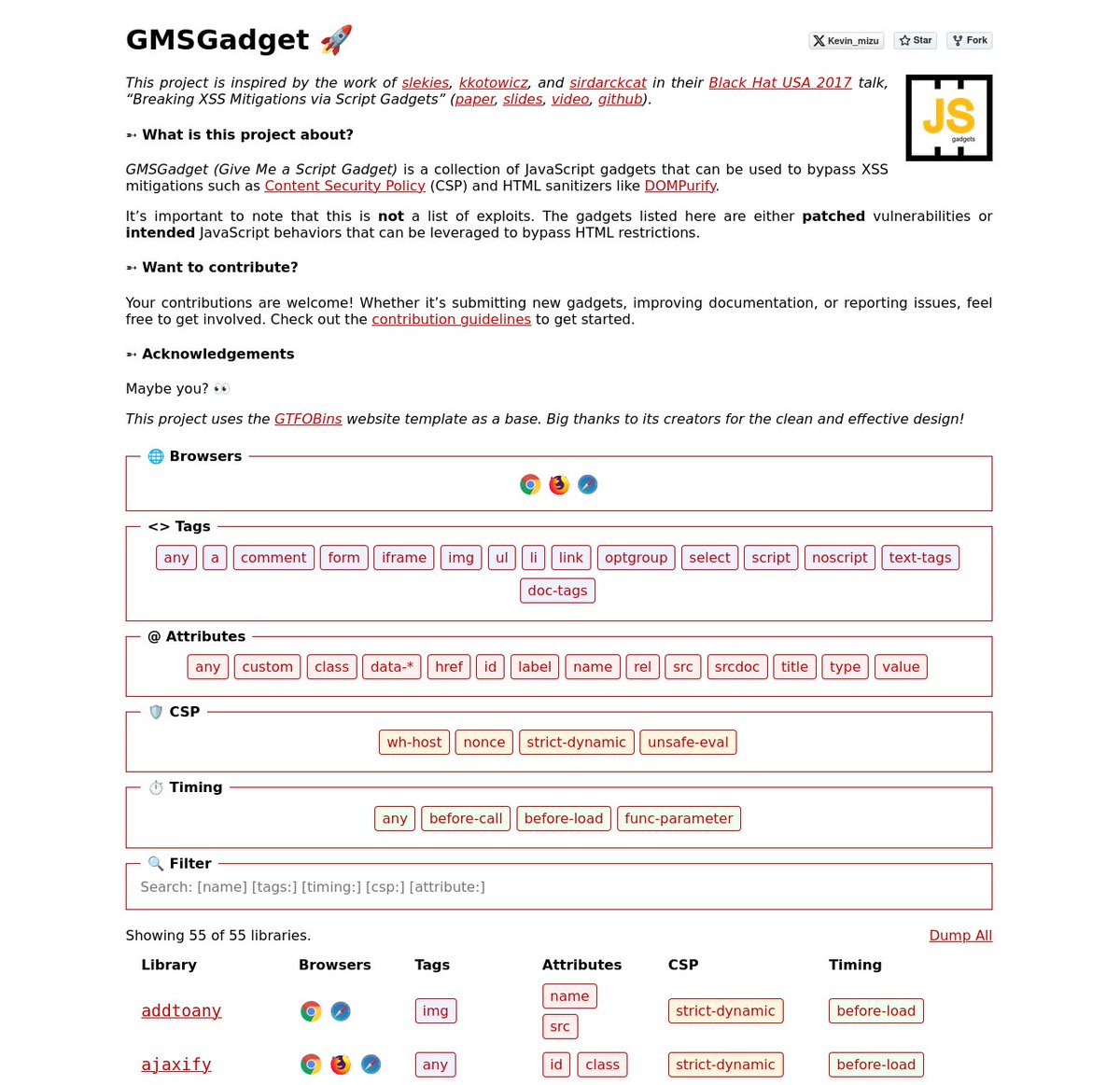
I'm happy to release a script gadgets wiki inspired by the work of Sebastian Lekies, koto, and Eduardo Vela in their Black Hat USA 2017 talk! 🔥 The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇 gmsgadget.com 1/4


The AD CS security landscape keeps evolving, and so does our tooling. 🛠️ Valdemar Carøe drops info on Certify 2.0, including a suite of new capabilities and refined usability improvements. ghst.ly/45IrBxI


Finally, with NoRiskNoLive, we managed to bypass the Cloudflare mTLS protection after around 5 days of work. I'd like to share a few golden tips for bug bounty hunters who might face something similar in the future. But first, here's a quick summary: The target was a banking app with


This blog post about impostor certificates by Squiblydoo is a gem and very relevant right now. Or: How threat actors impersonate companies to obtain authenticode certificates for signing their malware. And why revokation is important. squiblydoo.blog/2024/05/13/imp…



TombWatcher from Hack The Box is an assume breach Windows AD box. BloodHound shows a path abusing targeted Kerberoasting, GMSA, password change, and shadow creds. Then there's AD Recycle Bin and ESC15. 0xdf.gitlab.io/2025/10/11/htb…


0-click vulnerability affected Android in Dolby's DDPlus decoder-CVE-2025-54957 Malformed audio could lead to memory corruption and crashes. Android decodes audio locally, making this exploitable without user interaction just by receiving crafted RCS voice message by Natalie Silvanovich




AdminSDHolder: the AD security feature everyone thinks they understand but probably don't. 😬 Jim Sykora went to the source code to debunk decades of misconceptions — including ones in Microsoft's own docs. Read more ⤵️ ghst.ly/3Lpmjzv












