Bryan Alexander
@dronesec
researcher. exploit dev. hacking @ stripe
stop using twitter. find me @ [email protected]
ID: 615696093
http://dronesec.pw/ 22-06-2012 23:25:57
1,1K Tweet
1,1K Followers
335 Following




New blog post! Part 1 in my new PlayStation hacking series: An **unpatched** PS4 / PS5 userland exploit that also allows pirating PS2 games. mast1c0re: Hacking the PS4 / PS5 through the PS2 emulator - Part 1 - Escape: cturt.github.io/mast1c0re.html Video demo: youtube.com/watch?v=GIl1mR…





My keynote "The Evolution of Firmware Threats: Attacks below the OS" from No Hat Con is now available online! youtube.com/watch?v=L1VanO…

Inside Elon Musk's "free speech" Twitter, a culture of secrecy and fear has taken hold. Managers and employees have been muzzled, Slack channels have gone dark, and workers are turning to anonymous gossip apps to find out basic info about their jobs. washingtonpost.com/technology/202…

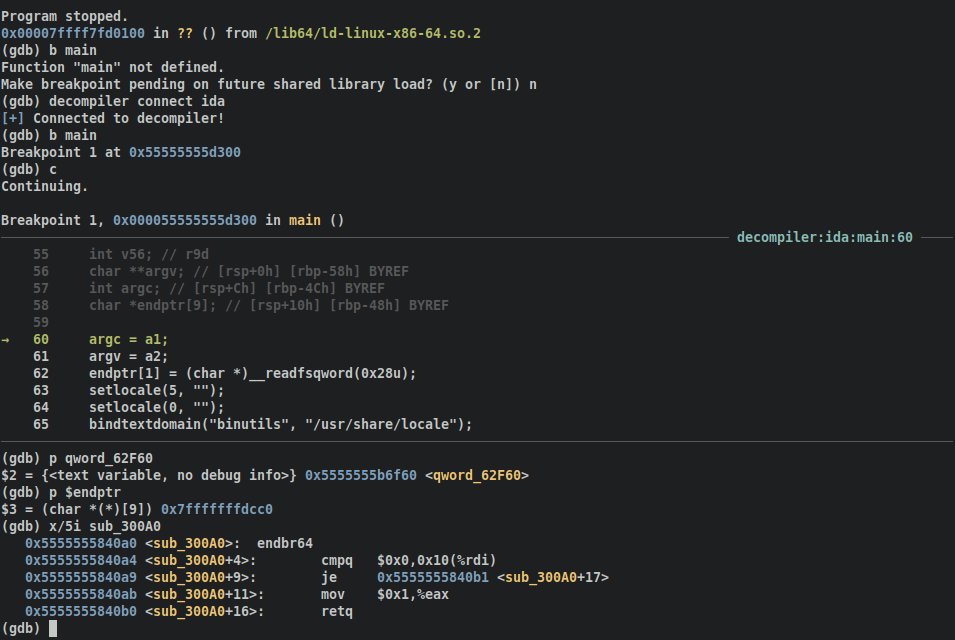
Now this is a pretty handy tool... "A plugin to introduce interactive symbols into your debugger from your decompiler" // by Zion Leonahenahe Basque github.com/mahaloz/decomp…





Control Your Types or Get Pwned: Remote Code Execution in Exchange PowerShell Backend - Piotr Bazydło provides the details of CVE-2022-41040 and -41082. These were the #Exchange bugs used in active attacks and recently patched. zerodayinitiative.com/blog/2022/11/1…