Dnucna
@dnucna
Cybersecurity and fun
ID: 3344515179
24-06-2015 20:43:09
2,2K Tweet
100 Takipçi
838 Takip Edilen





📚 New chapter in Trail of Bits' Testing Guide: Burp Suite Step-by-step guide to rapidly master @portswigger's Burp Suite ➡️ Using Burp Repeater, Intruder, and Collaborator, ➡️ Useful plugins ➡️ Best practices ➡️ Burp features to find specific vulns blog.trailofbits.com/2024/06/14/ann…




Our team collaborated with Eamon Javers and the video team on this digital documentary premiering now: Putin's Trader: How Russian hackers stole millions from U.S. investors Paige Tortorelli @CNBCBria Jeniece Pettitt cnbc.com/2024/08/01/put…



Buttercup (the Trail of Bits CRS) scores the FIRST POINT in the AIxCC! Let's GOOOO! x.com/trailofbits/st…

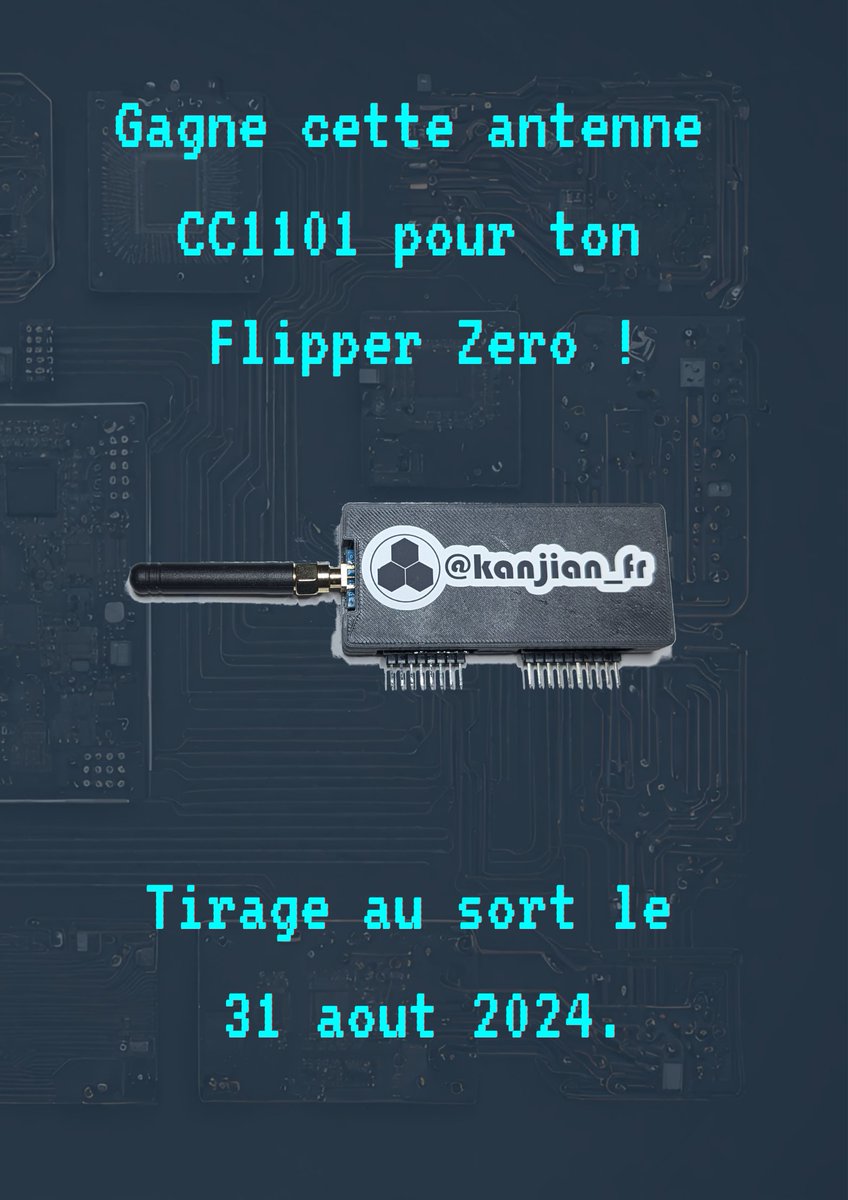
After two years of hard work with Damien Cauquil (@[email protected]) , we are proud to release for DEFCON32 the first public version of WHAD, a whole new ecosystem of opensource libs, tools & firmwares for wireless security ! The main repo is here: github.com/whad-team/whad… . And now, demo time ! [1/n]







Security training is often considered a waste of time. 10 essential techniques from Google Cloud CISO Phil Venables on what leading organizations are doing. 🗒 The Techniques 1. Computer Based Training (if you have to do it then do it better) 2. Ambient Controls (Solutions