Lars
@bob5ec
#LangSec conspirator eleminating injection vulnerabilities, #DevSecOps practitioner authoring #SecurityBelts and #ThreatModeling security architecture.
ID: 456772197
https://github.com/AppSecure-nrw/security-belts 06-01-2012 16:56:53
1,1K Tweet
213 Followers
313 Following

I'm a proud sponsor of LocoMocoSec: Hawaiʻi Security Conference! Please apply for the call for papers, open until March 31. Ladies and non-binary folks, this includes YOU! Everyone should apply! sessionize.com/loco-moco-secu…
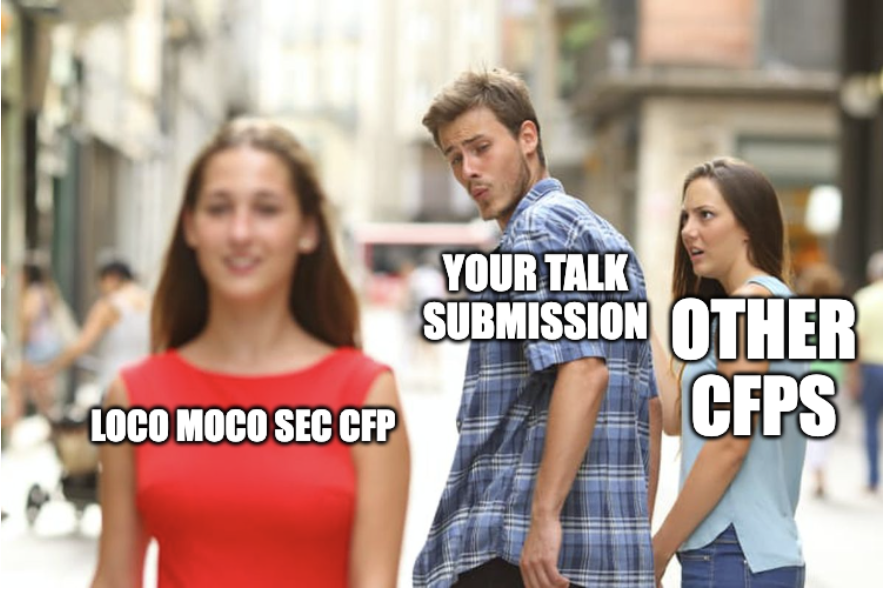

⏰ LAST CHANCE! Submit now to speak LocoMocoSec: Hawaiʻi Security Conference July 17-18 in Kaua'i! tinyurl.com/4m4jxprt







Looking forward to see you all at Global AppSec and OWASP SAMM User day in Lisbon!


I just launched a new post with Clint Gibler over on tl;drsec, check it out! When I read Wiring the Winning Organization (Gene Kim, Steven Spear), I spent the whole time trying to map the concepts to Security 1/2





Looking forward to talk about Security Coaching at @heise_devSec with @jn_struewer and Der Benji ✨ heise-devsec.de/veranstaltung-…



Greetings from Lisbon. Looking forward to OWASP SAMM User day and OWASP® Foundation AppSec Global.


I had a great time meeting the OWASP SAMM Community. Lots of like-minded people! TIL: OWASP SAMM is for people running an #AppSec program. Target groups are not Developers or Security Champions. Hence OWASP DSOMM and Security Belts need to be there to support these target groups.

🦀 Eliminating Memory Safety Vulnerabilities at the Source Rust caused memory safety vulnerabilities % in Android to drop from 76% to 24% over 6 years. 💡Key insight: new code is disproportionately responsible for bugs By Jeff Vander Stoep, Alex Rebert security.googleblog.com/2024/09/elimin…