Der Benji ✨
@spreadthekaozz
Father, #DevSecOps, #InfoSec enthusiast, agilist with common sense, and anarchistic chaot (AD&D: Chaotic Good)
ID: 808300697452220416
https://benjitrapp.github.io 12-12-2016 13:21:18
2,2K Tweet
130 Followers
1,1K Following





Cool secure boot bypass by fault injection in (Espressif) ESP32 CPUs by LimitedResults limitedresults.com/2019/09/pwn-th… #embedded #iot #hardware #faultinjection #infosec










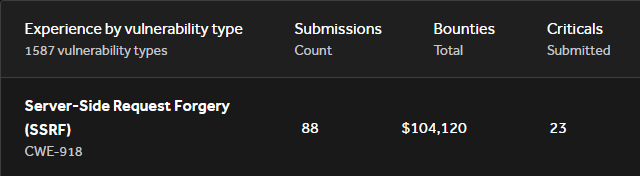
Citrix NetScaler ADC CVE-2023-3519 resources -- Compromise Assessments Cybersecurity and Infrastructure Security Agency advisory cisa.gov/sites/default/… Deyda guide deyda.net/index.php/en/2… -- Vuln Checks Python github.com/telekom-securi… Nmap NSE script github.com/RootUp/Persona… I'm gonna add more links in this🧵