RUSHII🦁🇮🇳/
@u1tran00b
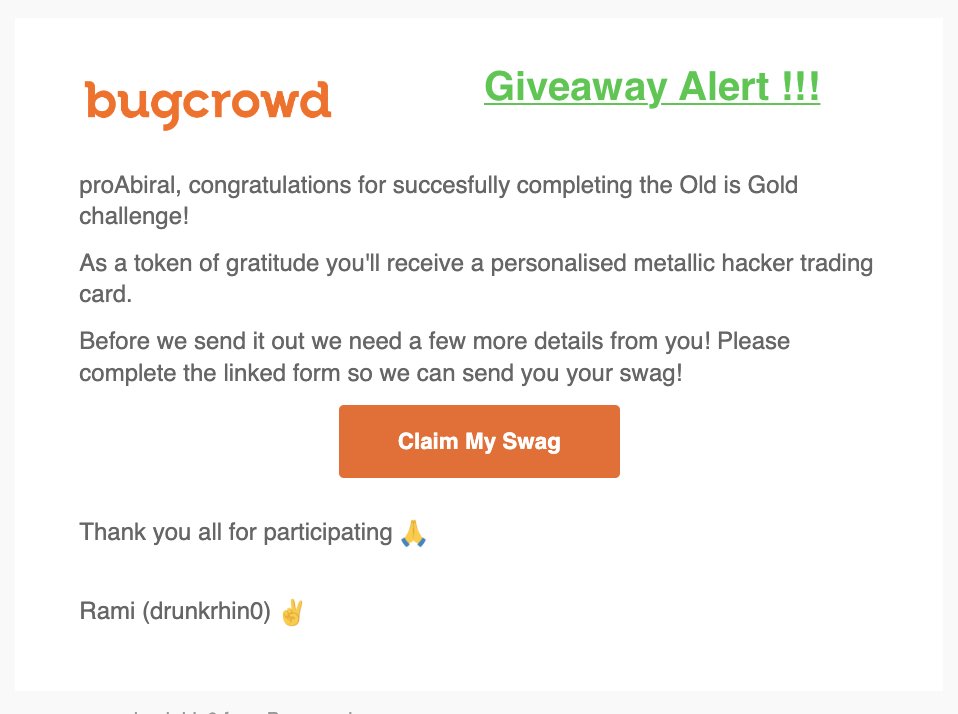
Infosec Junkie, Pentester, Part-Time Bug Bounty @Bugcrowd @SynackRedTeam, Ambassador @Bugcrowd, Freelancer 💻 🎒 | CRTO | eCPPTv2 | eWPTXv2 | ShivaHolic 🕉🔱
ID: 926482846742609921
03-11-2017 16:14:58
859 Tweet
2,2K Followers
480 Following





Check out Bollina Bhagavan's Bhagavan Bollina 🚩 new blog on "Getting shell and data access in AWS App Runner" Read on and share your thoughts! Link: blog.appsecco.com/getting-shell-… #aws #cloudsecurity #redteam #infosec #appsecco












Can someone with contact at Delhi Police POLICE COMMISSIONERATE GHAZIABAD help? Please DM me or SUMIT WAHI