Tarik
@tw4vesx
ID: 1430204350152986632
24-08-2021 16:24:49
46 Tweet
45 Followers
339 Following

















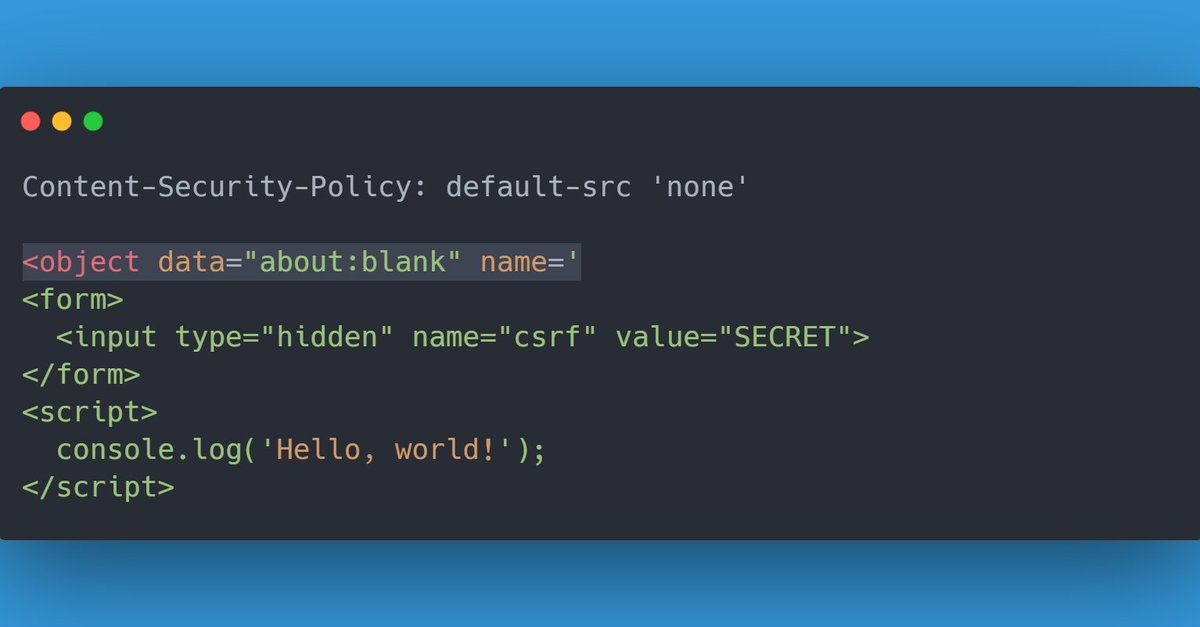
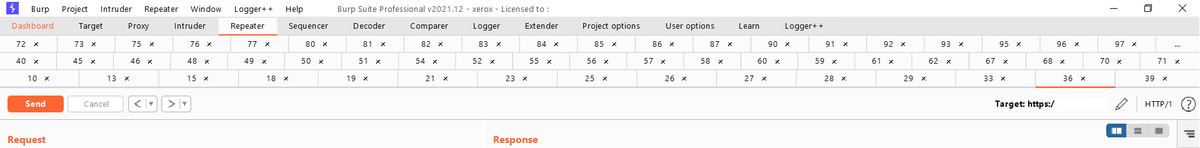
While playing a challenge by Salvatore Abello, I found a pretty interesting way to exploit Dangling Markup with a strict CSP. All you need is an <iframe>, <object> or <embed> set to about:blank, with a dangling name= attribute. This vulnerable page should be iframable.