
tonvi
@t0nvi
ID: 107230970
21-01-2010 22:44:39
710 Tweet
299 Followers
562 Following




The video for my talk at offensivecon with Cedric Halbronn is out! It was an absolute pleasure working with Cedric on this dream of mine! youtu.be/goEb7eKj660

Looks like BlueHat IL talks are online now, so here’s my talk for anyone who wanted to learn about the latest episode of KASLR and couldn’t make it: youtu.be/Dk2rLO2LC6I



Recon 20th year anniversary is almost upon us, and we just realised we got our first a copyright Strike on Youtube on one of our last year video. I guess VMProtect is not happy about Holger Unterbrink talk. We will release the video soon directly on our website. Stay tuned.







Cloudflare CEO Matthew Prince 🌥 is having the most honest conversations I've come across about the current & future of content creation "6 months ago, 75% of queries to Google get answered on Google. Which means if you're an original content creator, your content is getting





Rasta Mouse To clarify because I realized I forgot an important detail: you can still call the API from Medium IL in recent windows 11 but the Object field leaking a kernel address will be 0 unless the caller has SeDebugPrivilege enabled.


![hackyboiz (@hackyboiz) on Twitter photo [Research] CVE-2025-24985: Windows Fast FAT Driver RCE Vulnerability
hackyboiz.github.io/2025/07/17/ogu…
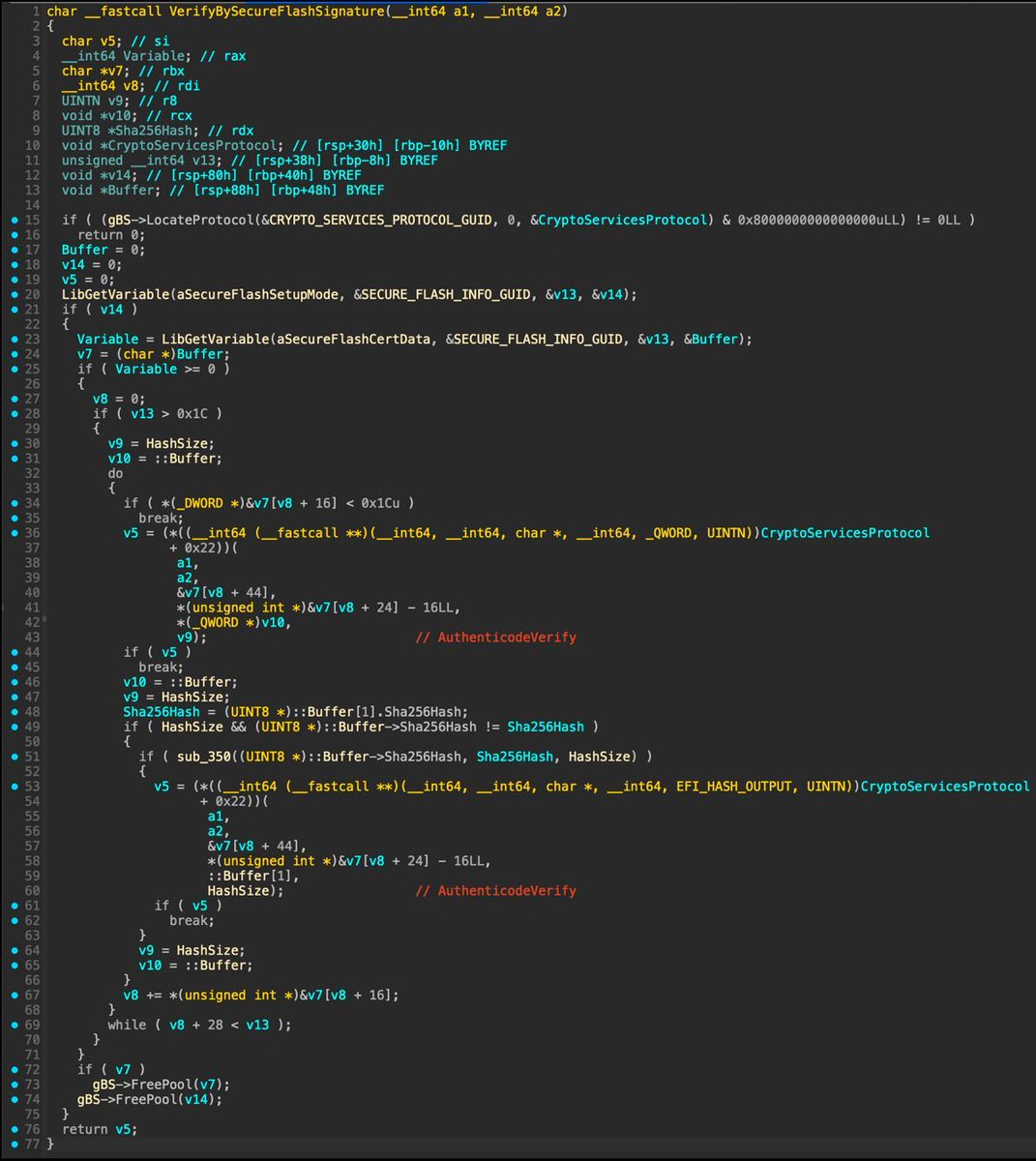
The vulnerability was caused by the ability to control five variables within the VHD file that determine the number of clusters. [Research] CVE-2025-24985: Windows Fast FAT Driver RCE Vulnerability
hackyboiz.github.io/2025/07/17/ogu…
The vulnerability was caused by the ability to control five variables within the VHD file that determine the number of clusters.](https://pbs.twimg.com/media/GwC4HkLasAEh-9D.jpg)