Kail
@specterfive
Sr. Information Security Engineer (red teamer) at a Fortune 500. I ❤️ CTFs, Photography, and video games. [email protected]
ID: 15851688
14-08-2008 15:35:13
1,1K Tweet
1,1K Followers
1,1K Following


Introducing ShadowSpray, it's like password spray but with shadow credentials. More info in the repo. Huge thanks to Elad Shamir for the amazing technique and to Will Schroeder (and others) for the implementation in Rubeus from which a lot of code was taken. github.com/Dec0ne/ShadowS…


You can find me on Mastodon at [email protected]








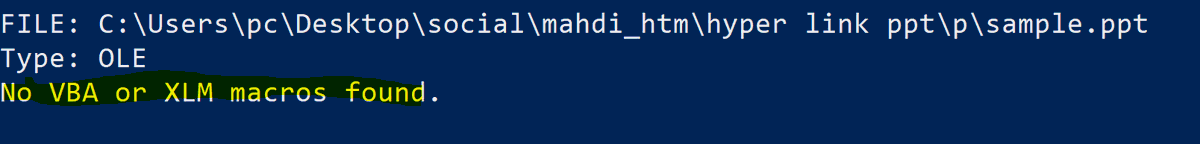
We've just published a quick write up on CVE-2023-23397, which allows a remote adversary to leak NetNTLMv2 hashes: mdsec.co.uk/2023/03/exploi… by Dominic Chell 👻