
sh4hin
@s3cdev
Threat Emulation/Hunting | Linux/Mac enthusiast
ID: 843399295
https://github.com/sh4hin 24-09-2012 11:15:25
410 Tweet
979 Followers
4,4K Following

Tony ippsec Rob Fuller Derek Rook @[email protected] Tunny Traffic James Hooker g0t mi1k inCIDRthreat Build your own lab, then ask interesting questions and explore. bit.ly/kickasslab is a decent start :) Da has some amazing resources too, check out his book!













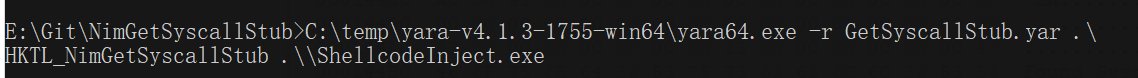
NimGetSyscallStub is now public, the first public fully working (didn't find another myself) Nim imlementation + PoC to grab fresh Syscalls from disk on runtime: github.com/S3cur3Th1sSh1t… Cas van Cooten even with a yara rule (with your template 🤓)


Check out capa v4 with: 1. support for analyzing .NET executables 2. finer grained capability detection via instruction and operand features 3. many new and updated detection rules Blog: mandiant.com/resources/blog… Binaries: github.com/mandiant/capa/… Source: github.com/mandiant/capa
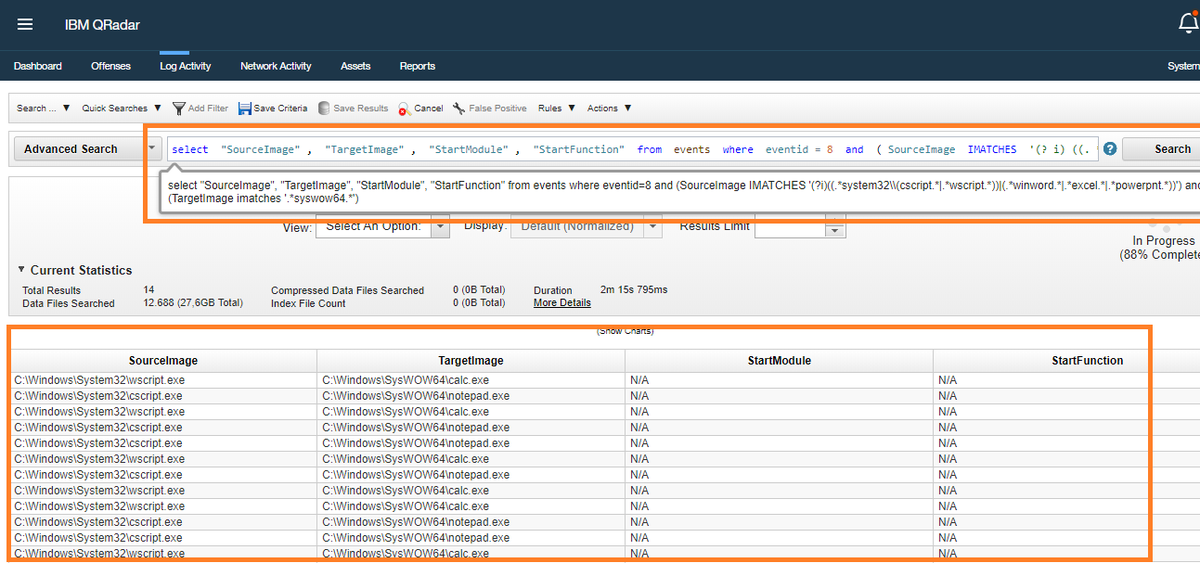
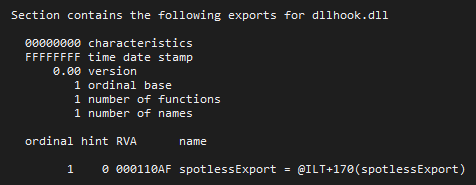
I'm happy to share the results of months of research on code injection, process tampering, and their detection! 🥳 Here you'll find technique categorization, a dive into the underlying OS mechanisms, sample demos, detection suggestions, and much more: huntandhackett.com/blog/concealed…


In nearly all of our on-premises engagements, a threat actor has taken total full control of Active Directory. If you are interested in the kind of things Microsoft DART finds, and how we recommend you secure Active Directory, then this blog is for you - techcommunity.microsoft.com/t5/microsoft-s…

![Matthew (@embee_research) on Twitter photo Reverse Engineering a #CobaltStrike #malware sample and extracting C2's using three different methods.
We'll touch on #cyberchef, #x64dbg and Speakeasy from fireeye to perform manual analysis and emulation of #shellcode.
A (big) thread ⬇️⬇️
[1/23] Reverse Engineering a #CobaltStrike #malware sample and extracting C2's using three different methods.
We'll touch on #cyberchef, #x64dbg and Speakeasy from fireeye to perform manual analysis and emulation of #shellcode.
A (big) thread ⬇️⬇️
[1/23]](https://pbs.twimg.com/media/FcXA6sfaUAAKpv_.png)