Ryan Cobb
@cobbr_io
Red Teamer | Hobbyist Software Developer | Operator @SpecterOps
Developer: Covenant, SharpSploit, PSAmsi
ID: 225249135
11-12-2010 03:05:15
895 Tweet
11,11K Followers
480 Following


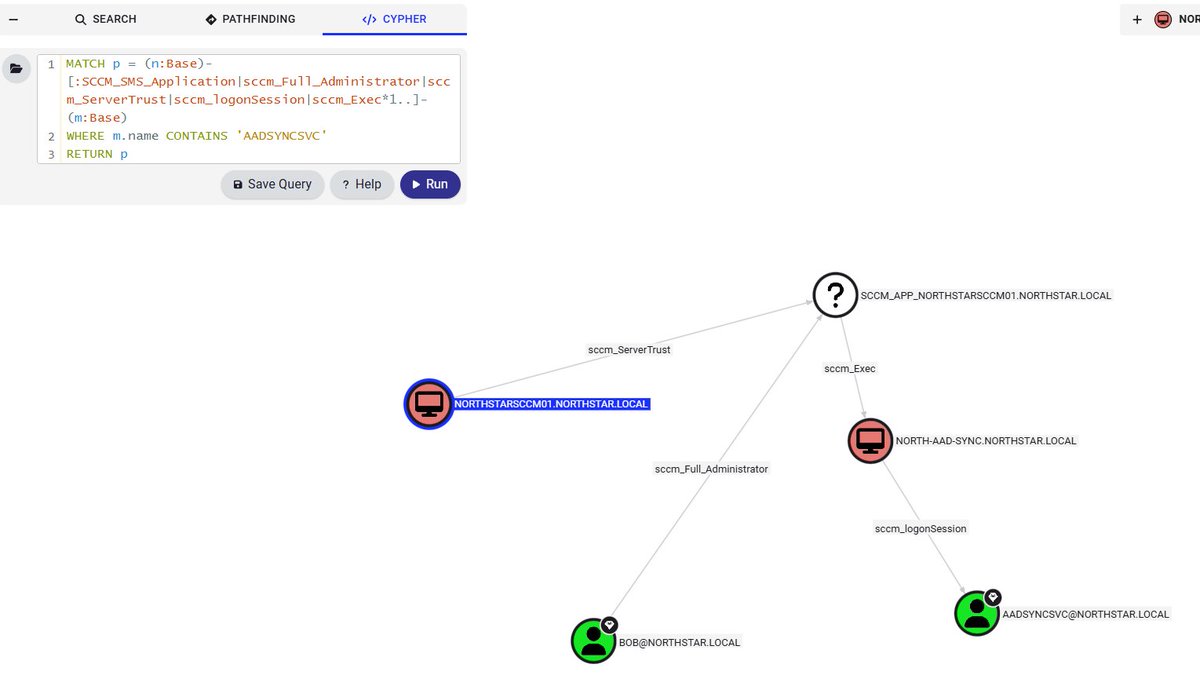
No weekend plans? Daydreaming of attacking SCCM? We're offering access to our Offensive SCCM DEF CON workshop to the first 30 people who DM me. The workshop will be accessible till Wednesday. Please don't claim it if you don't plan on using it. Chris Thompson Garrett Foster





BIG NEWS: SpecterOps raises $75M Series B to strengthen identity security! Led by @InsightPartners with @AnsaCapital, M12 - Microsoft's Venture Fund, Ballistic Ventures, Decibel, and Cisco Investments. ghst.ly/seriesb #IdentitySecurity #CyberSecurity (1/6)


Think NTLM relay is a solved problem? Think again. Relay attacks are more complicated than many people realize. Check out this deep dive from Elad Shamir on NTLM relay attacks & the new edges we recently added to BloodHound. ghst.ly/4lv3E31

Big updates are coming to BloodHound! Join our webinar July 31 to hear from Justin Kohler, Stephen Hinck (he/him), Andy Robbins & Jared Atkinson on some of the new features the team is rolling out. Register ▶️ ghst.ly/july-web-tw


BloodHound v8.0 is here! 🎉 This update introduces BloodHound OpenGraph, revolutionizing Identity Attack Path Management by exposing attack paths throughout your entire tech stack, not just AD/Entra ID. Read more from Justin Kohler: ghst.ly/bloodhoundv8 🧵: 1/7


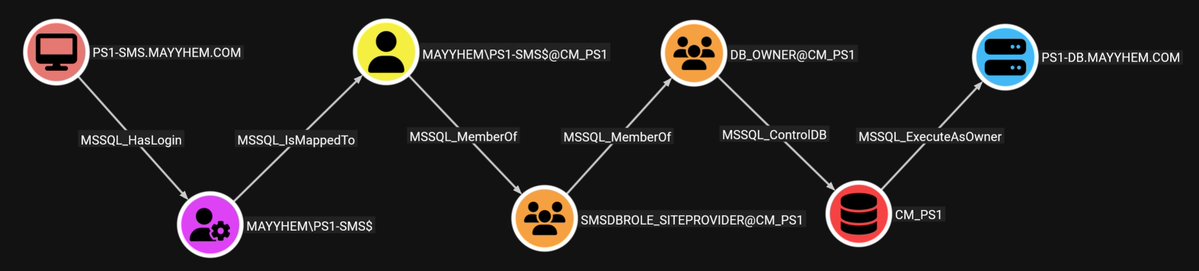
MSSQLHound leverages BloodHound's OpenGraph to visualize MSSQL attack paths with 7 new nodes & 37 new edges, all without touching the SharpHound & BloodHound codebases. Chris Thompson unpacks this new feature in his blog post. 👇 ghst.ly/4leRFFn


👋 Say hello to Nemesis 2.0, a streamlined, Docker Compose-based platform that is laser-focused on file triage. After introducing v1 two years ago, the team has reworked the platform to better serve what people need from it. Read more from Will Schroeder. ⤵️ ghst.ly/4mxQzFU


Credential Guard was supposed to end credential dumping. It didn't. Valdemar Carøe just dropped a new blog post detailing techniques for extracting credentials on fully patched Windows 11 & Server 2025 with modern protections enabled. Read for more ⤵️ ghst.ly/4qtl2rm

I have released an OpenGraph collector for network shares and my first blogpost at SpecterOps on the subject! You can now visualize attack paths to network shares in BloodHound 👀 specterops.io/blog/2025/10/3…