rtmcx
@rtmcx
Member of the Synack Red Team. Researcher, pentester, shellcoder and reverse engineer. OSCE|OSCP|SLAE|eCPPT|CISSP.
ID: 1670372407
14-08-2013 12:08:45
532 Tweet
902 Followers
1,1K Following

Windows rootkit development for red teaming Excellent series by Ido Veltzman Part 1: idov31.github.io/2022/07/14/lor… Part 2: idov31.github.io/2022/08/04/lor… Part 3: idov31.github.io/2022/10/30/lor… Part 4: idov31.github.io/2023/02/24/lor… #windows #driver #kernel #rootkit #redteam




Learning the basics of Linux kernel exploitation Excellent series by I write about security stuff Debugging with QEMU: blog.k3170makan.com/2020/11/linux-… Stack Overflows: blog.k3170makan.com/2020/11/linux-… RIP control: blog.k3170makan.com/2021/01/linux-… #cybersecurity #infosec #Linux #kernel

Series to learn IoT/embedded devices reverse engineering (credits Juan Carlos Jiménez) Debug Ports: jcjc-dev.com/2016/04/08/rev… Firmware: jcjc-dev.com/2016/04/29/rev… Data: jcjc-dev.com/2016/05/23/rev… Flash: jcjc-dev.com/2016/06/08/rev… Digging the Firmware: jcjc-dev.com/2016/12/14/rev… #iot




Nice short reading for anyone interested in starting with embedded/IoT devices analysis and reversing. Credits cyber wolf whiterose-infosec.super.site/mjsxj09cm-reco… #embedded #infosec



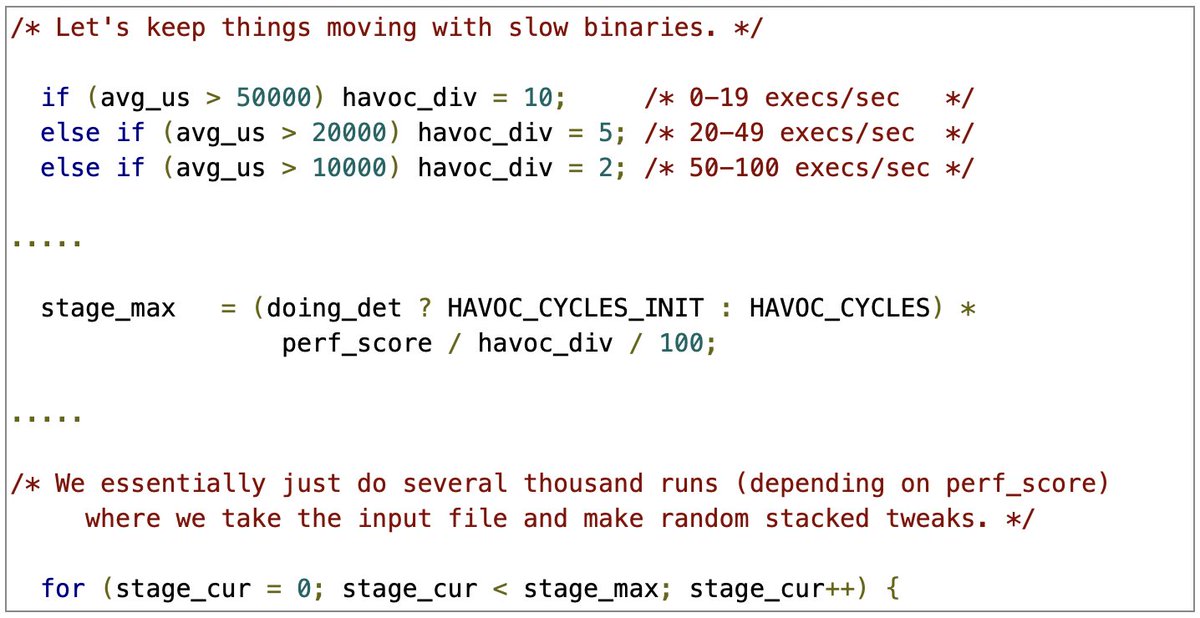
Series on fuzzing open source software using fuzzuf by Ricerca Security ricercasecurity.blogspot.com/2023/07/fuzzin… ricercasecurity.blogspot.com/2023/07/fuzzin… ricercasecurity.blogspot.com/2023/07/fuzzin… ricercasecurity.blogspot.com/2023/07/fuzzin… #fuzzing #cybersecurity

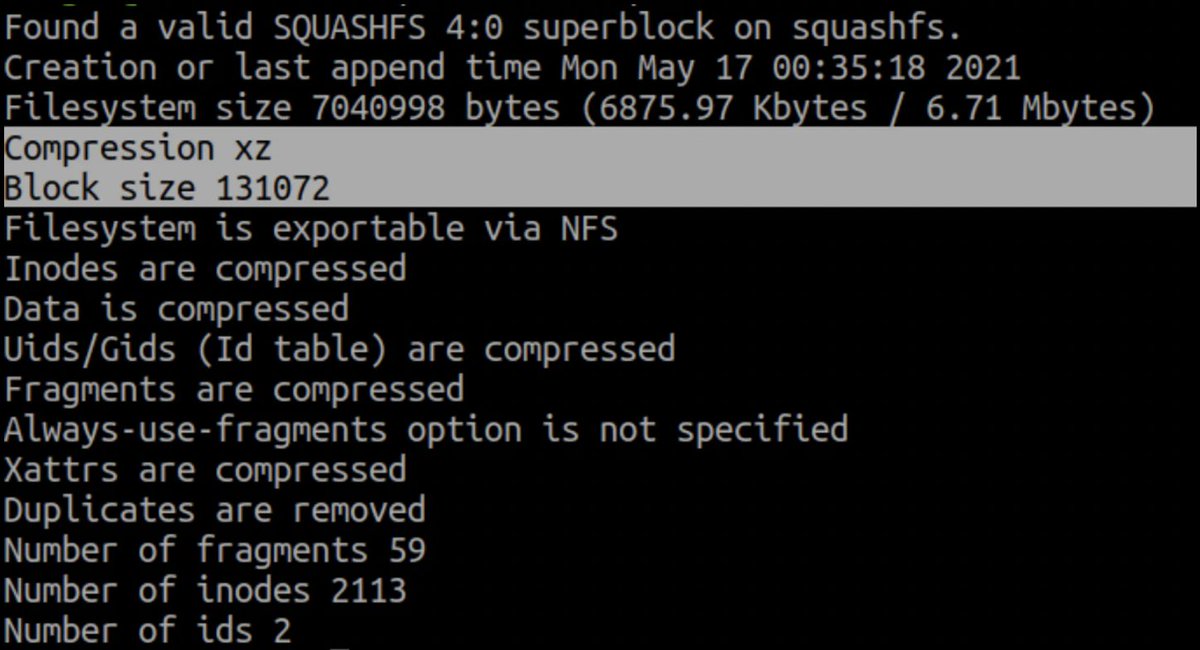
This was an excellent writeup on how to pwn WatchGuard firewalls Credits Ambionics Security web.archive.org/web/2023062813… #infosec #watchguard