Rh0
@rh0_gz
Security Research • Program Analysis • Bugs and Exploits
ID: 885860999156424704
https://rh0dev.github.io 14-07-2017 13:58:15
438 Tweet
401 Followers
366 Following






The Exploiting Reversing Series (ERS) currently features 945 pages of exploit development based on real-world targets: [+] ERS 08: exploitreversing.com/2026/03/31/exp… [+] ERS 07: exploitreversing.com/2026/03/04/exp… [+] ERS 06: exploitreversing.com/2026/02/11/exp… [+] ERS 05: exploitreversing.com/2025/03/12/exp… [+] ERS 04:
![Alexandre Borges (@ale_sp_brazil) on Twitter photo The Exploiting Reversing Series (ERS) currently features 945 pages of exploit development based on real-world targets:
[+] ERS 08: exploitreversing.com/2026/03/31/exp…
[+] ERS 07: exploitreversing.com/2026/03/04/exp…
[+] ERS 06: exploitreversing.com/2026/02/11/exp…
[+] ERS 05: exploitreversing.com/2025/03/12/exp…
[+] ERS 04: The Exploiting Reversing Series (ERS) currently features 945 pages of exploit development based on real-world targets:
[+] ERS 08: exploitreversing.com/2026/03/31/exp…
[+] ERS 07: exploitreversing.com/2026/03/04/exp…
[+] ERS 06: exploitreversing.com/2026/02/11/exp…
[+] ERS 05: exploitreversing.com/2025/03/12/exp…
[+] ERS 04:](https://pbs.twimg.com/media/HF4OLrWXIAQBjHS.jpg)











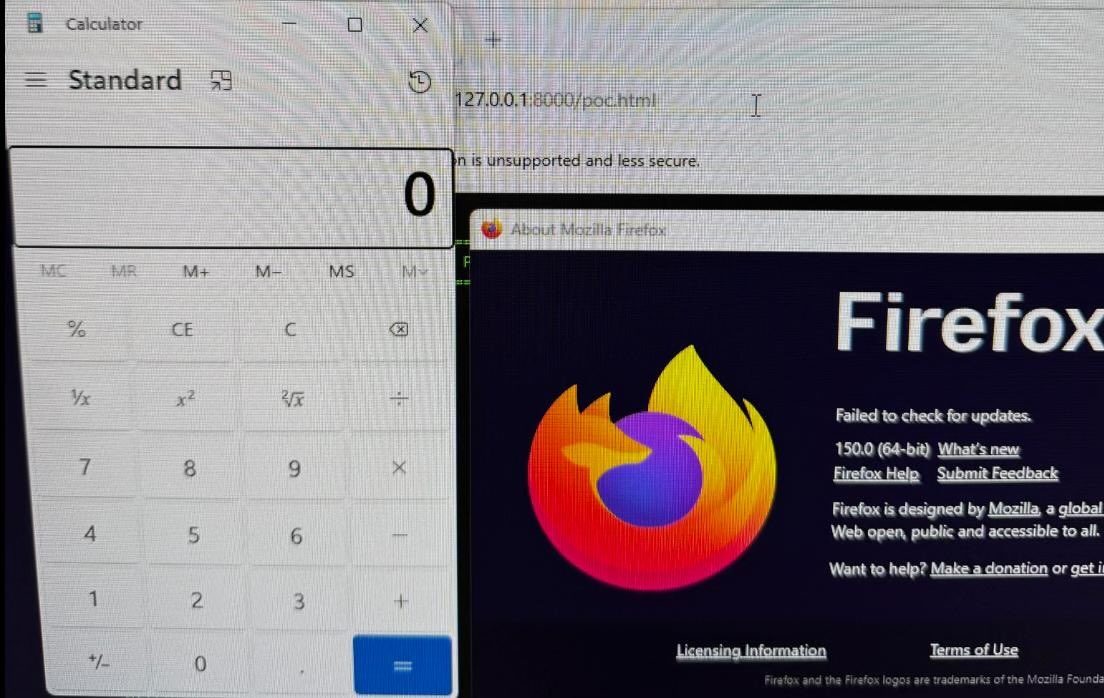
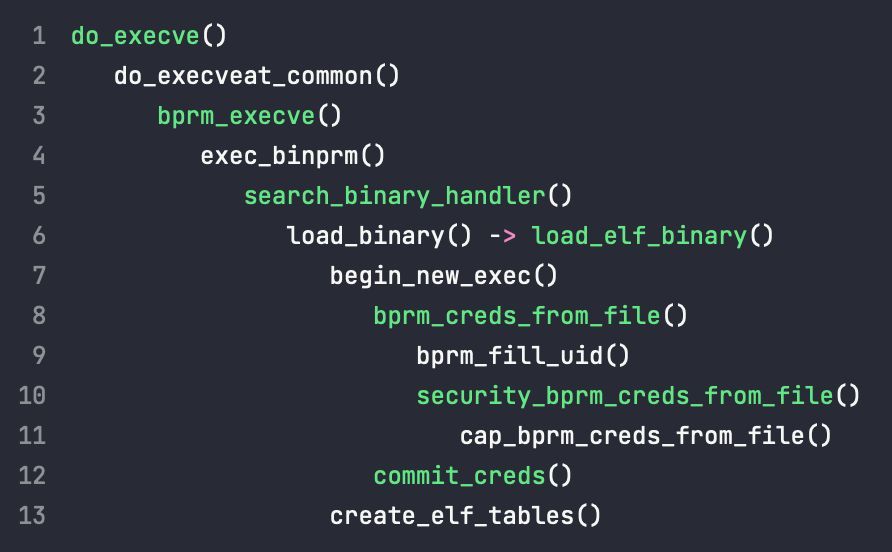
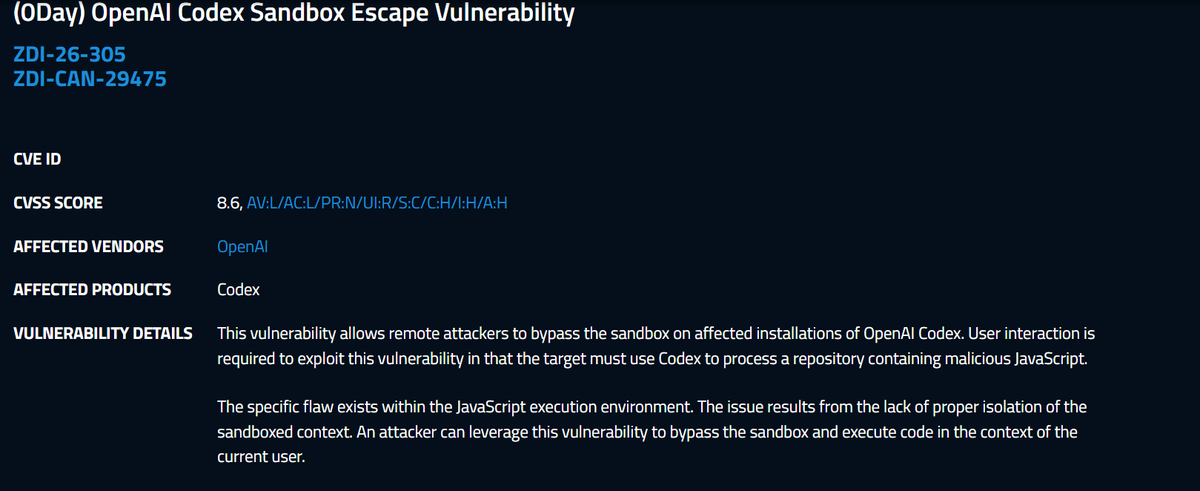
0Day OpenAI Codex Sandbox Escape Vulnerability 👀 Peter Girnus 🦅 zerodayinitiative.com/advisories/ZDI…


![xvonfers (@xvonfers) on Twitter photo 👀👀👀
(CVE-2026-6296)[$90000][490170083][ANGLE][GL]Heap-BoF
chromium-review.googlesource.com/c/angle/angle/…
Reported by <a href="/cinzinga_/">cinzinga</a> 👀👀👀
(CVE-2026-6296)[$90000][490170083][ANGLE][GL]Heap-BoF
chromium-review.googlesource.com/c/angle/angle/…
Reported by <a href="/cinzinga_/">cinzinga</a>](https://pbs.twimg.com/media/HF-uZ91XYAEF9xW.jpg)