Alton Guyton
@rarealton
ID: 3161807108
18-04-2015 02:42:53
168 Tweet
44 Followers
263 Following



CrowdStrike Sophos ESET Palo Alto Networks SentinelOne MalwareHunterTeam .SentinelOne has released an in-depth analysis of the malware and payload, they have dubbed it 'SmoothOperator'. The final payload exfiltrates data from web browsers Chrome, Edge, Brave, and Firefox. tl;dr largest data theft in history? sentinelone.com/blog/smoothope…





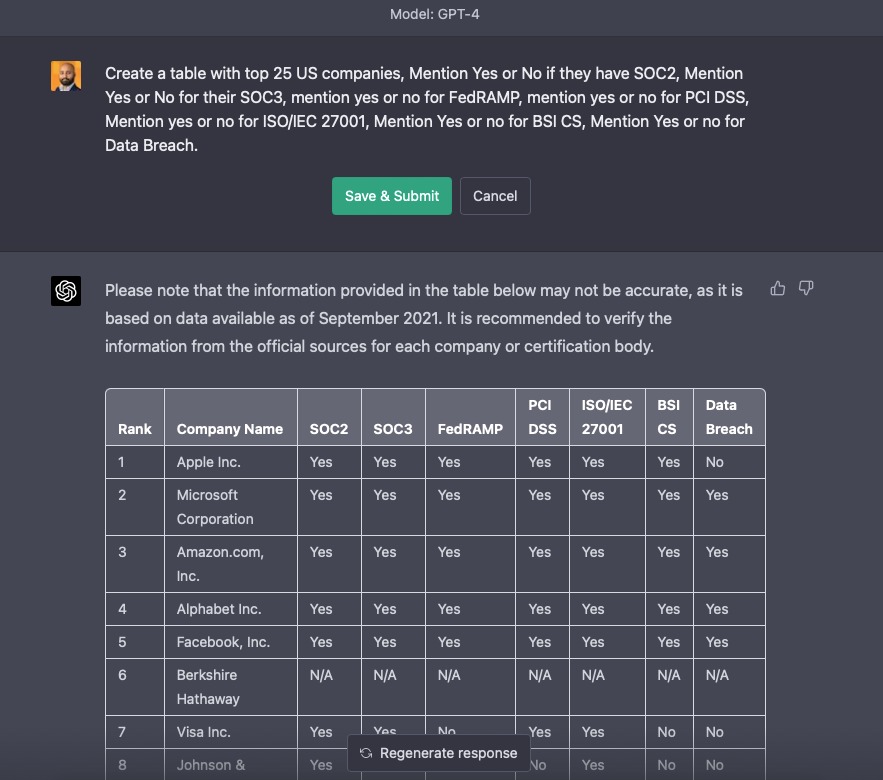
Andrew King (AJ) Create a table with top 25 US companies, Mention Yes or No if they have SOC2, Mention Yes or No for their SOC3, mention yes or no for FedRAMP, mention yes or no for PCI DSS, Mention yes or no for ISO/IEC 27001, Mention Yes or no for BSI CS, Mention Yes or no for Data Breach.



Active #Gamaredon #APT infra to track + few new domains nahalx[.]ru baraslx[.]ru 170.64.132[.]183 137.184.9[.]252 146.190.104[.]237 68.183.122[.]121 195.133.88[.]63 178.128.53[.]132 143.244.184[.]231 164.92.96[.]103 195.133.88[.]49 Mikhail Kasimov 匚ㄚ乃乇尺ㄖᐯ乇尺ㄥㄖ卂ᗪ ET Labs




You all know this had to happen 😜 Doom on the Kali Linux NetHunter TicWatch Pro 3 Mobvoi_Official Christian B. TimInBrum


![SOS Intelligence (@sosintel) on Twitter photo If anyone wants the unredacted Genesis Market Onion genesis7zoveavupiiwnrycmaq6uro3kn5h2be3el7wdnbjti2ln2wid[.] onion #GenesisMarket If anyone wants the unredacted Genesis Market Onion genesis7zoveavupiiwnrycmaq6uro3kn5h2be3el7wdnbjti2ln2wid[.] onion #GenesisMarket](https://pbs.twimg.com/media/Fs-TuWcWYA4_P8x.jpg)
![LeakIX (@leak_ix) on Twitter photo 🚨 Cisco Implant traffic detected from 192.3.101[.]111 .
Looking for DNS settings, likely to ID targets. 🚨 Cisco Implant traffic detected from 192.3.101[.]111 .
Looking for DNS settings, likely to ID targets.](https://pbs.twimg.com/media/F9i2VcWXsAAAbUu.png)