pubSubZero
@pubsubzero1
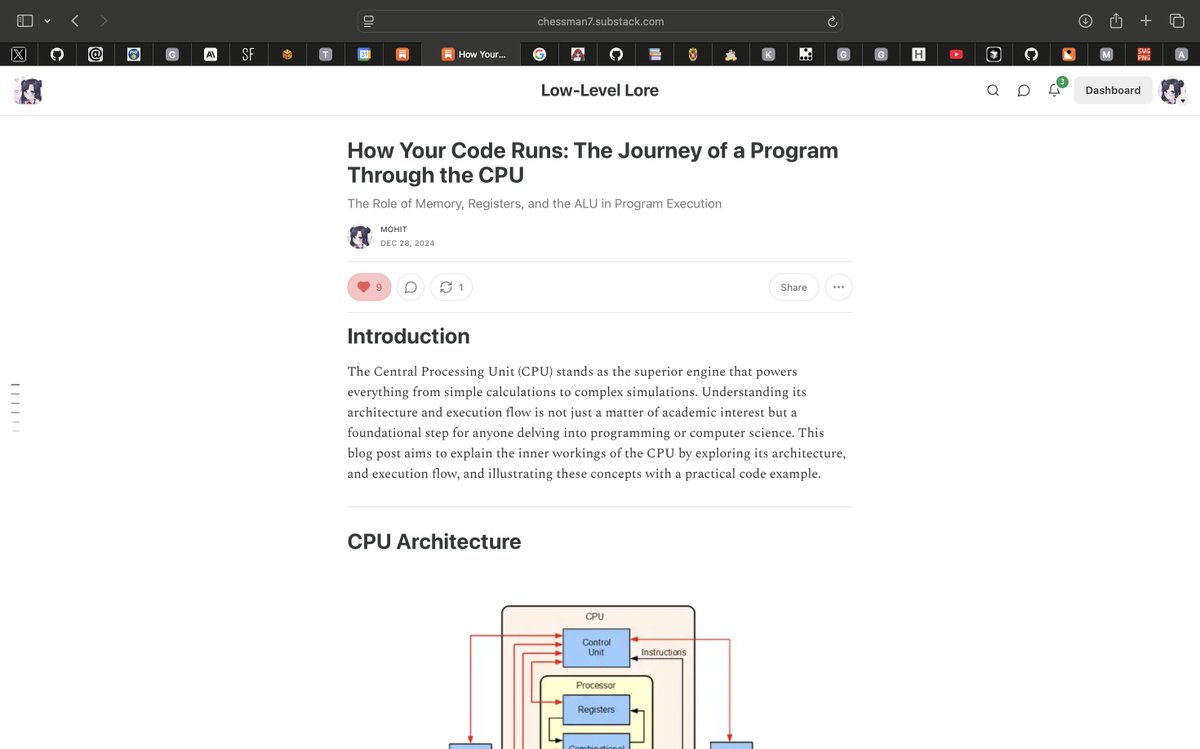
ID: 1276454607149907970
26-06-2020 09:58:09
3,3K Tweet
261 Followers
3,3K Following












Intercepting HTTPS Communication in Flutter using Frida sensepost.com/blog/2025/inte… Credits Jacques Coertze (Orange Cyberdefense's SensePost Team) #infosec














![Linux Kernel Security (@linkersec) on Twitter photo [CVE-2025-37752] Two Bytes Of Madness: Pwning The Linux Kernel With A 0x0000 Written 262636 Bytes Out-Of-Bounds
Great article by D3vil about exploiting a type confusion in the network scheduler subsystem and pwning all kernelCTF instances.
syst3mfailure.io/two-bytes-of-m… [CVE-2025-37752] Two Bytes Of Madness: Pwning The Linux Kernel With A 0x0000 Written 262636 Bytes Out-Of-Bounds
Great article by D3vil about exploiting a type confusion in the network scheduler subsystem and pwning all kernelCTF instances.
syst3mfailure.io/two-bytes-of-m…](https://pbs.twimg.com/media/Gq2y432XIAAk3rD.png)