NetFiT.eth
@onnetfit
Web2 Bug Hunter|Red Team|Web3.0 Scientists|21-year-old | 微信公众号:不懂安全的校董 |Bilibili:不懂安全的校长
ID: 1084124163818704896
http://x.com/logout?redirect_after_logout=https://baidu.com 12-01-2019 16:25:17
518 Tweet
544 Followers
1,1K Following







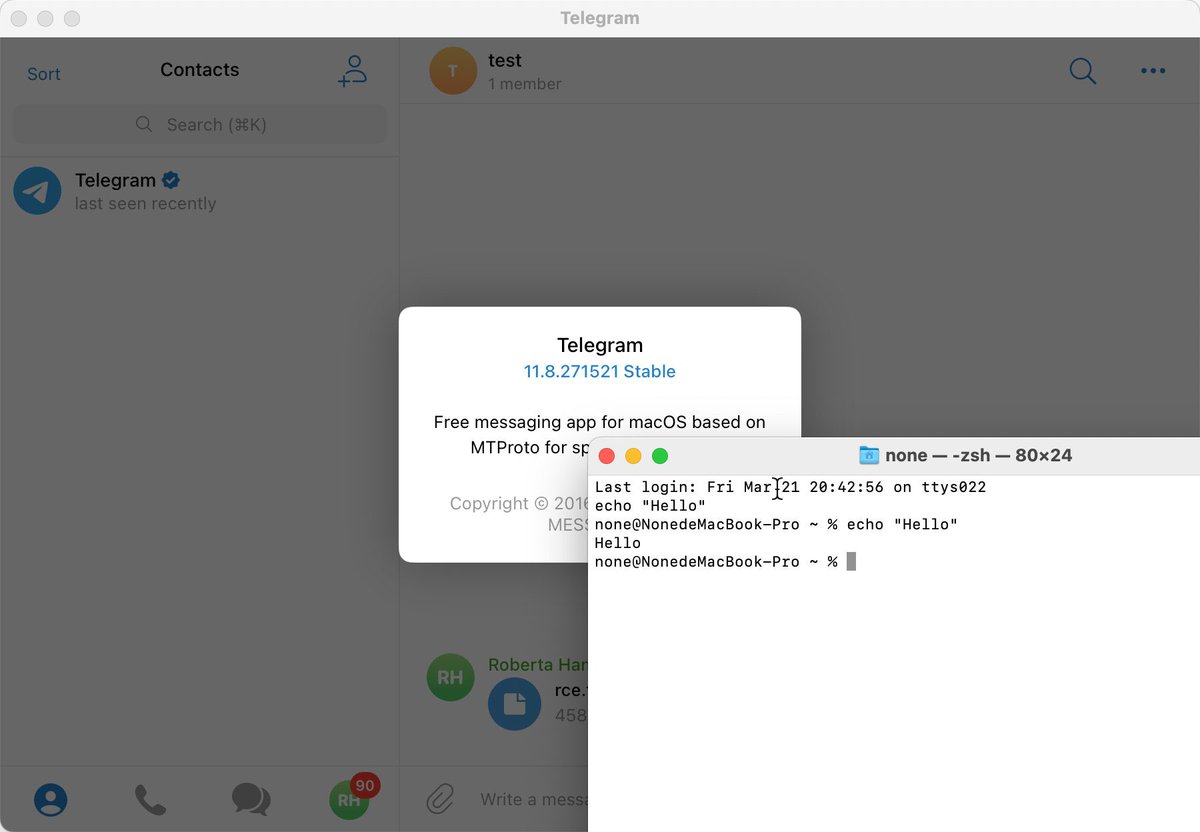
Telegram has a super serious bug, click on the file is hacked mp.weixin.qq.com/s/RiFgghK96QN-… #telegram #web3 Telegram Messenger #0day





New tool drop by Oli (C..1..P.H.Y)! 🛠️ SQLTimer is a simple, blazing-fast tool to scan for time-based SQL injections! 😎 Check it out! github.com/c1phy/sqltimer








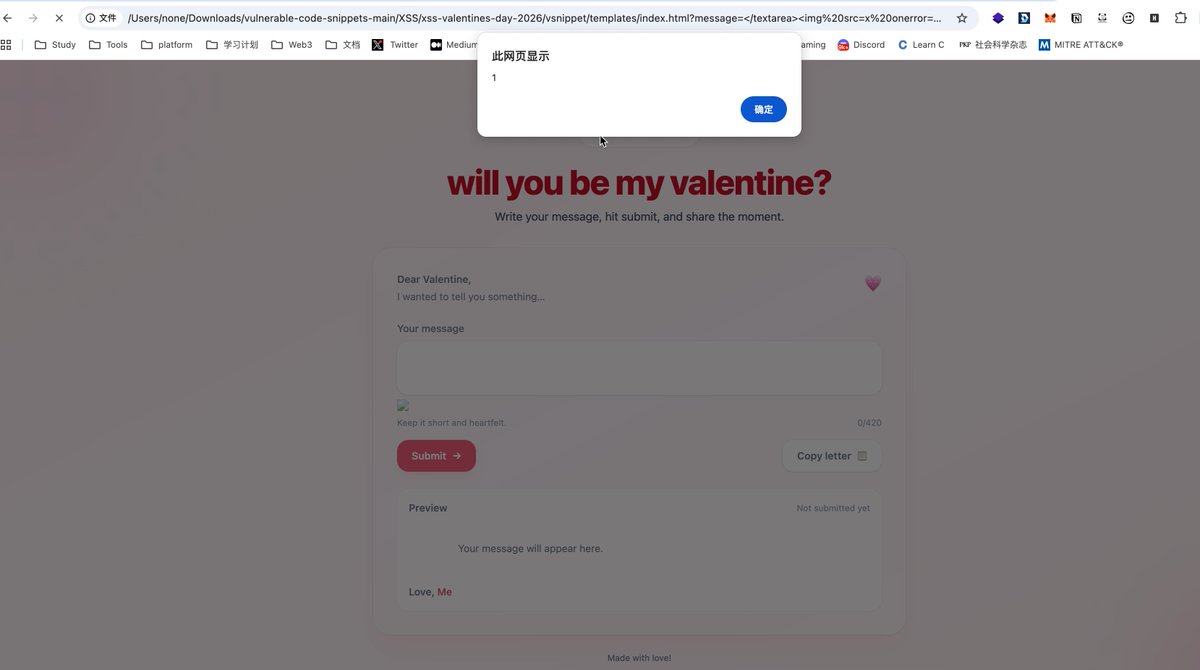
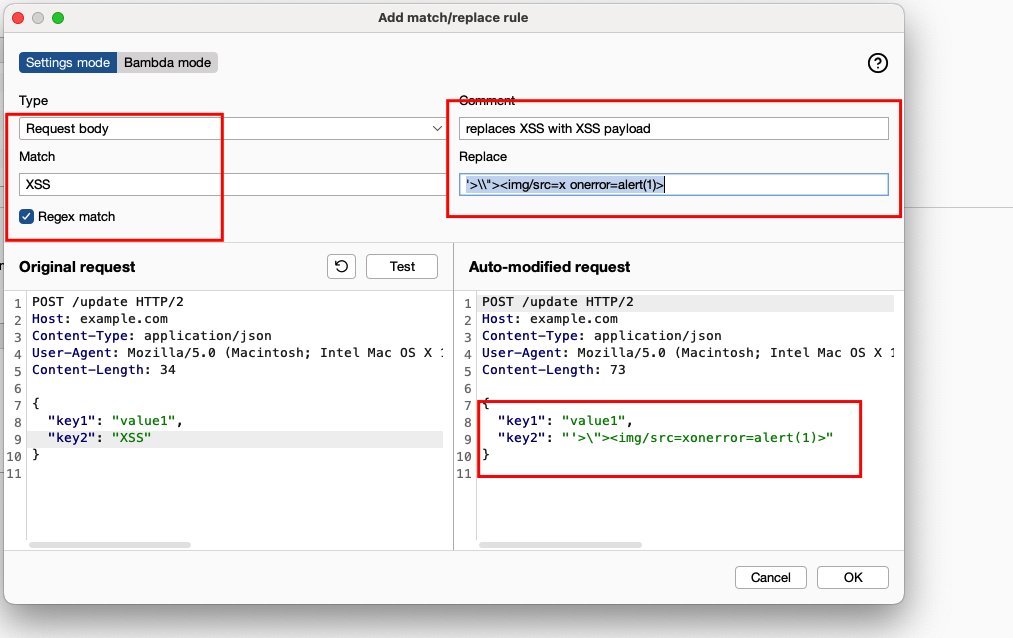
脚本通过 URLSearchParams 直接从当前 URL 获取名为 message 的参数值。这个值是用户完全可控的,并且没有经过任何清洗或过滤。 payload:index.html?message=</textarea><img%20src=x%20onerror=alert(1)> YesWeHack ⠵