Adam
@malworms
IDA pro enthusiast, malware reverser, addicted to Rocket League.
@PwC_uk Threat Intelligence.
All views my own.
ID: 1295312859111600133
17-08-2020 10:54:55
44 Tweet
293 Followers
62 Following






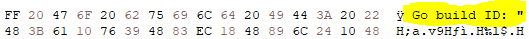
extra - IDA determines if a binary is Golang or not only by the presence of the Go build string. The build string does not need to be correctly formed, just finding space in the .text section with enough CC alignment and pasting that string in lets IDA work properly Hex-Rays SA

For anyone interested in some #ShadowPad research- pwc.co.uk/issues/cyber-s… github.com/PwCUK-CTO/Scat… Takes a deep dive into the #ScatterBee (aka #ShadowShredder, #PoppingBee) packing mechanism used by some ShadowPad variants and has scripts to enable static analysis of the payloads







The Banshee Queen👑 PwC ATT&CK Richard Ackroyd eral4m We're hiring for our #detectionengineering team. If you would like to join the team that helped produce this annex, the main report, and does so much more, then visit experiencedcareers.pwc.co.uk/job/14249418/e…



We've got TWO roles open in Australia! Looking for both tech and strat threat intel analysts. Come work with all the awesome folks on the #pwc TI team. Bonus: Witness firsthand the epic banter between me and Jason Smart. jobs-au.pwc.com/experiencedhir… jobs-au.pwc.com/experiencedhir…