Monish
@m0n1x90
Security Researcher
ID: 1029073940868546560
http://m0n1x90.dev 13-08-2018 18:35:21
1,1K Tweet
600 Followers
722 Following


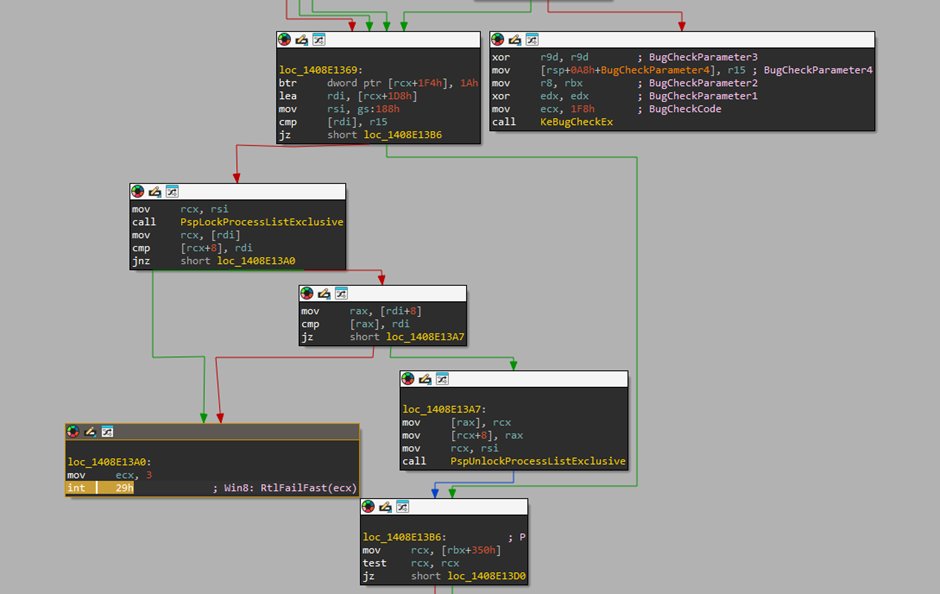
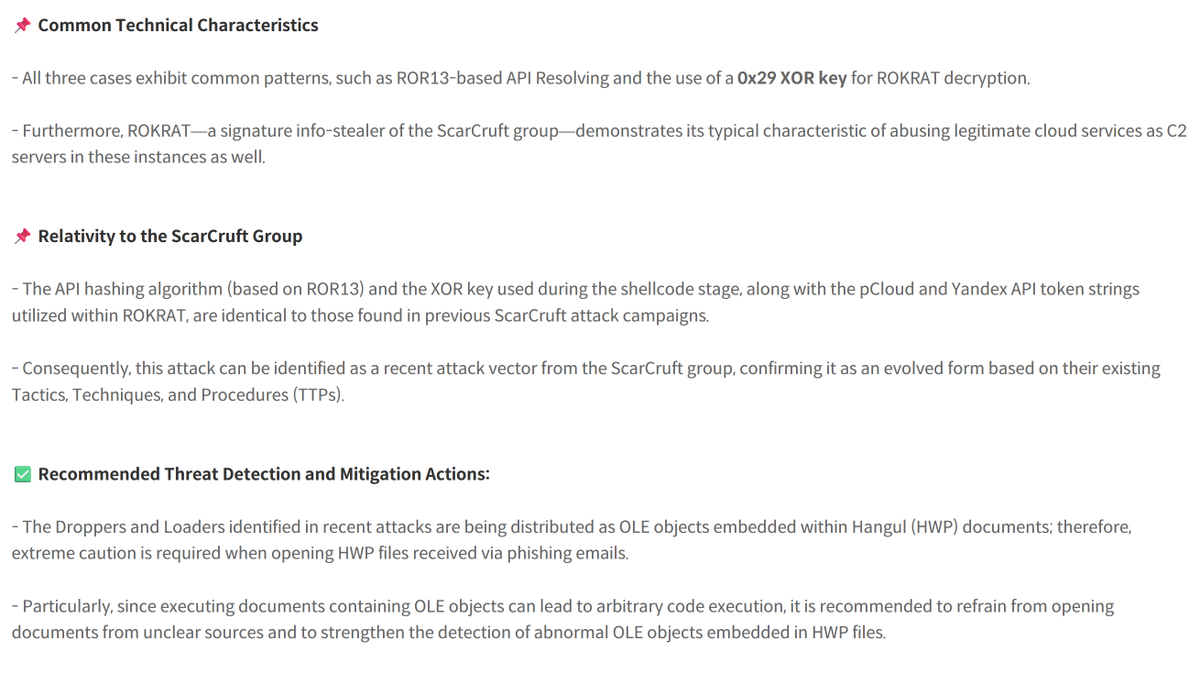
THE CHINESE GOVERNMENT USED MICROSOFT WARBIRD APIS FOR OBFUSCATION > proof-of-concept by Michael B. in 2023 > 30 stars on GitHub > 62 likes on Xitter This is fucking FIRE research. Insanely slept on research. I am FLABBERGASTED.