Jonathan Lusky
@luskyyehonatan
Security research team lead at Cellebrite. I love anything related with low-level security research, poking CPUs, hopping between rings and destroying hardware
ID: 1526912886399975426
18-05-2022 13:09:47
26 Tweet
63 Followers
87 Following


I guess now would be great opportunity for an hello world tweet :) Thank you for hopping in to our talk, we "hopped" you enjoyed it! BlueHat IL Benny Zeltser #RingHopper #UEFI #SMM
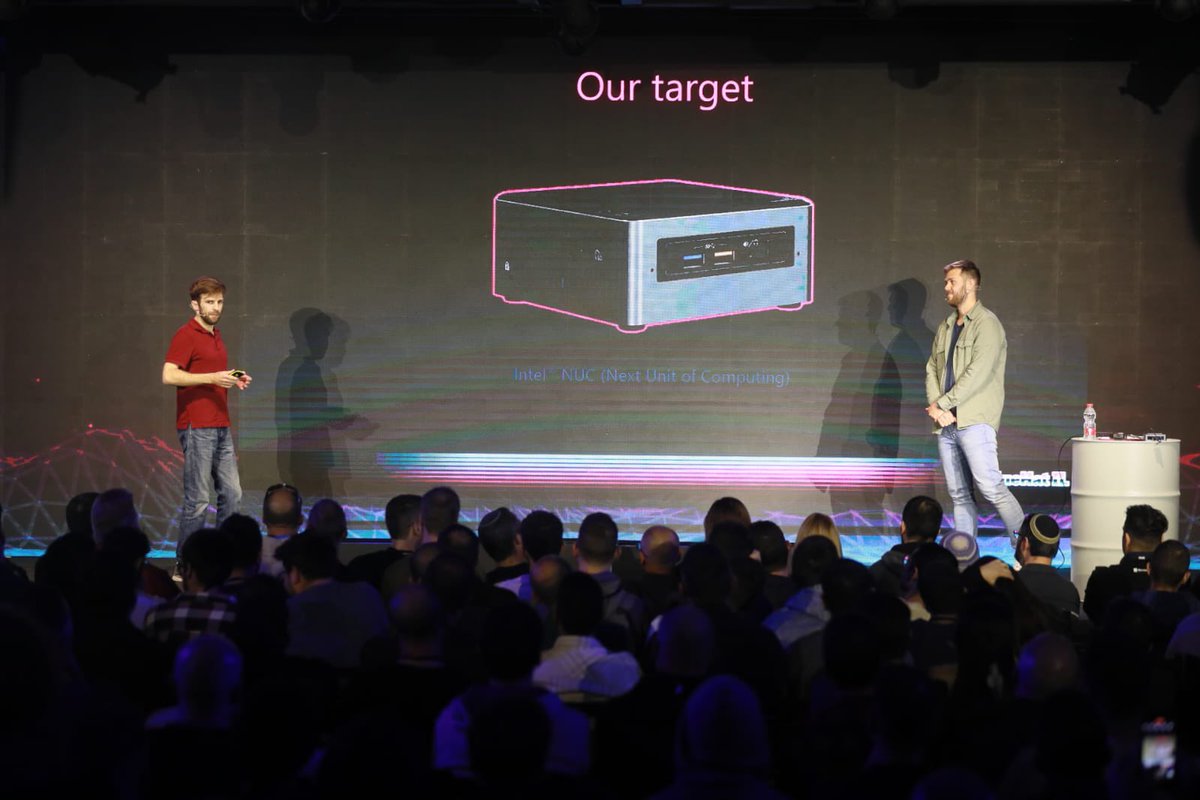
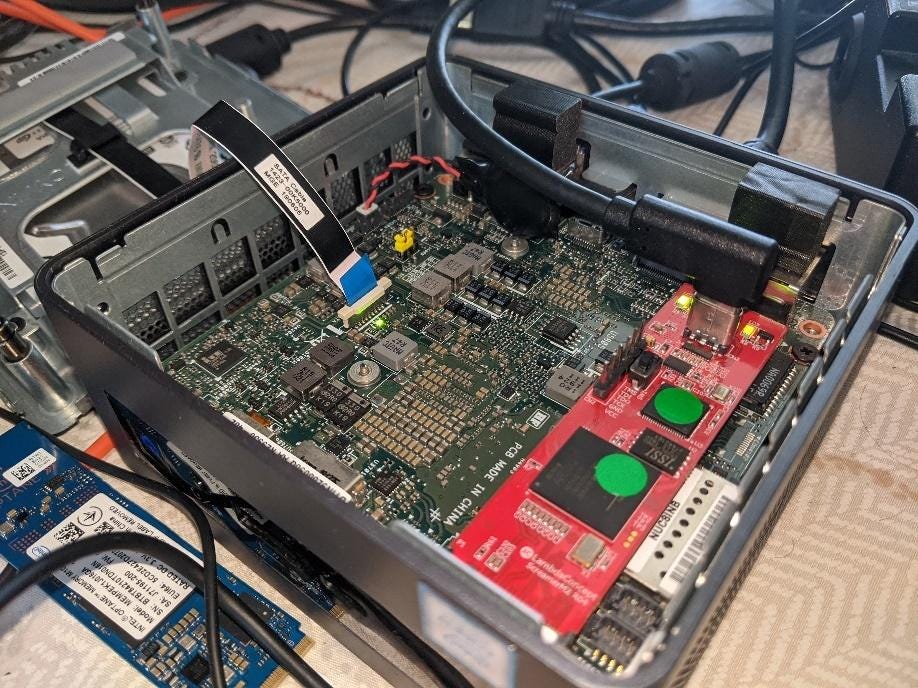
Jonathan Lusky and I submitted our talk "The #RingHopper Journey: Hopping through the maze of SMM exploitation" where we delve into the realm of SMM exploitation and talk extensively about the journey, rather than only the destination. Fingers crossed we get to deliver this talk

Our talk from BlueHat IL is live! youtube.com/watch?v=CJDv_b… In our live demo on stage, we hopped from user-space to SMM modifying the BIOS logo 😎 Benny Zeltser #RingHopper #UEFI

2023-03-29 "RingHopper – Hopping from User-space to God Mode" Slides: msrndcdn360.blob.core.windows.net/bluehat/blueha… Video: youtube.com/embed/CJDv_bcI… By Jonathan Lusky & Benny Zeltser Added to darkmentor.com/timeline.html


Bug bounties are broken - the story of "i915" bug, ChromeOS + Intel bounty programs, and beyond Google VRP (Google Bug Hunters) Intel Security How the unspoken problems of bug bounties can be addressed? "Imbalance of Power" is a real problem and it should be changed. blog.pi3.com.pl/?p=931



📢 Super thrilled to announce that our #RingHopper talk presented @ #DefCon31 is now LIVE on YouTube! 🎉📺 If you want to dive even deeper into the details of our research, check out our awesome blog post series too! medium.com/@RingHopper/em… 📚🔍 Jonathan Lusky

Just released the third blog in our #RingHopper series! 📝 Dive in as we showcase the transformation of a seemingly weak write primitive into unauthorized code execution in SMM 💻🔒 medium.com/@RingHopper/br… Jonathan Lusky
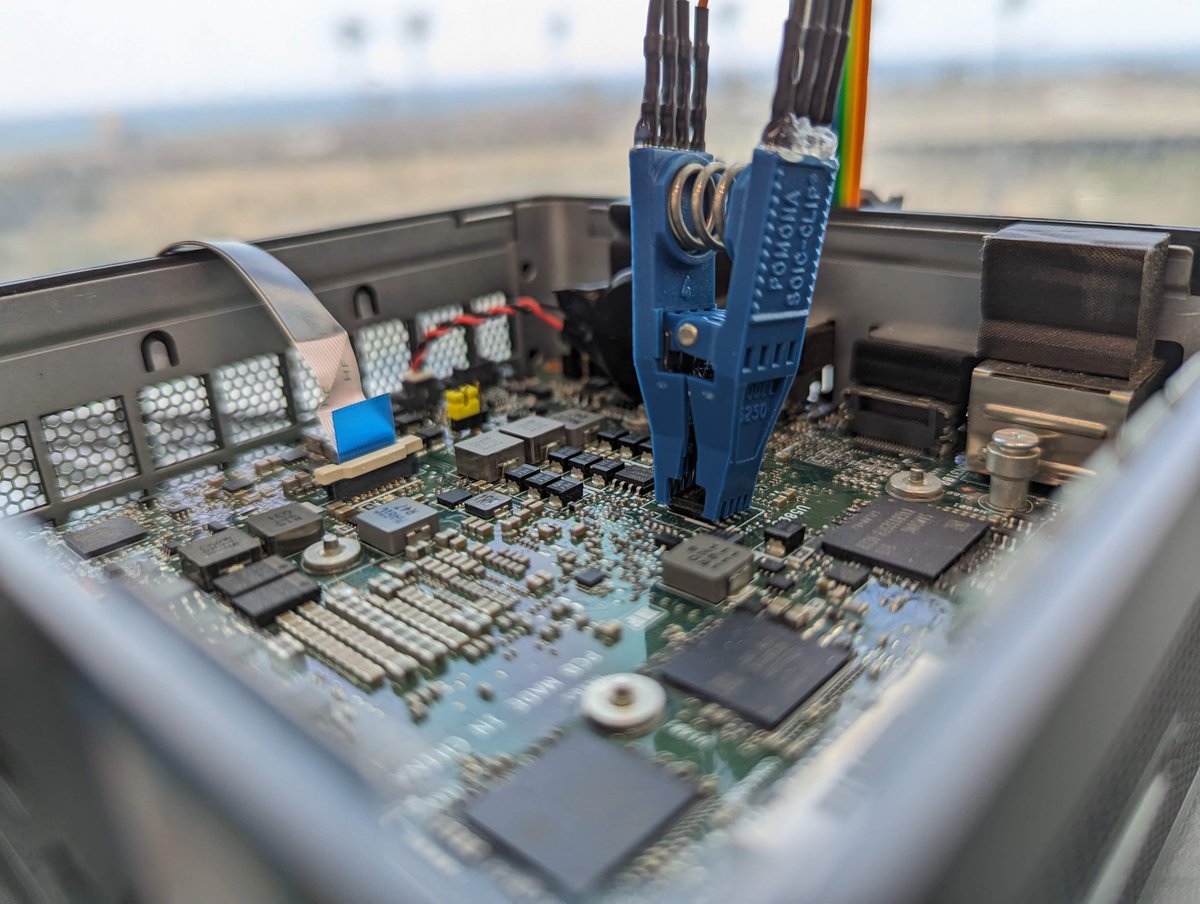
📢 Just dropped the fourth and final blog post in the #RingHopper saga! In this post, we elevated the attack to operate from user-land and thus, managed to hop from Ring 3 to SMM. Explore the details in our latest post here: medium.com/@RingHopper/co… ⭕🦗 Jonathan Lusky


Is remote code execution in UEFI firmware possible? Yes it is. Meet #PixieFAIL: 9 vulnerabilities in the IPv6 stack of EDK II, the open source UEFI implementation used by billions of computers. Full details by Francisco Falcon and iarce in our new blog post: blog.quarkslab.com/pixiefail-nine…