
Wayne
@kprobes
Threat Intelligence - Detection Engineering
ID: 322589994
23-06-2011 12:32:40
390 Tweet
165 Takipçi
421 Takip Edilen


I've released a new post on F-Secure Labs that considers persistence using calendar alerts on macOS. This builds on some awesome prior work by Andy Grant, and can now be executed using Cody Thomas 's Mythic framework.




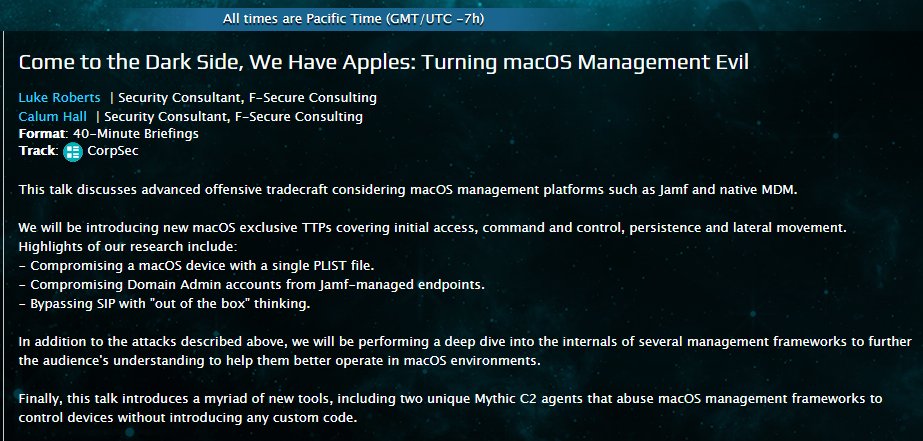
\o/ Looking forward to presenting this with Calum Hall in August at BlackHat USA 2021. It's going to be a good one!

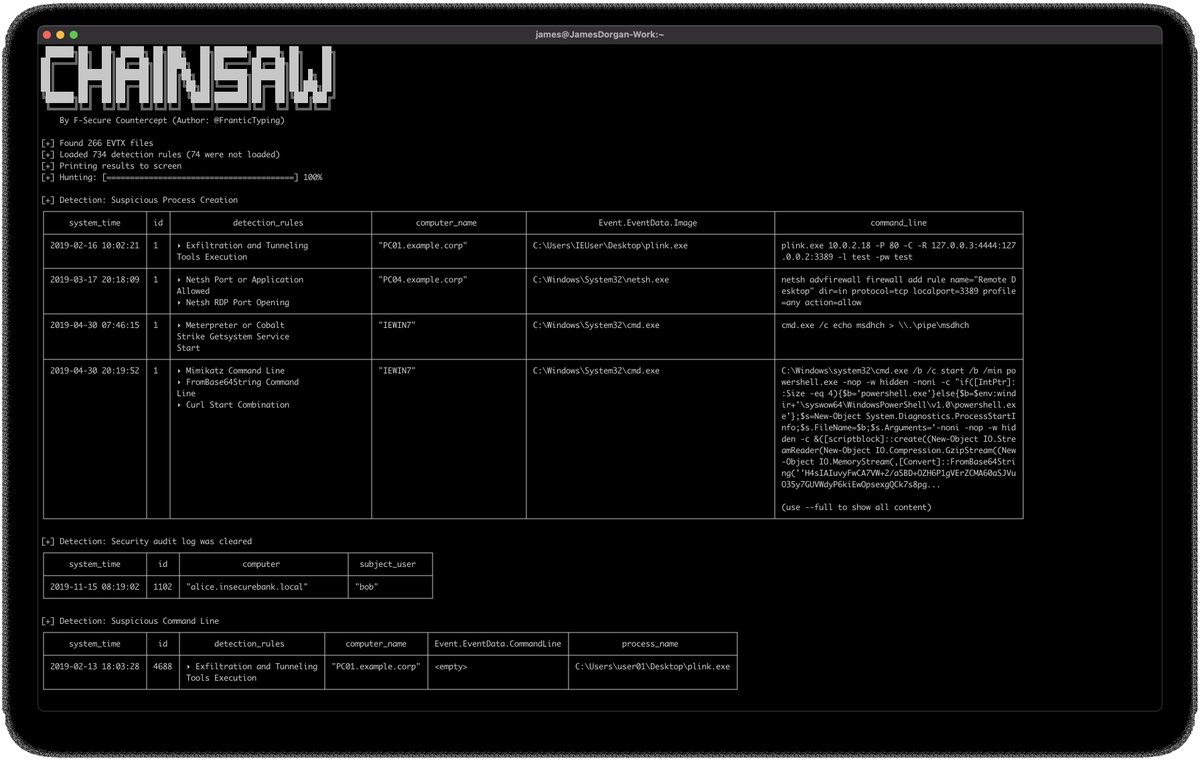
I'm excited to release a tool that I wrote at F-Secure Countercept to help triage Windows event logs. Chainsaw is a RUST CLI tool to quickly search and hunt through event logs. It supports sigma detection rules to identify potential threats. More info here: github.com/countercept/ch…


Join @Lavi161 at AISA National as he discusses #UEFI variable runtime manipulation persistence techniques, and detection and monitoring methods. This is going to be a good one. Register to book your seat now >> cyberconference.com.au/program-virtua…








My #BlueHat talk "The new SaaS cyber kill chain" has finally dropped! If you didn't make it to Seattle last month, check it out on youtube along with all the talks. Microsoft BlueHat thanks again for having me! youtu.be/pdDzUTFVIZc?si…


