James D
@frantictyping
Threat Hunting | Detection Engineering | Defensive Automation (ex @Countercept, @mwrlabs)
ID: 14573968
http://blog.securehat.co.uk 28-04-2008 19:33:15
390 Tweet
821 Followers
446 Following






Check out the first post in my new blog series "On Detection: From Tactical to Functional". The first post explores how we can leverage source code to discover which API Functions an attack tool is using which serves as a base for further investigation. posts.specterops.io/on-detection-t…


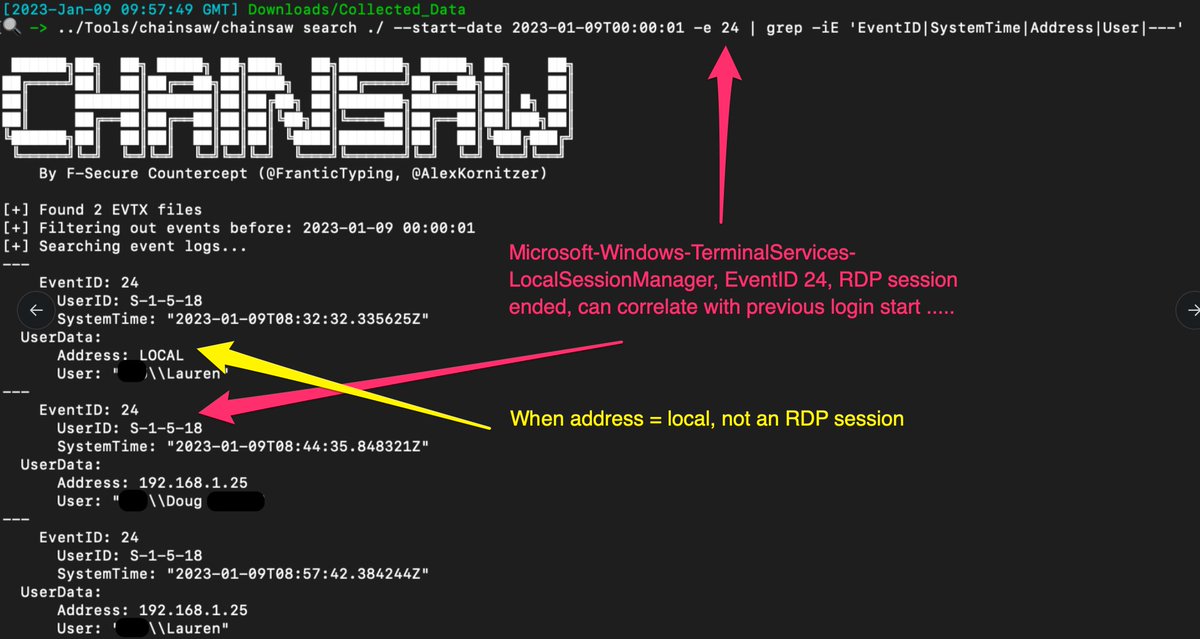
Hunt, search, and extract Windows event log records with Chainsaw, now in #toolsmith 148. Experiments with an old #DFIR malware case, as well as APT Simulator. The saw is the law! Alex Kornitzer James D sigma Florian Roth ⚡️ holisticinfosec.io/post/chainsaw/


Our team at Elastic has been developing this feature for almost six years and we are excited to share our work with the security research community. Thanks to Gabriel Landau William Burgess and many others who have contributed to this effort over the years!

Awesome to see this new feature being added to chainsaw! Great work Alex Kornitzer @56616C6F72 💪