Michael Kajiloti
@kajilot
Research, Security, Malware, Cryptocurrency.
Apparently a drunk rock.
ID: 825432141009936384
28-01-2017 19:55:33
79 Tweet
448 Followers
94 Following

My first blog with ESET Research is up documenting a cyber-espionage toolkit we called Ramsay, likely designed to spread within air-gapped networks via a file-based protocol and parasitic file infection. Some overlaps with #DarkHotel's Retro were found. x.com/ESETresearch/s…

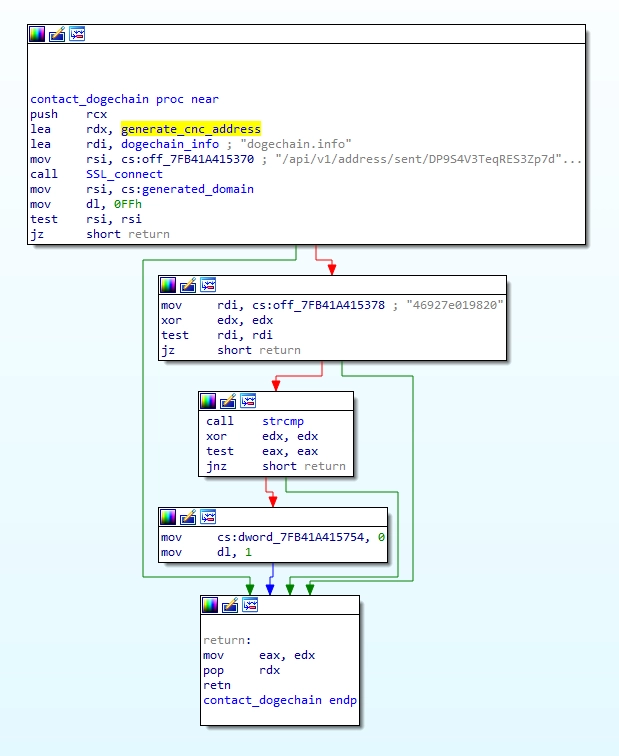
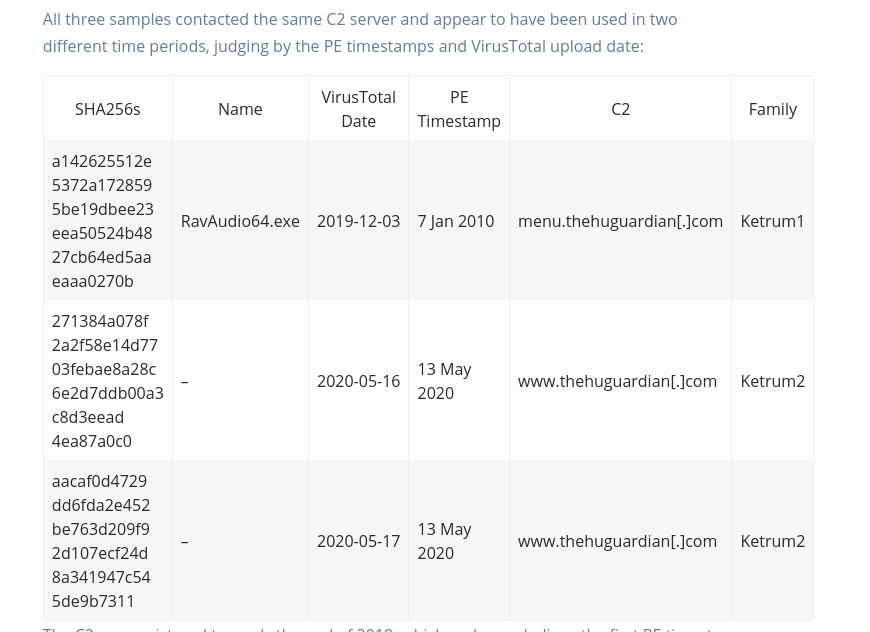
My new blog post about continued Ke3chang (APT15 🇨🇳) tool changes in 2020 and their new "Ketrum" tools. intezer.com/blog/research/… Zuzana Hromcova was very helpful with her previous documentation of the group's activities in 2019.


[1/3] 🆕 Linux version of #Lazarus's #ManusCrypt variant F. Its PE version was reported by the Follow CISA's accounts: @CISAgov and @CISACyber in May 2020 analyze.intezer.com/#/analyses/fb5… ->>
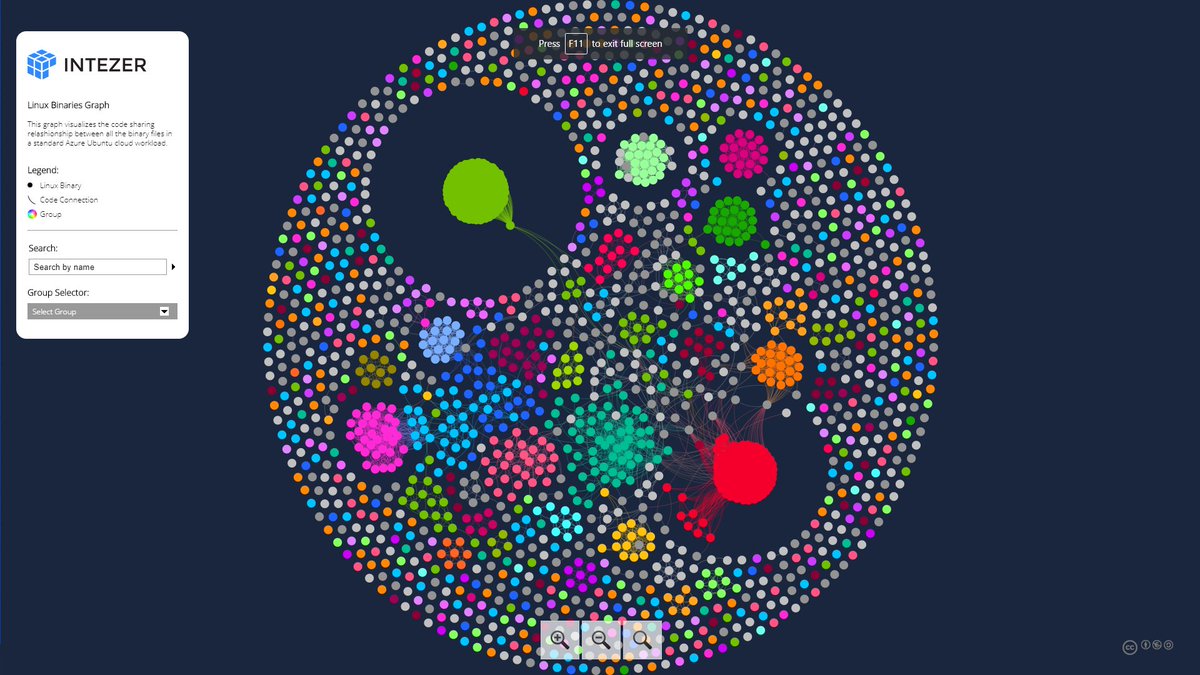
![Intezer (@intezerlabs) on Twitter photo [1/3]
🆕 Linux version of #Lazarus's #ManusCrypt variant F. Its PE version was reported by the <a href="/USCERT_gov/">Follow CISA's accounts: @CISAgov and @CISACyber</a> in May 2020
analyze.intezer.com/#/analyses/fb5…
->> [1/3]
🆕 Linux version of #Lazarus's #ManusCrypt variant F. Its PE version was reported by the <a href="/USCERT_gov/">Follow CISA's accounts: @CISAgov and @CISACyber</a> in May 2020
analyze.intezer.com/#/analyses/fb5…
->>](https://pbs.twimg.com/media/EapNGu5X0AAQ5aQ.png)










🚨 Apple released security updates for multiple devices. Of these, 5 vulnerabilities in AirPlay were reported by the Oligo Security research team.