Josh Stroschein | The Cyber Yeti
@jstrosch
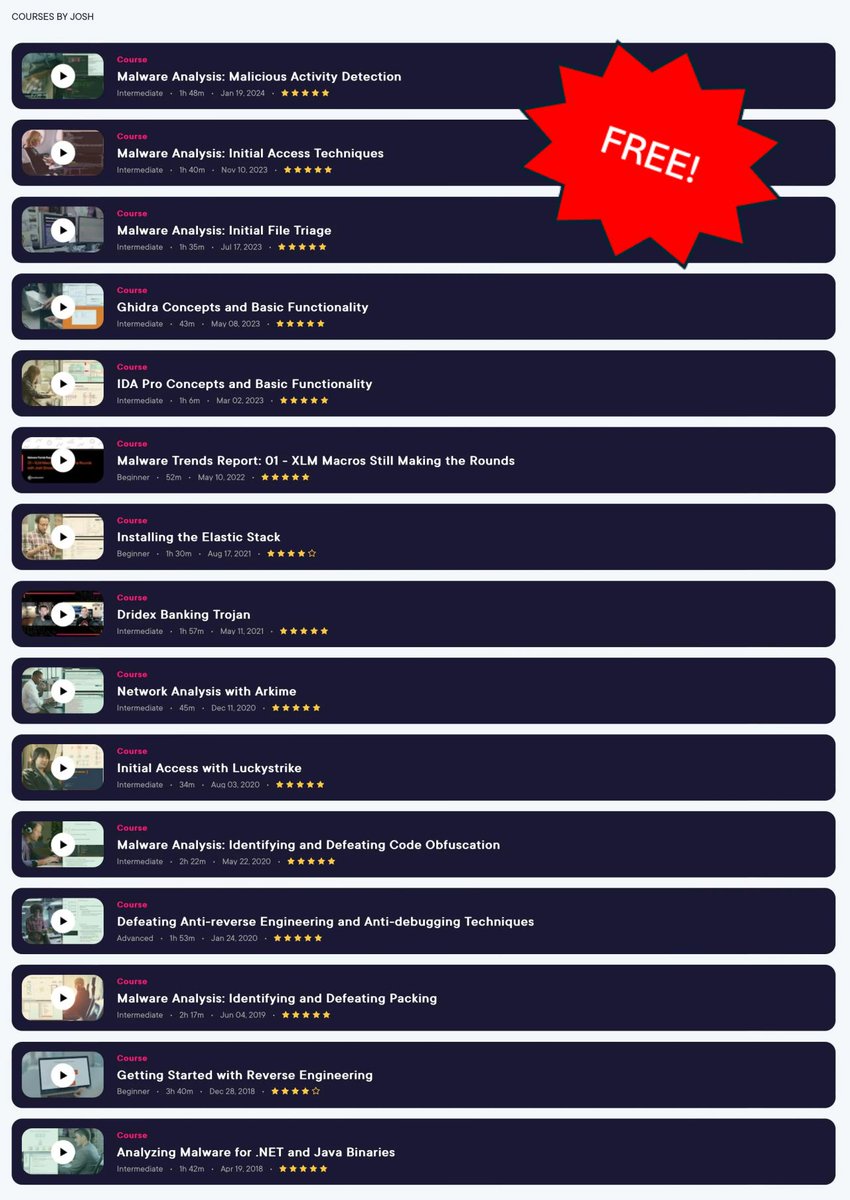
Reverse engineer at FLARE/@Google | @pluralsight author | 700K+ views on YT 😱 Find FREE resources below👇
ID:53809084
https://thecyberyeti.com 05-07-2009 01:40:42
3,9K Tweets
8,7K Followers
971 Following





Unraveling Not AZORult but Koi Loader: A Precursor to Koi Stealer
Did some analysis on #KoiLoader which ultimately led to #KoiStealer . Warning ⚠️It is not AZORult.
The blog: esentire.com/blog/unravelin…
eSentire Threat Intel




Google CEO lookalike and master instructor 🐘 @[email protected] will teach The ARM IoT Exploit Laboratory, a virtual Ringzer0 course this July: ringzer0.training/doubledown24-a…




🦔 📹 New Video: D3fack loader analysis
➡️ Inno Setup pascal script analysis
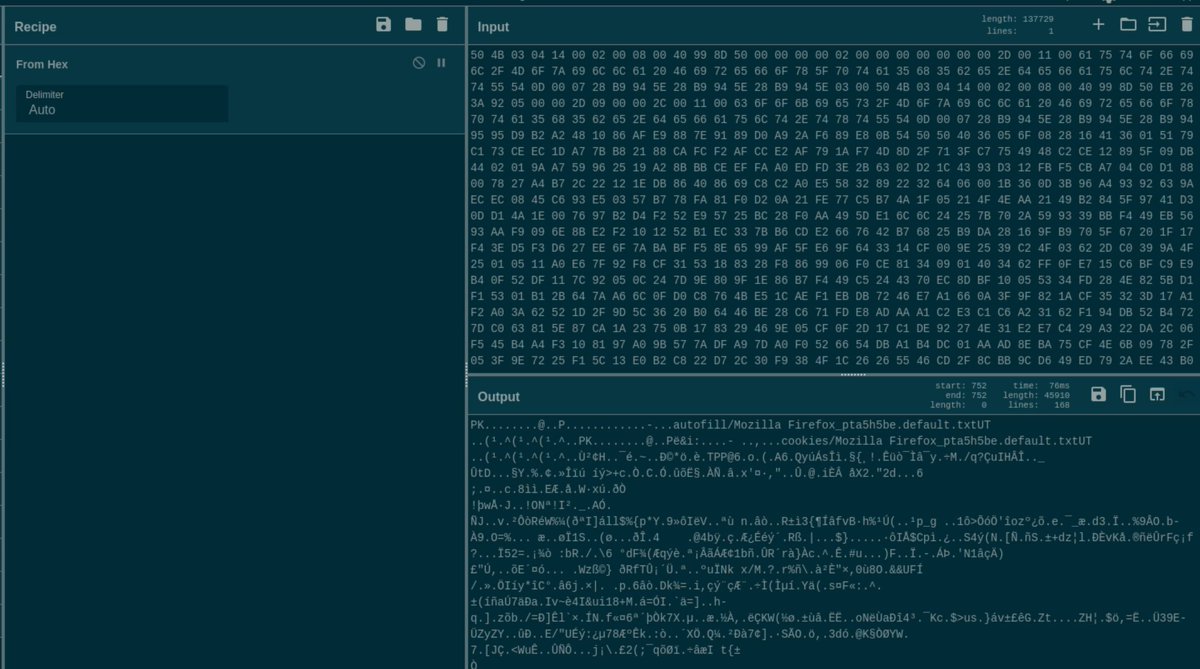
➡️ string deobfuscation with binary refinery
➡️ JPHP decompilation
Sample was first described by RussianPanda 🐼 🇺🇦
youtube.com/watch?v=y09Zre…
#MalwareAnalysisForHedgehogs #D3fackLoader


Hi all, If you are struggling with inline decryption and C++ triage, I wrote a brief article, using #emulation and a quite recent #GlorySprout sample. Hope someone will find it an inspiring reading: shorturl.at/teq6W