herrcore
@herrcore
UnpacMe | OALABS
ID:43022669
http://www.openanalysis.net/ 28-05-2009 02:03:24
8,1K Tweets
11,9K Followers
475 Following



Ever wonder what is buried in a 10 year old file infector? What files has it collected over the years?
Join us at 1300 EST today and find out!
#OALabsLive
#SundaySandboxCentipede





Since it is back in the news here is some info on SmartLoader that mysterious LUA malware...
The name SmartLoader comes from the UserAgent string used in early builds of the malware (cc Who said what), the true name is currently unknown.
There are at least two different versions of…



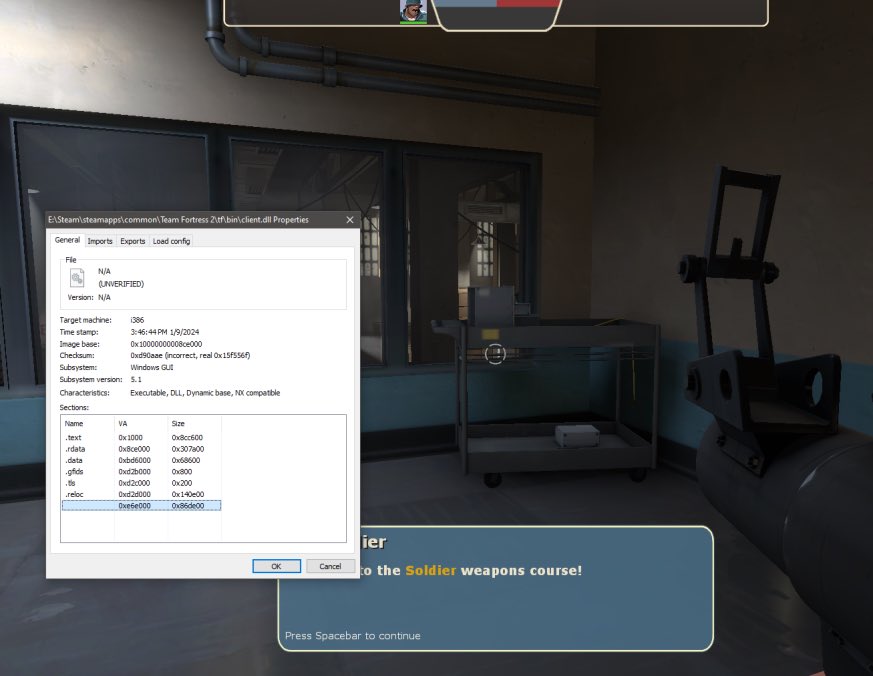
Daniel Mayer herrcore Vector 35 Josh Reynolds (jmag) Binary Ninja’s strengths are its API (especially when accessing the decompiler) and its headless mode (sadly that’s only in the commercial version.) Here is a cheat sheet for binary ninja I created a while back.
gist.github.com/alexander-hane…







Source: They’re building a next-gen obfuscator suitable for modern binaries Back Engineering Labs. They can do binary-to-binary translation of Windows kernel, CSGO, Chromium, Hyper-V, while respecting CFG, ACG, CET