Jaeho Jeong
@jeongzero
Security researcher @78_lab
ID: 1461220572252483584
18-11-2021 06:32:07
3 Tweet
20 Followers
94 Following

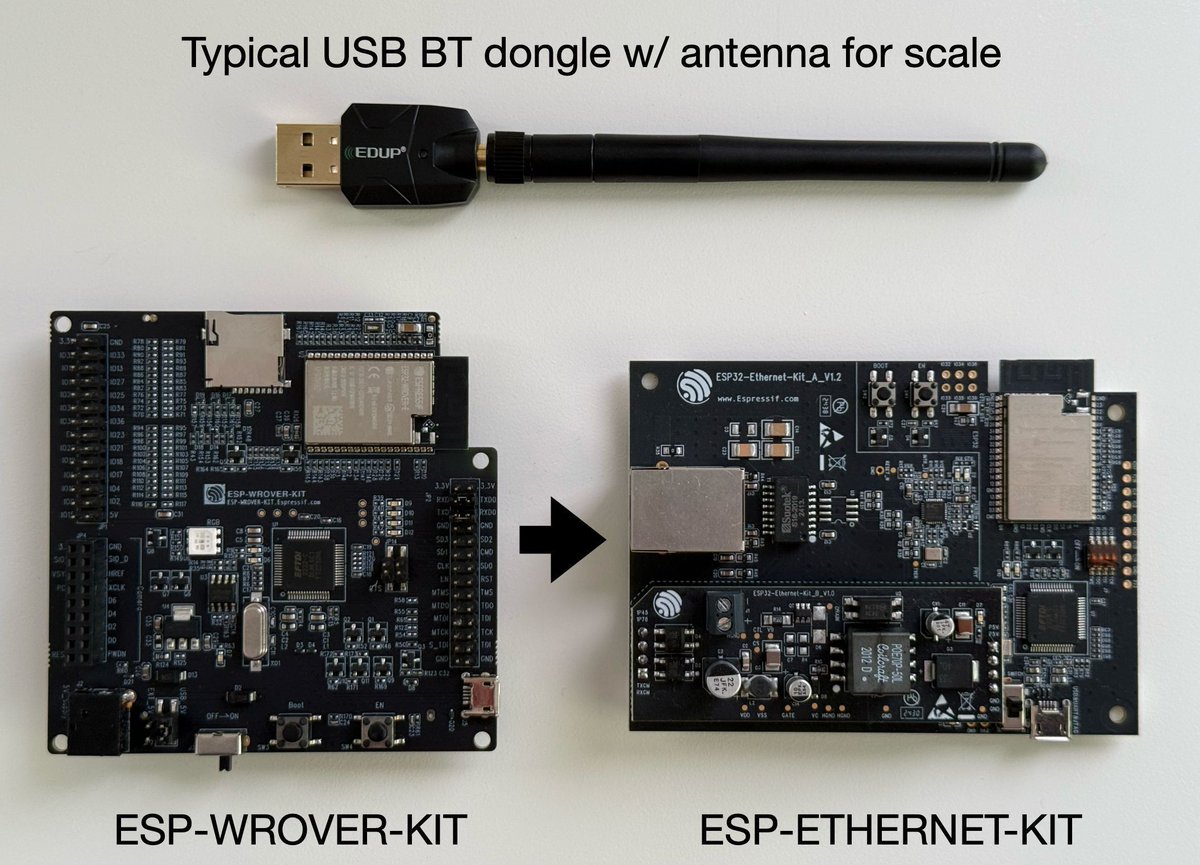
A practical approach to IoT devices vulnerability research Series (2021) by Ruben Santamarta (IOActive Labs) Part 1: labs.ioactive.com/2021/02/a-prac… Part 2: labs.ioactive.com/2021/02/a-prac… Part 3: labs.ioactive.com/2021/02/a-prac… #iot









“Reverse engineering Realtek RTL8761B* Bluetooth chips, to make better Bluetooth security tools & classes” (slide deck by Xeno Kovah) darkmentor.com/publication/20… #infosec