Infoneeds
@infoneeds1
ID: 1278726700667305984
02-07-2020 16:26:29
1,1K Tweet
44 Followers
287 Following



🚨 ALL FREE CERTIFICATION RESOURCES 🚨 No paywalls. No BS. Just value. 📘 AWS 👉 drive.google.com/drive/mobile/f… 🔐 CISSP 👉 drive.google.com/drive/mobile/f… 🛡️ CISA 👉 drive.google.com/drive/mobile/f… 📊 CISM 👉 drive.google.com/drive/mobile/f… ⚠️ CRISC 👉 drive.google.com/drive/mobile/f… 🌐 CCDA 👉







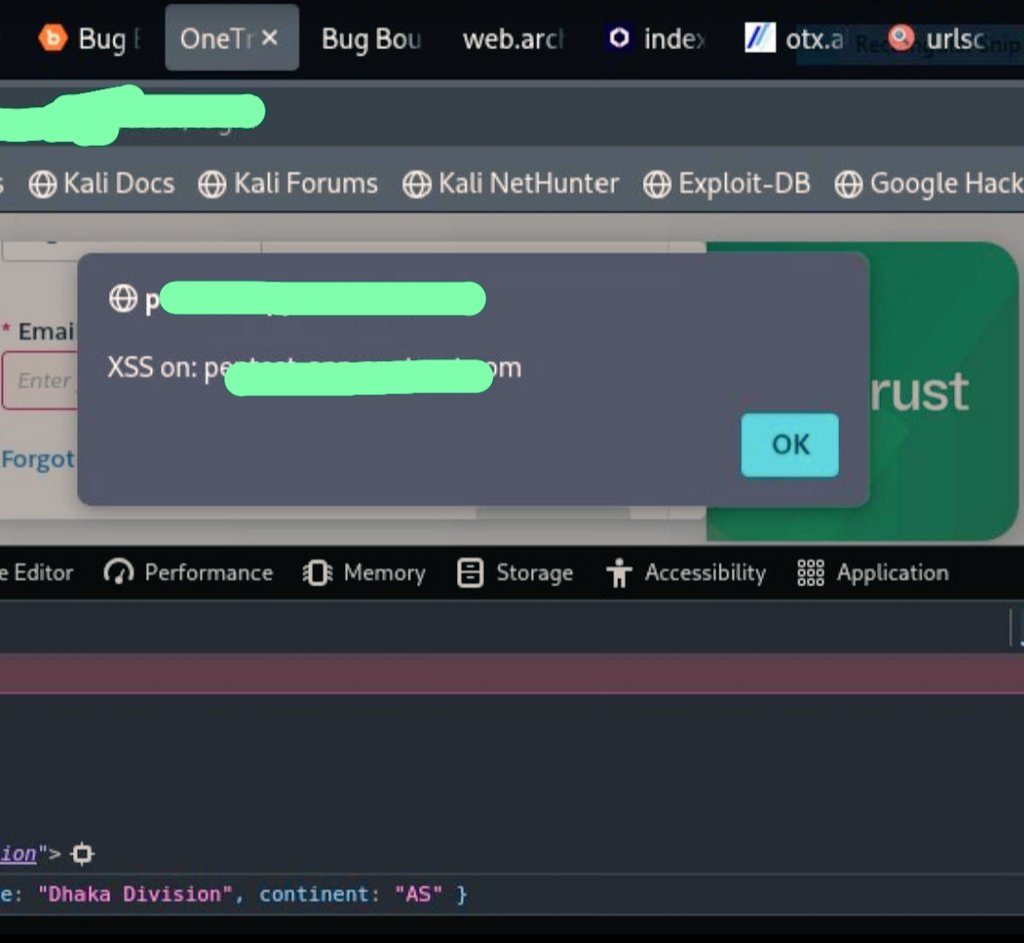
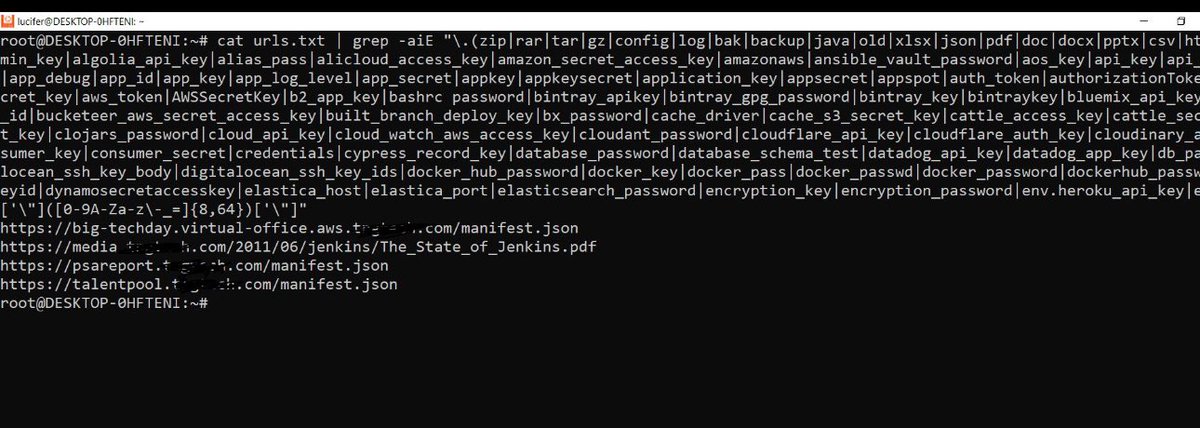
1 rat ... 1 lifetime ... 1 opportunity ;-) - Security testing repo: github.com/The-XSS-Rat/Se… - Subscraper repo: github.com/The-XSS-Rat/su… - Hackxpert-brute repo: github.com/The-XSS-Rat/ha… - RatDo Repo: github.com/The-XSS-Rat/Ra… - RatPetShop repo: github.com/The-XSS-Rat/Ra… - Medium: