DataFuel
@datafuel0
ID: 1627602636932358145
20-02-2023 09:35:11
374 Tweet
9 Followers
25 Following








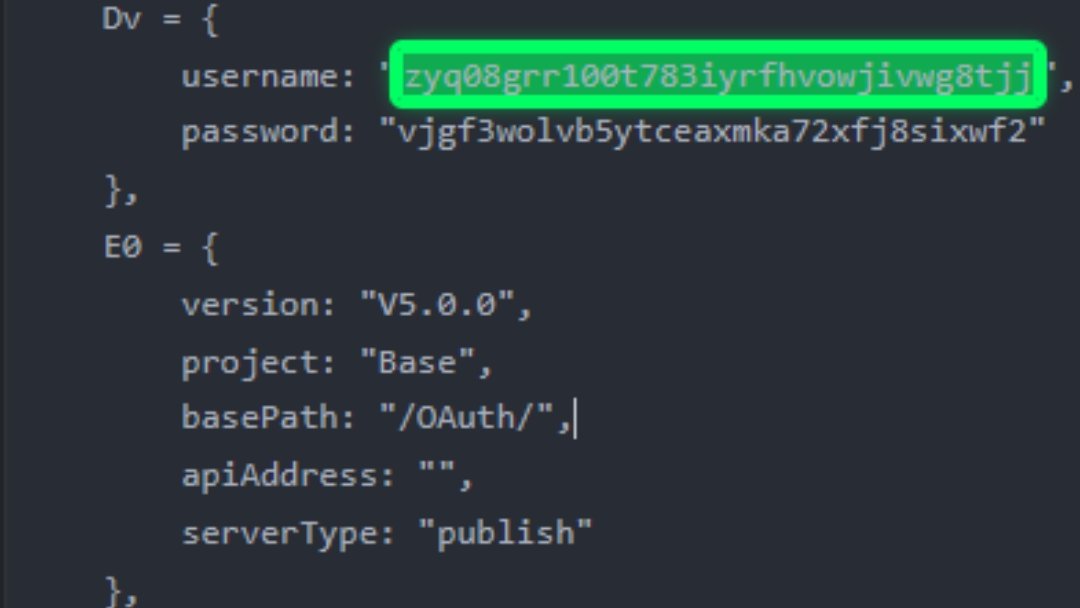
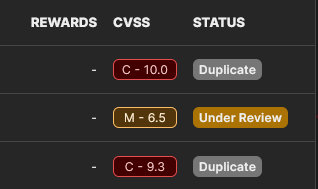
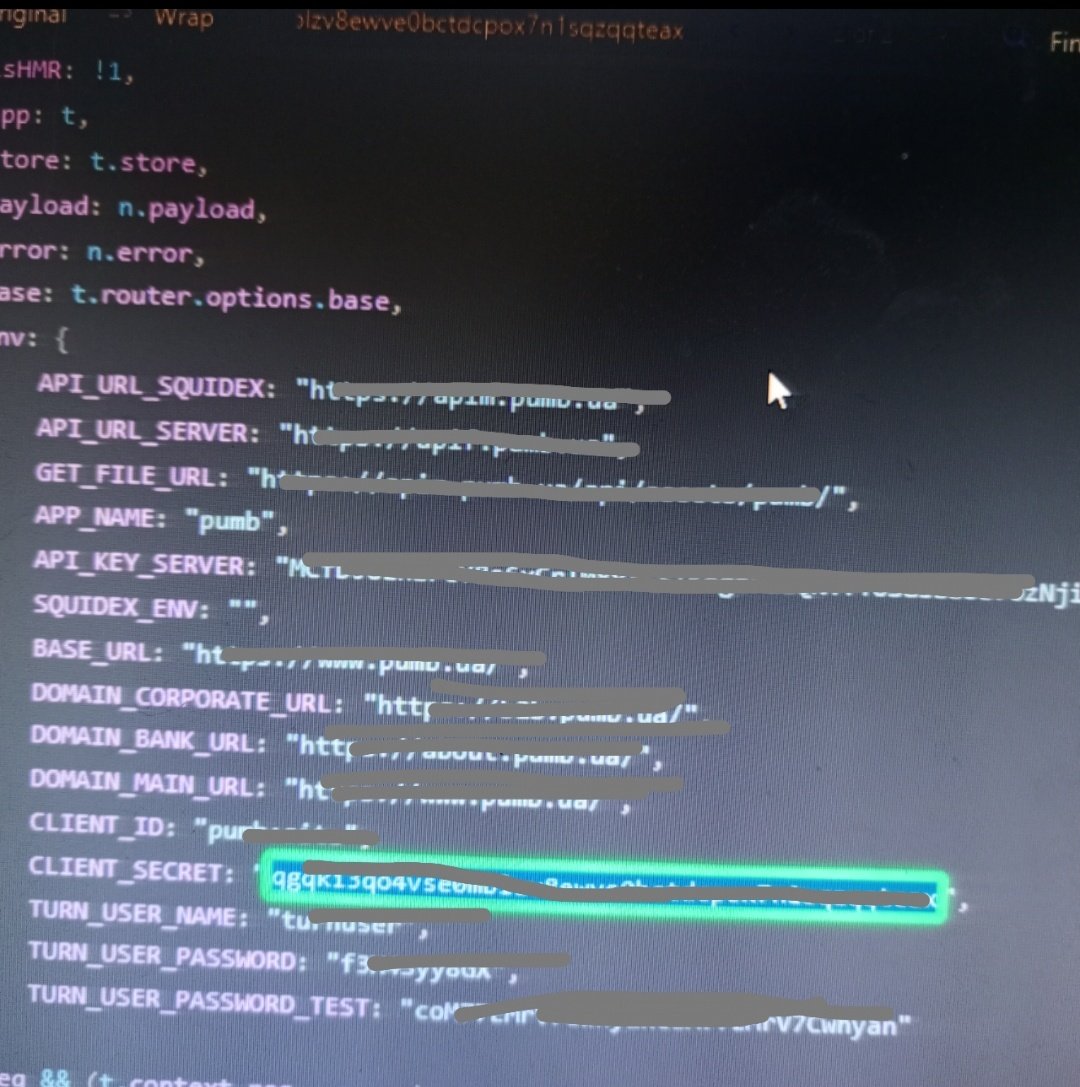
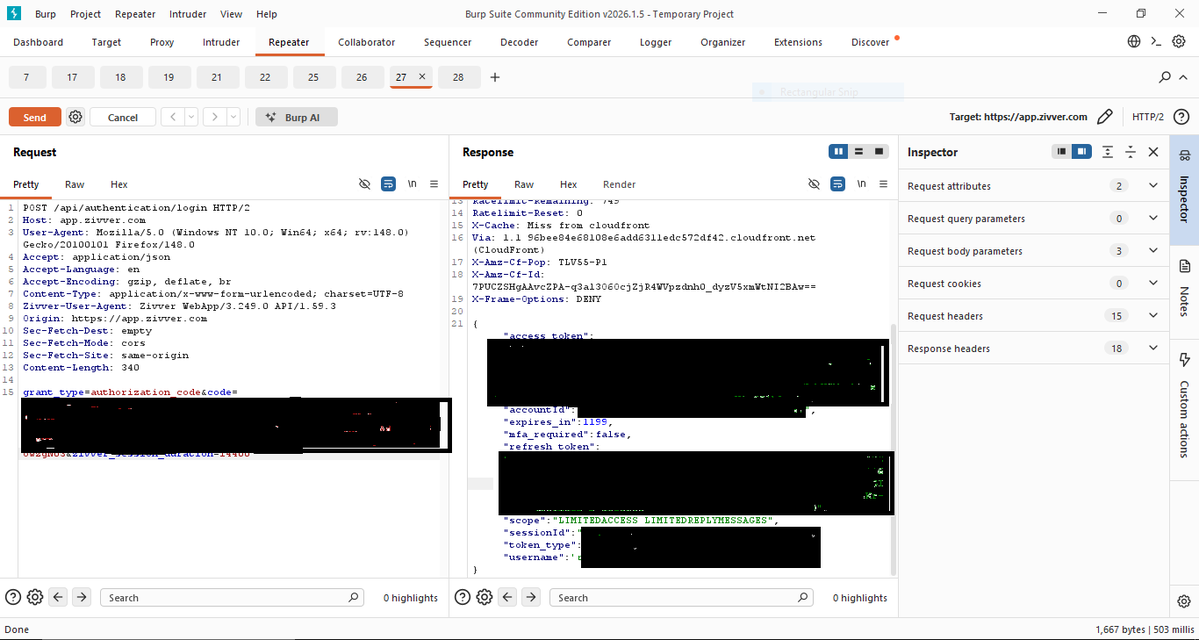
I’m not an expert, my te.. community asked how I choose HackerOne programs. I use Claude Sonnet + simple PowerShell checks before hunting. I made a prompt to help pick better targets on any bug bounty platform. Prompt link from my calude storage: erdserqzroebtfztwmgh.supabase.co/storage/v1/obj…