ii4gsp
@ii4gsp
Security Researcher
ID: 1671802547823312899
http://ii4gsp.github.io 22-06-2023 08:49:37
56 Tweet
99 Followers
182 Following

PageJack: A Powerful Exploit Technique With Page-Level UAF blackhat.com/us-24/briefing… Slides: i.blackhat.com/BH-US-24/Prese… Repository: github.com/Lotuhu/Page-UAF WP: arxiv.org/abs/2401.17618 Zhiyun Qian, Jiayi Hu, Jinmeng Zhou, Qi Tang & Wenbo Shen Zhiyun Qian

EC #37 is out and it's stacked 🗞️ hypr (find me on bluesky) pops the same bug 4 different ways A Linux LPE from ii4gsp Pwn2Own Automative exploits from Sector 7 Chrome and Windows ITW bugs ft S K, j j, 1377 High-yield Nukes, DARKNAVY + Jobs and more 👇 blog.exploits.club/exploits-club-…





Slides and recording from my "SLUB Internals for Exploit Developers" talk at LSS (@[email protected]) yesterday 🥳 Slides: docs.google.com/presentation/d… Slides PDF: static.sched.com/hosted_files/l… Recording: youtu.be/WWQh4yAoXME?t=…






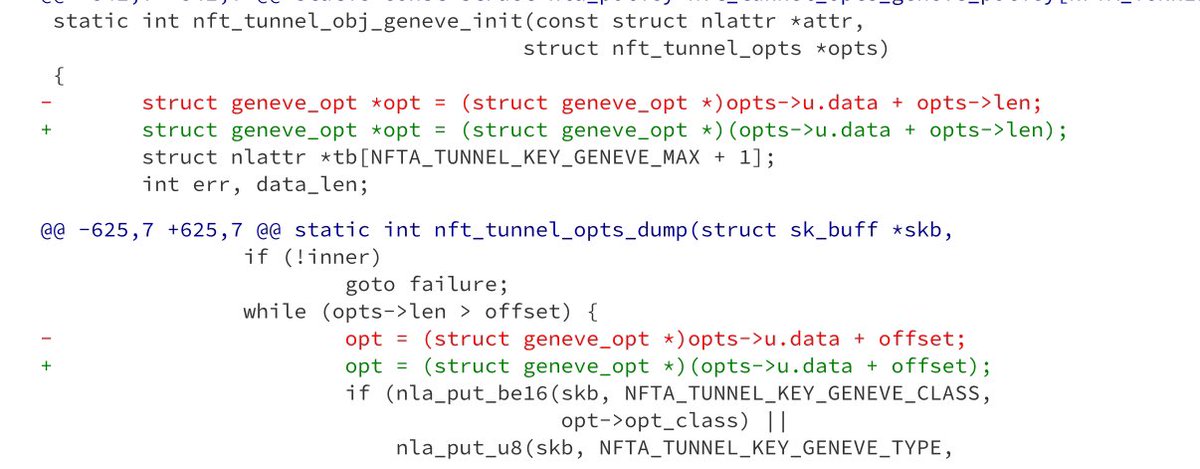
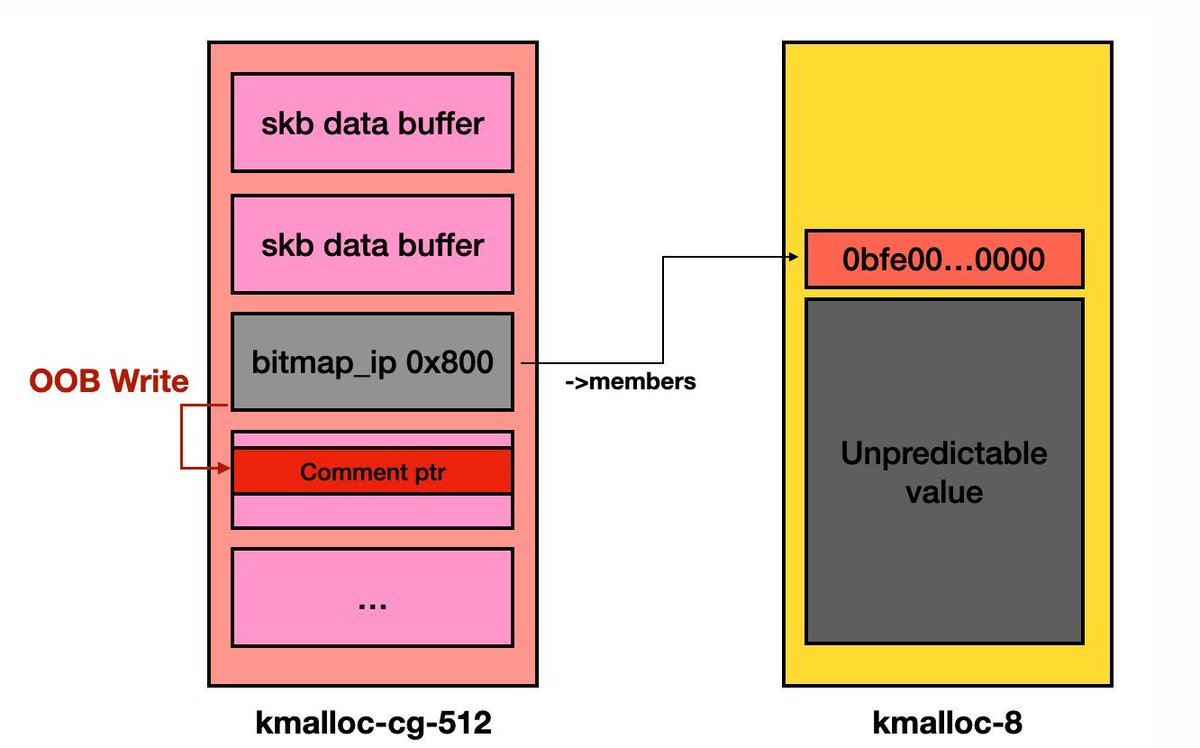
I tried my hand at exploiting an nday on the Google Container Optimized OS instance in kCTF but sadly was very late to the party. Here is my exploit write-up for it. I learned a lot during the process, let me know what you think. I'll post TL;DR in thread h0mbre.github.io/Patch_Gapping_…