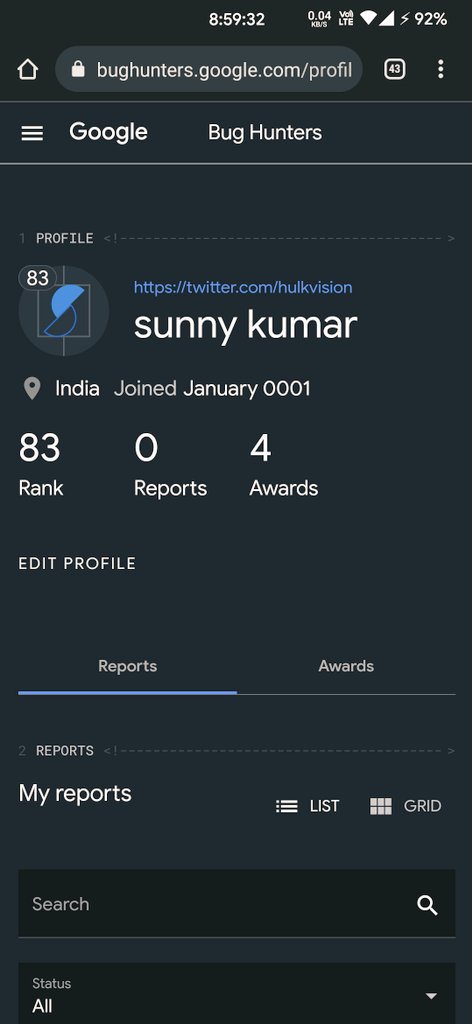
sunny
@hulkvision
Learning android hacking | bug hunter |
ID: 844198878568243200
https://hulkvision.github.io 21-03-2017 14:47:51
68 Tweet
880 Followers
291 Following









#0day #research #bugbounty #informationsecurity blog.malicious.group/from-akamai-to… How I *AM* able to abuse Akamai to abuse F5, to abuse all of their customers. This is a bug chain that doesn't require a bug on the target domain to exploit them. But what do I know, I am a freelance nobody.


Started my smart contract auditing journey after completing the Cyfrin Updraft 🟩 course with AI ARENA | ʌı Code4rena contest. Reported 3 high severity bugs, waiting for the contest results to see how i performed.