Jinay Patel
@0_0eth0
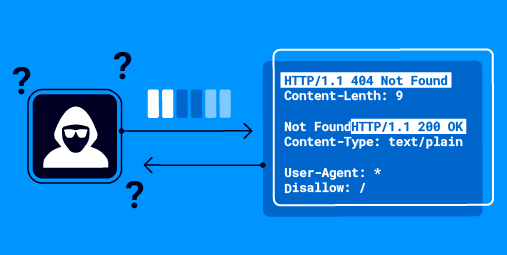
Looking at the burp history & analyzing | InfoSec | Hacker | An semi-active member at @Hacker0x01 | Securing IoMT Devices | BLR🔁AMD | Views are my own
ID: 334117771
12-07-2011 16:12:48
1,1K Tweet
783 Takipçi
118 Takip Edilen






🚨 Hey Hackers! 🚨 Get ready for HackerOne Hacking Meetup – Bangalore 3rd Edition! 🌟 organized by Akshansh Jaiswal 🎯 Hack live on a private program 🎁 Earn bounties & rewards 🤝 Collaborate, learn, and network with top hackers 🗓️ Event Date: December 7th Don’t miss out –




Attention Kali Linux users! In the coming day(s), apt update is going to fail for pretty much everyone. The reason? We had to roll a new signing key for the Kali repository. You need to download and install the new key manually: offs.ec/4lUEtak



Jenish Sojitra Little late to this, but you can follow these steps: 1. Create Rooted AVD with rootAVD & Magisk v27. Choose SDK API v33. 2. Add magisk modules: MagiskFrida, Always Trust User Certificates 3. Use the following script with Frida: github.com/hackcatml/frid… This worked for me.




New reconftw small release with a bunch of QoL improvements, small fixes and ip.thc.org by The Hacker's Choice (@[email protected]) added as a source for passive subs and RevDNS entries. ENJOY! github.com/six2dez/reconf…