NEURON TEAM
@hillstone_lab
Hillstone Security Technology Research Institute. 情報セキュリティ技術研究所
ID: 1401080962209828864
http://www.hillstonenet.com 05-06-2021 07:38:37
22 Tweet
57 Followers
47 Following


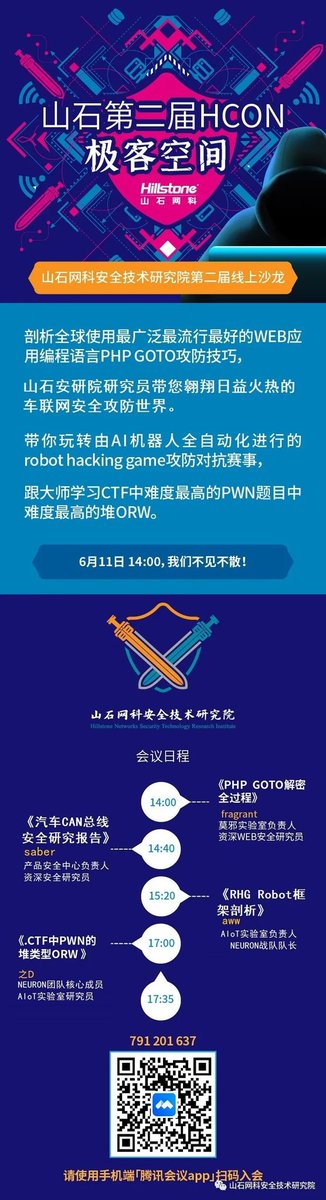
Hillstone Networks' second online HCON Information Security Technology Salon counts down to 3 days Hillstone Networks #security #infosec #cybersecurity