Heretic_Nerd
@heretic_nerd
Security and Programming
ID: 1353925308223692800
26-01-2021 04:40:10
999 Tweet
47 Followers
1,1K Following
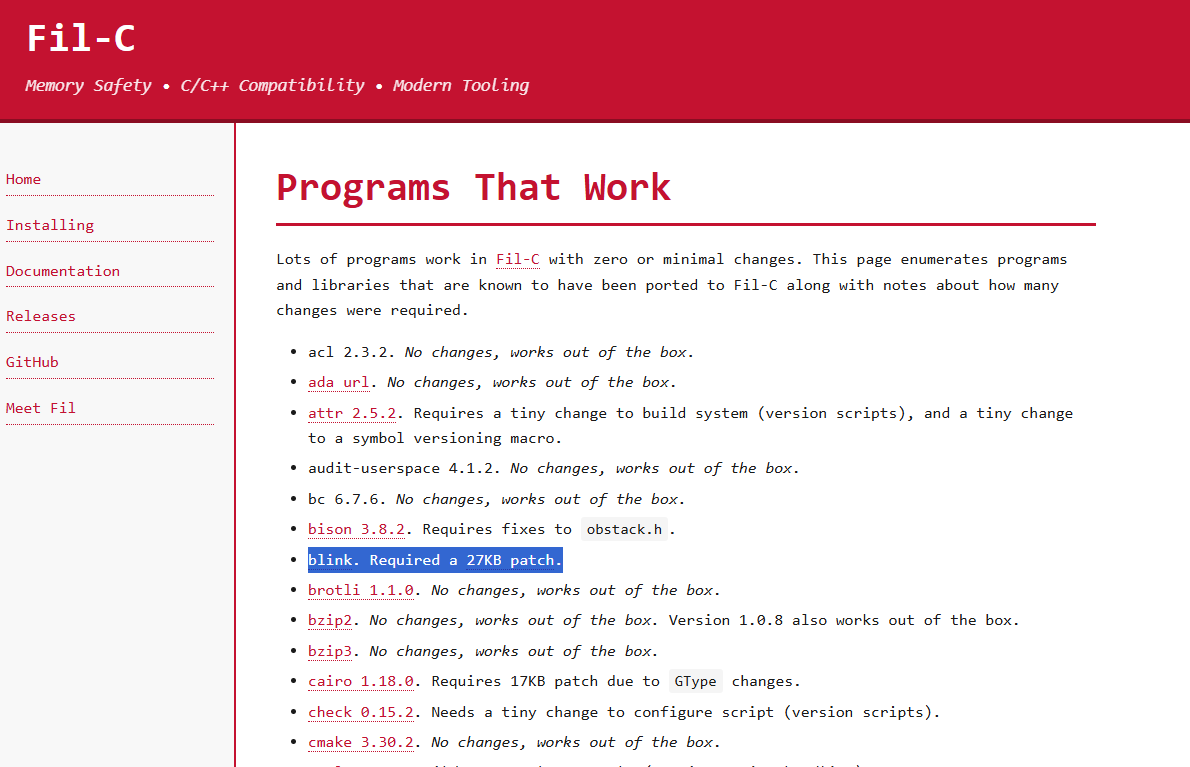
I'm so proud that my project Blink is one of the first to be officially listed as Fil-C compatible. I'm amazed it was even possible. I'm happy with how easy it was. Filip Jerzy Pizło was super helpful too.
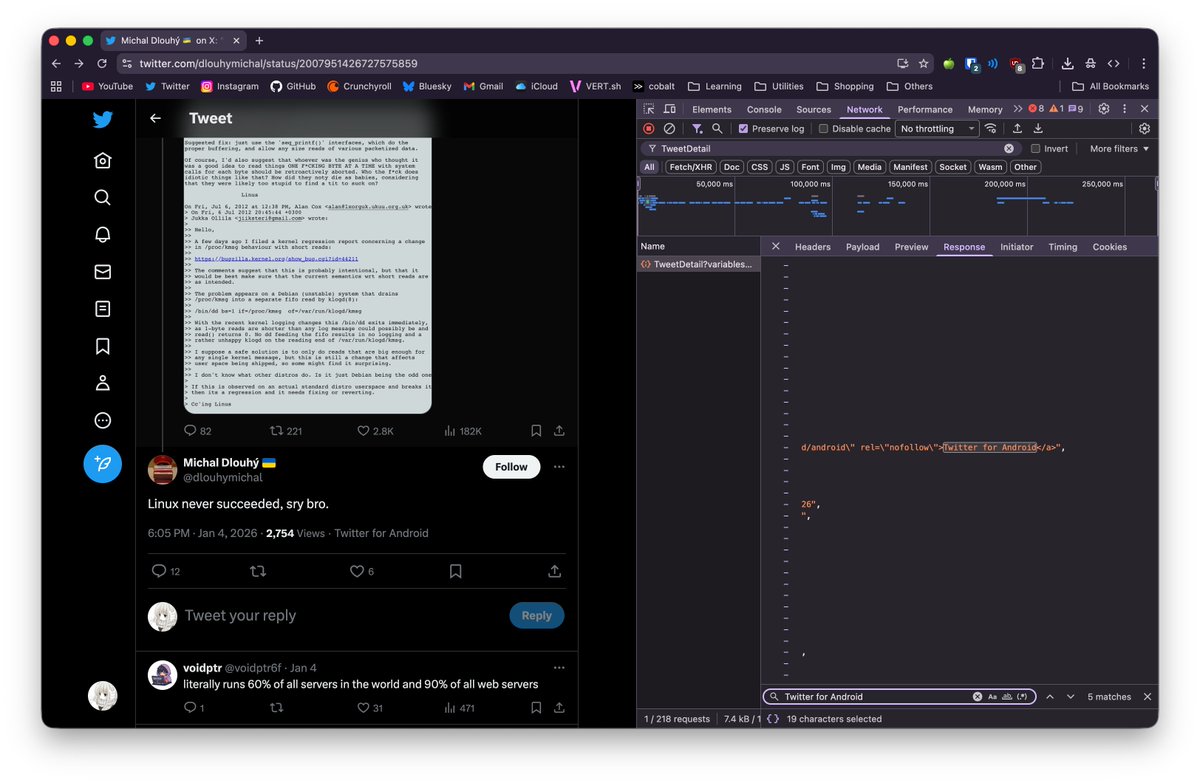
Last month, Zellic researcher Faith 🇧🇩🇦🇺 gave an internal talk on pwning Linux kernel. He teased an exploit he'd be submitting to a 0day challenge. Today, Faith 🇧🇩🇦🇺 and his teammate just won $40,000 for a Linux kernel 0-day! Congratulations Faith!









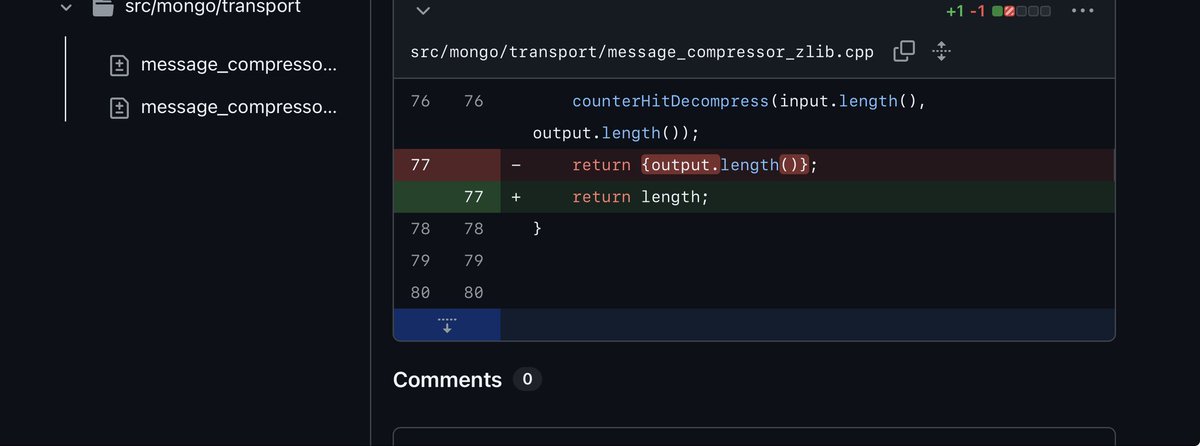
The MongoBleed vuln is such a cool and powerful primitive, it practically allows you to remotely live-view the host memory (limits still apply) and navigate around like a local hexdump! I made a TUI live memory browser based on Joe Desimone's PoC. Credits to him for the original PoC






tl;dr > decide to do winsock malware poc > need to be position indepedent > low as possible to metal > post about it > Dominic Chell 👻 recommends x86matthew research > "nah not related" > mfw i was wrong > get code working > need to remove abstractions > start reversing winsocks > mfw