GRInfosec
@grinfosecurity
🏴 Cymro. Information security practitioner, cyber defence lead. Outdoor enthusiast. Supporter @SecurityBsides.
ID: 2448170923
16-04-2014 22:26:30
208 Tweet
188 Followers
2,2K Following













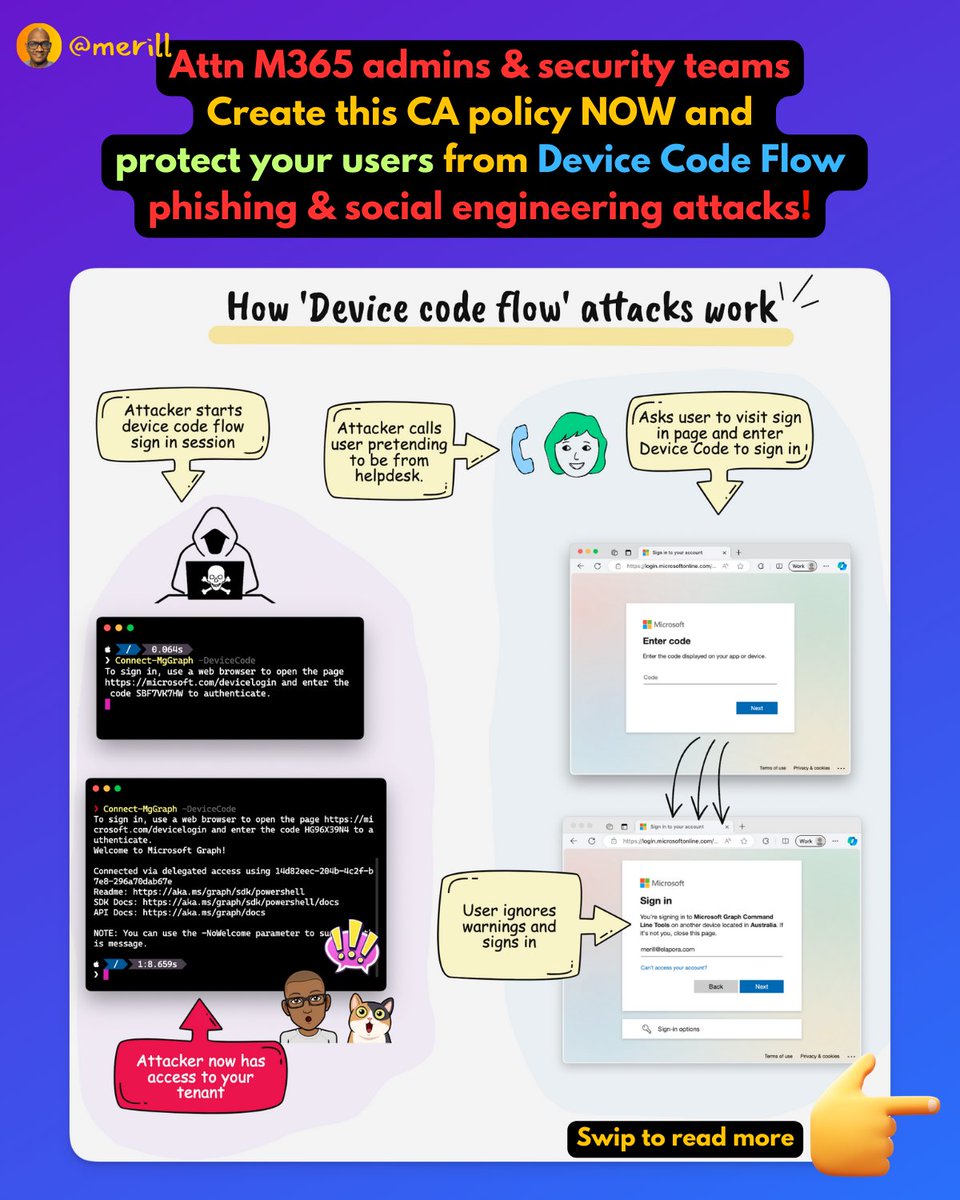
Folks, I'm super excited to announce a three part webinar series from Microsoft that involves some of your favorite folks from the Entra community. Nathan McNulty and Ru Campbell will be joining me and others from Microsoft to talk about implementing Zero Trust for identity and