
B3rt0
@rpsanch
#Cyber hunter with my navigation on and trying to find my next thrill (views expressed are my own) #threatintel #OSINT #malware #infosec #phishing
ID: 3448979902
26-08-2015 17:01:24
3,3K Tweet
914 Followers
1,1K Following

Appears to be #agenttesla distribution through mal_docx and template injection and EQNED.exe vul #CVE-2017-11882. Same smtp exfil domain found by enjoying being dumb PI992020.docx 2522dfe82c933dc4b88ec021a4dad080 us2.smtp.mailhostbox[.]com JAMESWT_MHT Joakim Kennedy
![Gage (@circuitous__) on Twitter photo Appears to be #agenttesla distribution through mal_docx and template injection and EQNED.exe vul #CVE-2017-11882. Same smtp exfil domain found by <a href="/_Bear_Crawl_/">enjoying being dumb</a>
PI992020.docx
2522dfe82c933dc4b88ec021a4dad080
us2.smtp.mailhostbox[.]com
<a href="/JAMESWT_MHT/">JAMESWT_MHT</a> <a href="/joakimkennedy/">Joakim Kennedy</a> Appears to be #agenttesla distribution through mal_docx and template injection and EQNED.exe vul #CVE-2017-11882. Same smtp exfil domain found by <a href="/_Bear_Crawl_/">enjoying being dumb</a>
PI992020.docx
2522dfe82c933dc4b88ec021a4dad080
us2.smtp.mailhostbox[.]com
<a href="/JAMESWT_MHT/">JAMESWT_MHT</a> <a href="/joakimkennedy/">Joakim Kennedy</a>](https://pbs.twimg.com/media/EhfbaIXXYAAQuSH.png)

Possible new #mustangpanda or #reddelta #APT activity. Possibly related to the campaign against Vatican Hash : cc233b9f02903b91d57ff3b6625c6719 Name: Catholic Bishops call for urgent Cameroon peace talks.exe Arkbird Florian Roth ⚡️ RedDrip Team Shadow Chaser Group Gage


C2: http://103.85.24[.]158/hk097.dat Payload : #PlugX James Dodge This Security Security Doggo
![ᴘᴀʀᴛʜɪ (@cyber__sloth) on Twitter photo C2: http://103.85.24[.]158/hk097.dat
Payload : #PlugX
<a href="/James_inthe_box/">James</a> <a href="/shotgunner101/">Dodge This Security</a> <a href="/securitydoggo/">Security Doggo</a> C2: http://103.85.24[.]158/hk097.dat
Payload : #PlugX
<a href="/James_inthe_box/">James</a> <a href="/shotgunner101/">Dodge This Security</a> <a href="/securitydoggo/">Security Doggo</a>](https://pbs.twimg.com/media/EhjjnXEX0AEfJmd.jpg)

#REvil/#Sodinokibi moved to #golang for their #ransomware...? 6eb69acd2ac82be838c8b3d8910b0d70 CC: MalwareHunterTeam Michael Gillespie JAMESWT_MHT Vitali Kremez
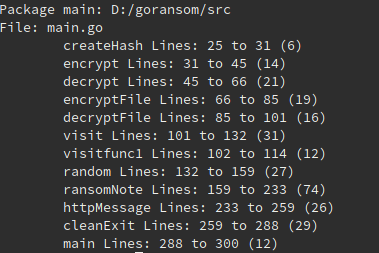



#RobbinHood #golang #ransomware: 3ad2dfa916d473848df470bdd0b18968 VT: 7/72 "pdb": C:/Users/User/go/src/Robbinhood7 CC: Vitali Kremez, Michael Gillespie, MalwareHunterTeam, JAMESWT_MHT




DocuSign-themed #malxls delivering #ursnif / #gozi #malware h113198x9.xlsm bd8e543c53506ca06c085efdb937854a http://premiumstatics[.]co/con3cti0n.dll con3cti0n.dll c8392d93a1f064a53abb61887cad409b JAMESWT_MHT #ThreatIntel #ThreatHunting
![Gage (@circuitous__) on Twitter photo DocuSign-themed #malxls delivering #ursnif / #gozi #malware
h113198x9.xlsm
bd8e543c53506ca06c085efdb937854a
http://premiumstatics[.]co/con3cti0n.dll
con3cti0n.dll
c8392d93a1f064a53abb61887cad409b
<a href="/JAMESWT_MHT/">JAMESWT_MHT</a>
#ThreatIntel #ThreatHunting DocuSign-themed #malxls delivering #ursnif / #gozi #malware
h113198x9.xlsm
bd8e543c53506ca06c085efdb937854a
http://premiumstatics[.]co/con3cti0n.dll
con3cti0n.dll
c8392d93a1f064a53abb61887cad409b
<a href="/JAMESWT_MHT/">JAMESWT_MHT</a>
#ThreatIntel #ThreatHunting](https://pbs.twimg.com/media/EoFieLmXcAgoN1b.jpg)



#APT #sidewinder gearing up for their campaign with newly registered domains. gov-pbs[.]net gov-nadra[.]net gov-af[.]net gov-crt[.]net gov-pmo[.]net. Registered on Late December. Shadow Chaser Group Arkbird @Rmy James markus neis
![ᴘᴀʀᴛʜɪ (@cyber__sloth) on Twitter photo #APT #sidewinder gearing up for their campaign with newly registered domains.
gov-pbs[.]net
gov-nadra[.]net
gov-af[.]net
gov-crt[.]net
gov-pmo[.]net. Registered on Late December. <a href="/ShadowChasing1/">Shadow Chaser Group</a> <a href="/Arkbird_SOLG/">Arkbird</a> <a href="/Rmy_Reserve/">@Rmy</a> <a href="/James_inthe_box/">James</a> <a href="/markus_neis/">markus neis</a> #APT #sidewinder gearing up for their campaign with newly registered domains.
gov-pbs[.]net
gov-nadra[.]net
gov-af[.]net
gov-crt[.]net
gov-pmo[.]net. Registered on Late December. <a href="/ShadowChasing1/">Shadow Chaser Group</a> <a href="/Arkbird_SOLG/">Arkbird</a> <a href="/Rmy_Reserve/">@Rmy</a> <a href="/James_inthe_box/">James</a> <a href="/markus_neis/">markus neis</a>](https://pbs.twimg.com/media/Eq5PWWwXAAM3Qzn.jpg)


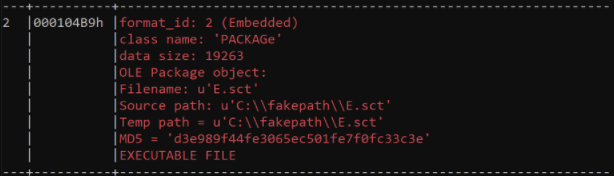
Possible #Bahamut #APT campaign IOCs. docx dropping rtf containing sct file that modifies tmp file to drop VB exe. one domain reported on previously by BlackBerry thanks to Yury Polozov @t0001100000 d2hvYW1p pastebin.com/9U57CHZn ᴘᴀʀᴛʜɪ Arkbird ςεяβεяμs - мαℓωαяε яεsεαяςнεя

#PrimitiveBear #Gamaredon group campaign IOCs. Timely mal docx files with template injection TTPs Thanks to Yury Polozov and @t0001100000 IOCs - pastebin.com/JmksCTch Arkbird Mikhail Kasimov /Pistus.exe Jazi Shadow Chaser Group JAMESWT_MHT ςεяβεяμs - мαℓωαяε яεsεαяςнεя Joakim Kennedy
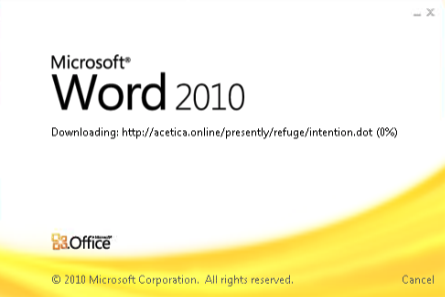

Looks like #PrimitiveBear #Gamaredon using remote template injection протокол макарони.docx 0db02addc704c71e0260a1132697208c http://83.166.246[.]59/SGZ2/sought.dot 83.166.246.59 ᴘᴀʀᴛʜɪ ςεяβεяμs - мαℓωαяε яεsεαяςнεя Jazi JAMESWT_MHT
![Gage (@circuitous__) on Twitter photo Looks like #PrimitiveBear #Gamaredon using remote template injection
протокол макарони.docx
0db02addc704c71e0260a1132697208c
http://83.166.246[.]59/SGZ2/sought.dot
83.166.246.59
<a href="/cyber__sloth/">ᴘᴀʀᴛʜɪ</a> <a href="/c3rb3ru5d3d53c/">ςεяβεяμs - мαℓωαяε яεsεαяςнεя</a> <a href="/h2jazi/">Jazi</a> <a href="/JAMESWT_MHT/">JAMESWT_MHT</a> Looks like #PrimitiveBear #Gamaredon using remote template injection
протокол макарони.docx
0db02addc704c71e0260a1132697208c
http://83.166.246[.]59/SGZ2/sought.dot
83.166.246.59
<a href="/cyber__sloth/">ᴘᴀʀᴛʜɪ</a> <a href="/c3rb3ru5d3d53c/">ςεяβεяμs - мαℓωαяε яεsεαяςнεя</a> <a href="/h2jazi/">Jazi</a> <a href="/JAMESWT_MHT/">JAMESWT_MHT</a>](https://pbs.twimg.com/media/E2fmsmcXMAMhga8.png)

Spotlight on Joakim Kennedy and his talk: The Dark Side of Go: A 2020 Go Malware Round-Up youtu.be/rcsWz-gT0sI #gopherconEU #golang
![Gage (@circuitous__) on Twitter photo Appears to be #AgentTesla delivered via #maldoc exploiting #CVE-2017-11882. #opendir: savemodificationgloballyfromthepinaltypo[.]duckdns[.]org
NEW ORDER NO. SVLG075904.docx
551077ebeb5bc105ffd4b433ed89358a
rb[.]gy
vbc.exe-3a38731d63fc1d7397ea3b7c4bc2c73d
<a href="/joakimkennedy/">Joakim Kennedy</a> <a href="/rpsanch/">B3rt0</a> Appears to be #AgentTesla delivered via #maldoc exploiting #CVE-2017-11882. #opendir: savemodificationgloballyfromthepinaltypo[.]duckdns[.]org
NEW ORDER NO. SVLG075904.docx
551077ebeb5bc105ffd4b433ed89358a
rb[.]gy
vbc.exe-3a38731d63fc1d7397ea3b7c4bc2c73d
<a href="/joakimkennedy/">Joakim Kennedy</a> <a href="/rpsanch/">B3rt0</a>](https://pbs.twimg.com/media/EjlBDyOWkAIBHS8.png)
![Gage (@circuitous__) on Twitter photo #malXLSX exploiting #CVE-2017-11882 to drop what appears to be #agenttesla
MRKRFQPD-1682020.xlsx
cb57e8bab6e835b5c8a41db0429fb9d4
pars-science[.]ir
INTERIORRAWFILE.exe
3fb45dffb8a667262be92cee09cf5311
#malware #ThreatIntel #ThreatHunting #malXLSX exploiting #CVE-2017-11882 to drop what appears to be #agenttesla
MRKRFQPD-1682020.xlsx
cb57e8bab6e835b5c8a41db0429fb9d4
pars-science[.]ir
INTERIORRAWFILE.exe
3fb45dffb8a667262be92cee09cf5311
#malware #ThreatIntel #ThreatHunting](https://pbs.twimg.com/media/EnhLsD5WMAIGfM_.png)
![Gage (@circuitous__) on Twitter photo #formbook #malware distributed via #maldoc that exploits #CVE-2017-11882.
INV#2020-000185.docx
6e16c996ef12946d1453ed39b1d71e17
www.reem[.]pro
www.digitalcashteam[.]com
http://103.207.38.170/document.doc
coo.exe
161034a13945eac6eccc0cf5b4f2effc #formbook #malware distributed via #maldoc that exploits #CVE-2017-11882.
INV#2020-000185.docx
6e16c996ef12946d1453ed39b1d71e17
www.reem[.]pro
www.digitalcashteam[.]com
http://103.207.38.170/document.doc
coo.exe
161034a13945eac6eccc0cf5b4f2effc](https://pbs.twimg.com/media/EnmNueDWEAAyXpN.png)