Arkbird
@Arkbird_SOLG
Malware slayer
Member of @CuratedIntel
ID:1089248858058772480
26-01-2019 19:48:59
6,6K Tweets
13,6K Followers
64 Following


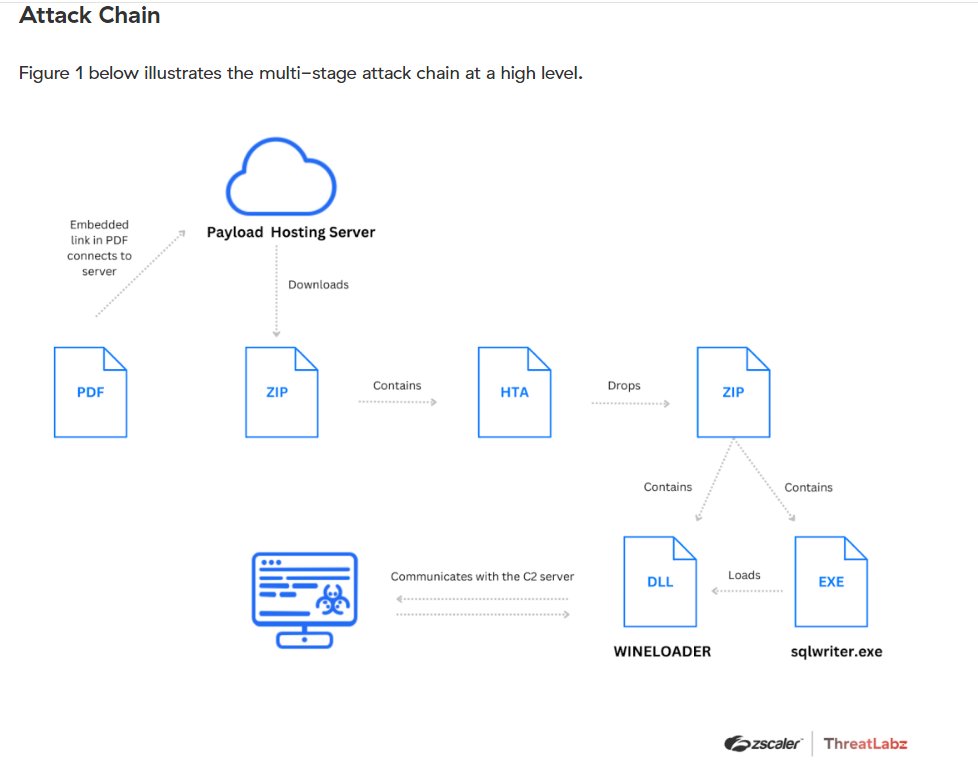
From late 2023 to early 2024, #SharpPanda has continued to target government entities in the Southeast Asia. Group-IB researchers have spotted several initial infection vectors (documents/executables) similar to previous Sharp Panda operations. These malicious files deliver the




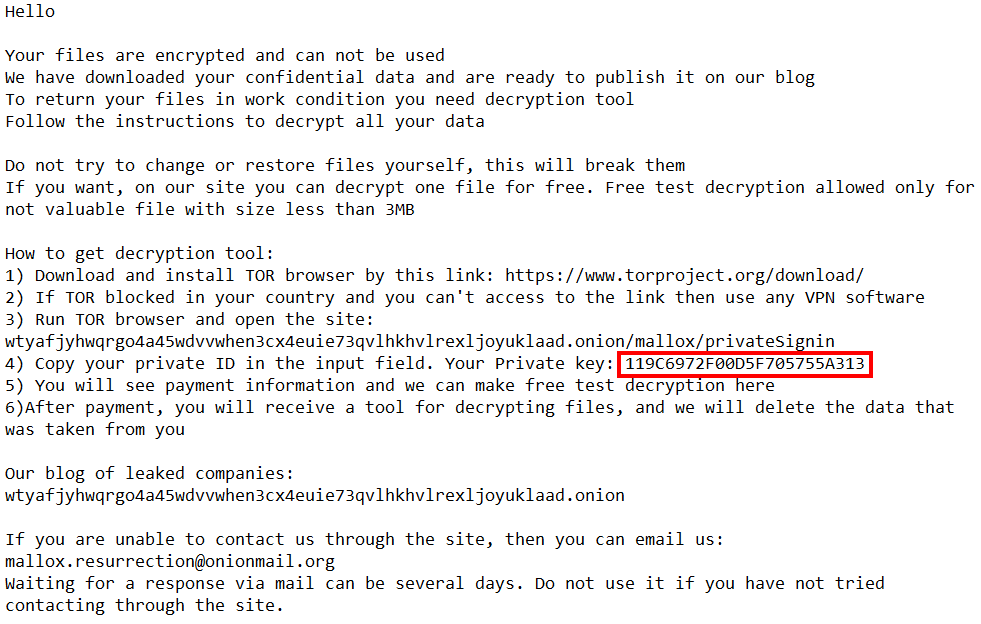
Le très évasif groupe #3am vient de revendiquer une #cyberattaque contre La Compagnie de Phalsbourg en 🇫🇷
Interrogée, la victime ne réfute pas la survenue de l'incident et indique ne pas souhaiter faire de commentaire. #ransomware


While Microsoft's User Account Control is not defined as a security boundary, bypassing UAC is still something attackers frequently do. Check out this blog post from Matt Nelson detailing one method for bypassing UAC using App Paths. ghst.ly/43U8XQY

Malicious activity tracked under the campaign #OperationMidnightEclipse is targeting CVE-2024-3400, which exploits a vulnerability in certain versions of PAN-OS software. This threat brief covers mitigations and product protections: bit.ly/3vPUngM


Our team at Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this Palo Alto Networks advisory security.paloaltonetworks.com/CVE-2024-3400




Wrote an Program(POC) for Early Bird APC and
APC Queue Code.
Link: github.com/Whitecat18/Rus…
github.com/Whitecat18/Rus…
#maldev #offensiverust #redteaming #pentesting #CyberSecurity #rust