
Etienne Cote
@ecote7
Father, Cybersecurity Consultant, OSCP, Security enthusiast and one CVE :)
ID: 2512485164
21-05-2014 12:38:52
2,2K Tweet
89 Followers
619 Following

In our latest blogpost, Quentin Roland presents an often overlooked AD attack surface related to OUs ACLs,with the release of a dedicated exploitation tool, OUned.py (github.com/synacktiv/OUned). synacktiv.com/publications/o…


Something that was extremely helpful for me yesterday is this PR by to properly handle cross-realm tickets requests. Having got a [email protected] that is a member of ForeignSecurityPrincipals container in B.LOC, I could successfully request her ST and pwn B 🥰 github.com/fortra/impacke…


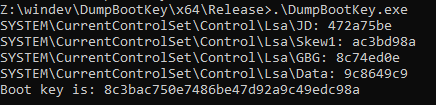
Decorrelate attack tool behaviour to avoid EDR interference. In this post, Aurélien Chalot writes about how remote LSA secrets dumping works and retrieves a Windows computer's BOOTKEY using less common methods. sensepost.com/blog/2024/dump…












![Jean-Michel Besnard (@jmbesnard_maz) on Twitter photo Want to check for #ESC15 ? Use the following cypher with #BloodHound
MATCH p=(:Base)-[:MemberOf*0..]->()-[:Enroll|AllExtendedRights]->(ct:CertTemplate)-[:PublishedTo]->(:EnterpriseCA)-[:TrustedForNTAuth]->(:NTAuthStore)-[:NTAuthStoreFor]->(:Domain) WHERE Want to check for #ESC15 ? Use the following cypher with #BloodHound
MATCH p=(:Base)-[:MemberOf*0..]->()-[:Enroll|AllExtendedRights]->(ct:CertTemplate)-[:PublishedTo]->(:EnterpriseCA)-[:TrustedForNTAuth]->(:NTAuthStore)-[:NTAuthStoreFor]->(:Domain) WHERE](https://pbs.twimg.com/media/GZdrQxUWwAApO_f.png)