Dominik Phillips
@dphillips__
ID: 1101482508175200258
01-03-2019 14:01:09
584 Tweet
101 Followers
231 Following













You should checkout the Mimikatz Missing Manual that Darkoperator | 🇺🇦 has made. So much awesome documentation in there. github.com/darkoperator/m…



AV/EDR Lab Environment Setup A curated list of various resources helpful in building own malware-centric research lab. A post by Udayveer Singh (Udayveer Singh) Source: an0nud4y.notion.site/AV-EDR-Lab-Env… #redteam #blueteam #maldev #malwaredevelopment



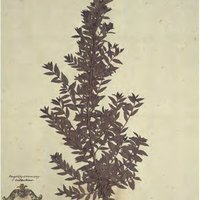
![Byte Atlas (@byteatlas) on Twitter photo [blog post] MalpediaFLOSSed
danielplohmann.github.io/blog/2024/03/0… [blog post] MalpediaFLOSSed
danielplohmann.github.io/blog/2024/03/0…](https://pbs.twimg.com/media/GII-0PyWsAA9kd7.jpg)