deathflash ⚡️
@deathflash1411
Building boxes, hunting bugs & earning bounties
Pentester @cobalt_io | Maintainer @ExploitDB | Meetup Host @hackthebox_eu
Ex: @offsectraining & @ThinkstCanary
ID: 1128191203034353664
https://deathflash.xyz 14-05-2019 06:51:58
97 Tweet
373 Followers
155 Following




I'm excited to be selected as a Subject Matter Expert by Hack The Box, sharing insights to help over 2 million professionals learn and grow. Thank you, HTB, for this incredible opportunity! #Cybersecurity #HackTheBox

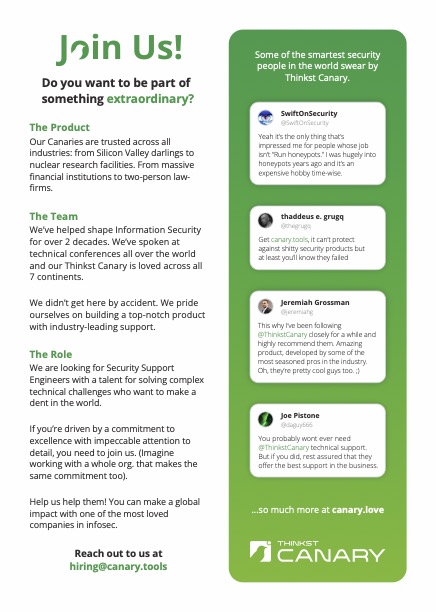
We slipped one of these in the bags at BSides Joburg this weekend because we are looking for amazing support engineers (to join our amazing support engineers). "If you’re driven by a commitment to excellence with impeccable attention to detail, you need to join us" Join us!





D'oh, so you leaked your AWS credentials 🤦♂️ Does it matter 𝐰𝐡𝐞𝐫𝐞? It turns out there's a HUGE difference in how fast attackers will find them. Idan Ben Ari deployed canary tokens (fake AWS credentials) using Thinkst Canary to a number of different locations and analyzed: