
Alex
@cryptogramfan
ID: 1133764730072514562
29-05-2019 15:59:10
43 Tweet
303 Followers
547 Following


If you're interested in malware analysis & RE, I highly recommend the #Zero2Hero course by Vitali Kremez and 0verfl0w. Props to SentinelOne for releasing ~7 hrs of content for free. It's community contributions like these that close the gap between defensive & offensive capability




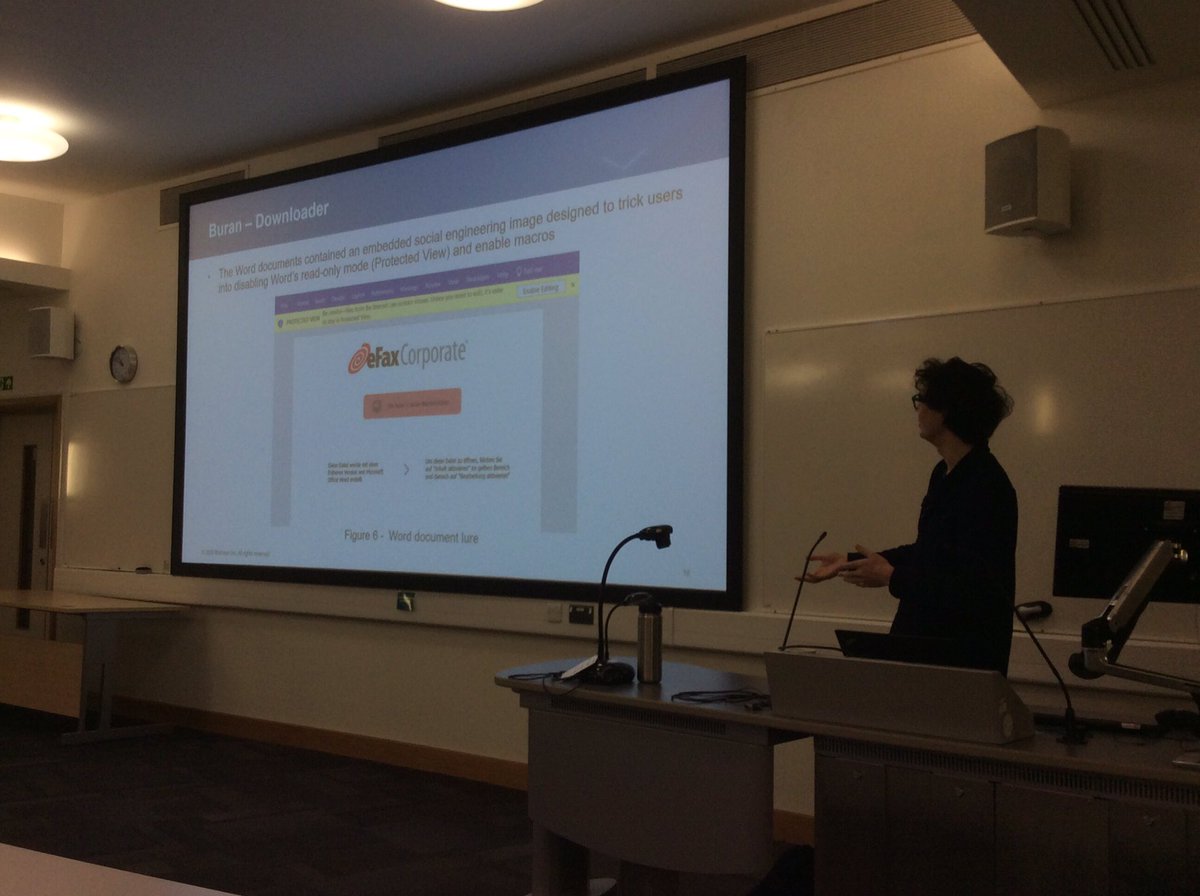
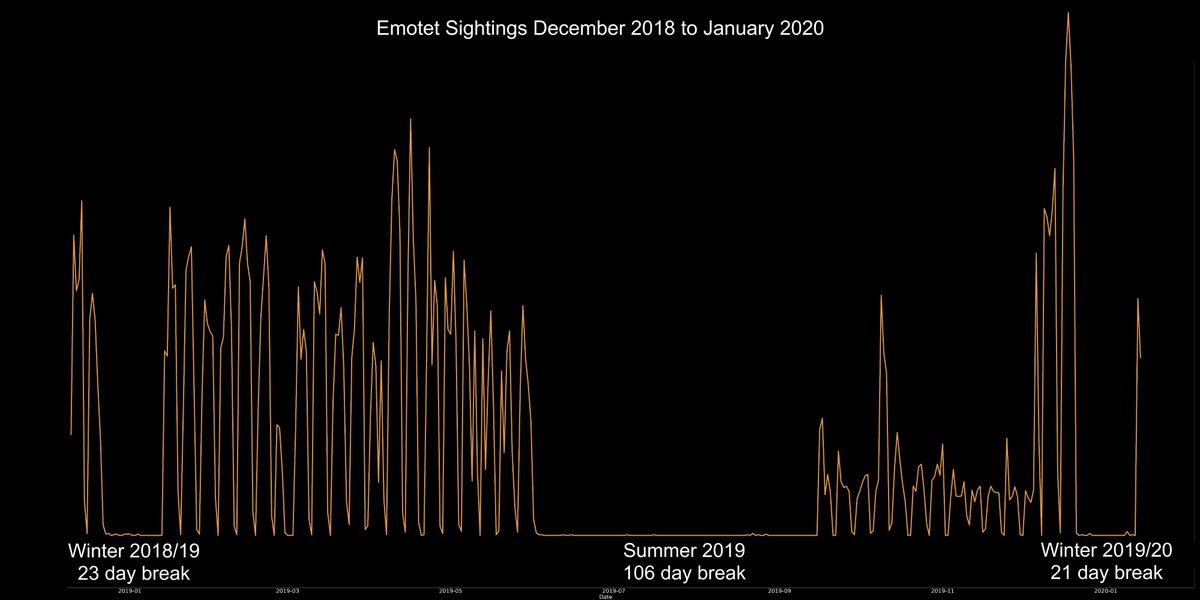
Extremely informative overview of reverse engineering of “Ransomware as a Service” #Buran by Alex Bromium for Joint BCS Cybercrime Forensics OWASP® Foundation OWASP Cambridge UK ARU Cyber Research “Aspects Of Digital Forensics” Workshop ARU ARU Science & Engineering #cambridge on Wednesday 19th Feb








#PurpleFox EK now exploits CVE-2021-26411, demonstrating a short PoC-to-ITW time. On 12 April we isolated a sample from a HP Sure Click Enterprise customer in the Middle East. More details in our write-up by stoerchl on the HP Threat Research blog. threatresearch.ext.hp.com/purple-fox-exp…


We’re super excited to share our research into #opendir malware hunting and announce a new framework at #VBLOCALHOST Virus Bulletin this October! Hope to see many of you there.


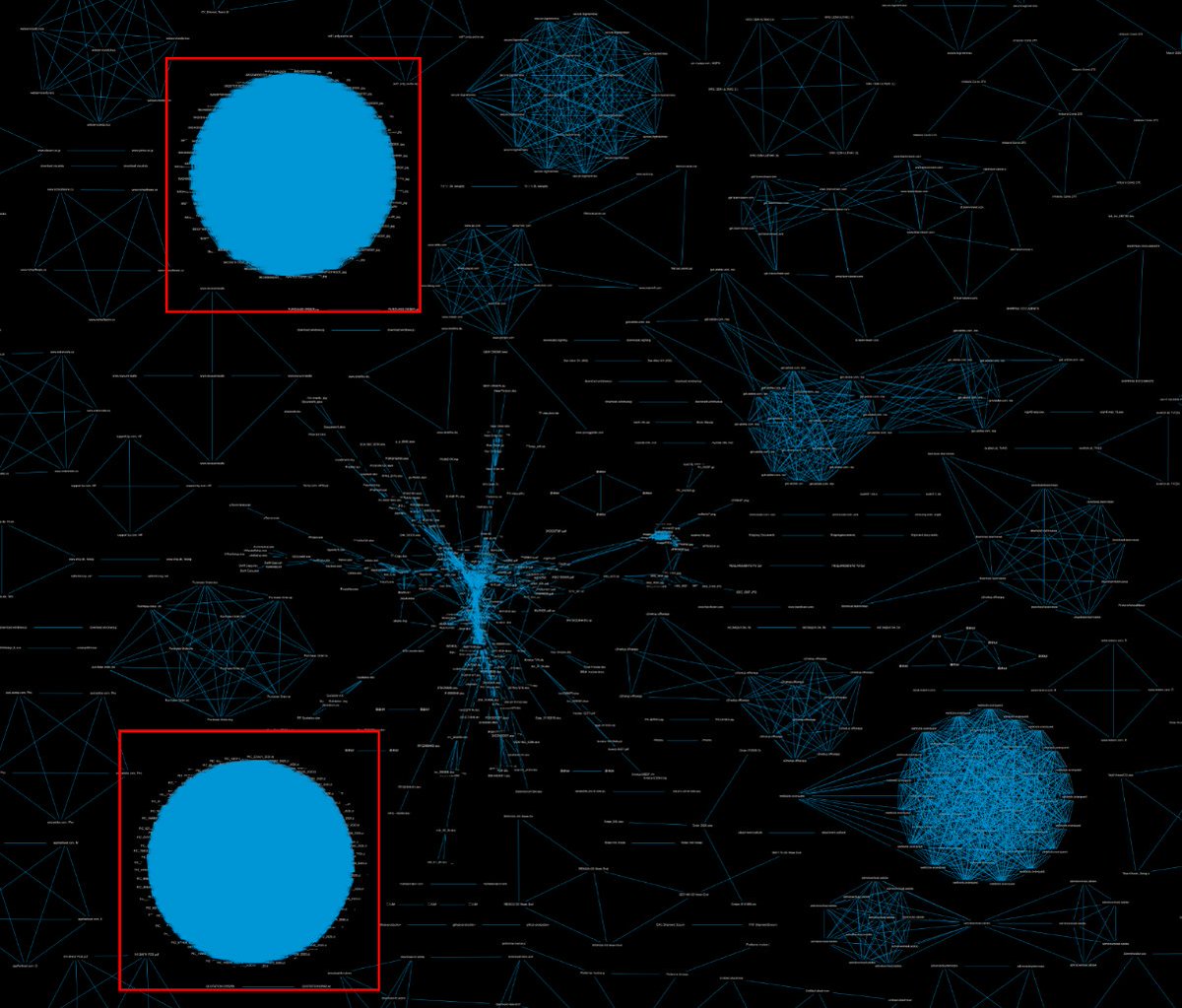



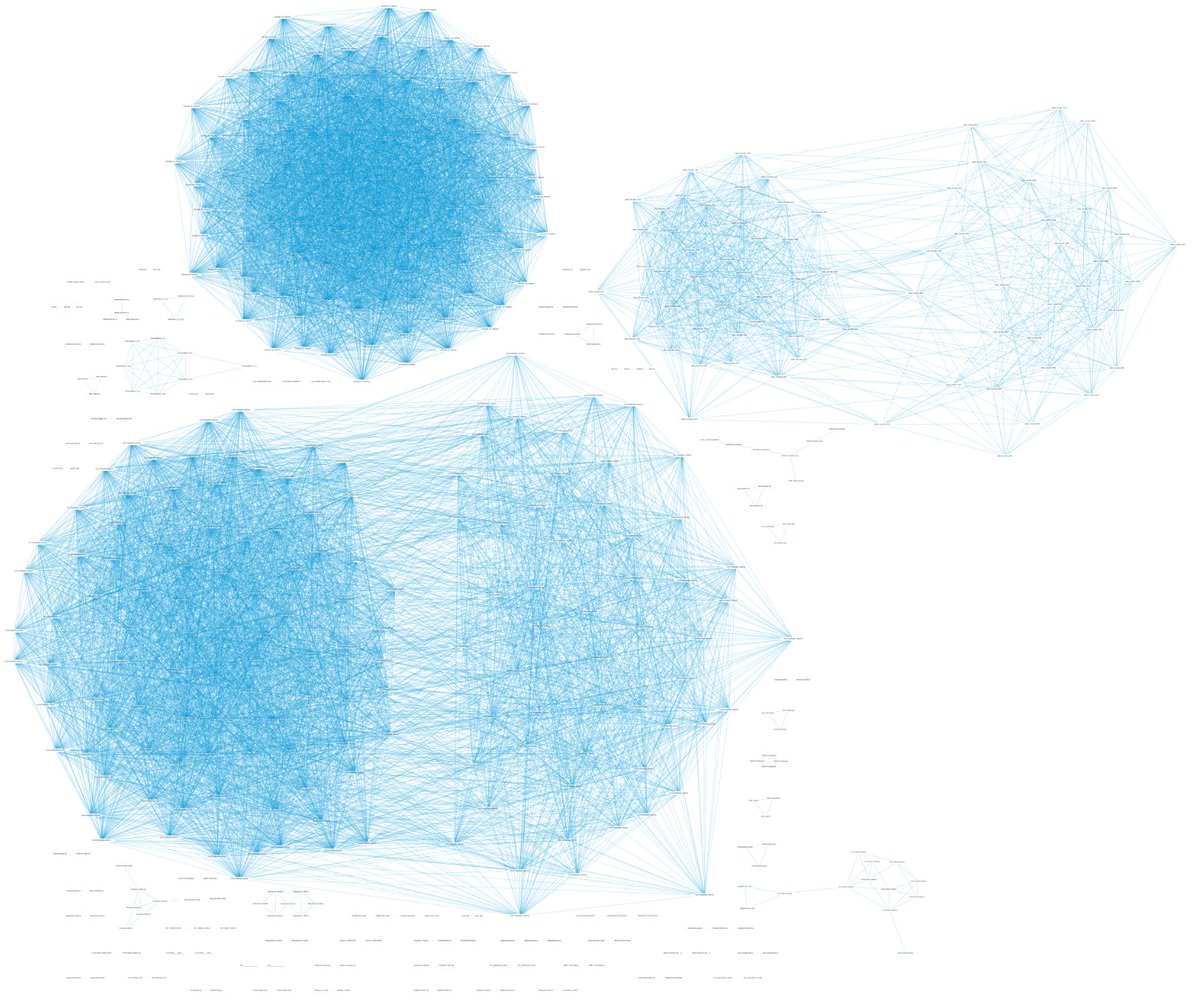
![HP Wolf Security (@hpsecurity) on Twitter photo New #PurpleFox EK campaign spotted in the wild.
An IE Exploit was hosted on this domain:
hxxps://feneffecsdoteteat.aixgedbubirtsabkhotsswse[.]shop
C2 (registered on 25/07/2021):
hxxps://8ze[.]me/u.php?id=1 New #PurpleFox EK campaign spotted in the wild.
An IE Exploit was hosted on this domain:
hxxps://feneffecsdoteteat.aixgedbubirtsabkhotsswse[.]shop
C2 (registered on 25/07/2021):
hxxps://8ze[.]me/u.php?id=1](https://pbs.twimg.com/media/E7NojPmXsAAj2yG.jpg)