Daniel Chun
@chunderstruck
IR Consultant @mandiant a Google Cloud Company #DFIR
Opinions are my own
ID: 142961291
12-05-2010 06:02:09
452 Tweet
255 Followers
1,1K Following


#log4j thread Detection Ideas + Yara by Florian Roth ⚡️ - gist.github.com/Neo23x0/e4c8b0… Hashes for vulnerable LOG4J versions by Rob Fuller - github.com/mubix/CVE-2021… SIGMA by SOC Prime - tdm.socprime.com/tdm/info/XY2Ej… tdm.socprime.com/tdm/info/4SiOs… Payloads list by GreyNoise - gist.github.com/nathanqthai/01…





Today we are very proud to release IRIS: github.com/dfir-iris/iris…. It is a collaborative platform designed for and by IR analysts. Developed and used by the Airbus Defence and Space Cyber CSIRT (special mention to the main dev, WhiteKernel). 1/4

I completed the Slot Machine Scrutiny challenge! holidayhackchallenge.com Don't miss out on SANS #HolidayHack x KringleCon holidayhackchallenge.com








Good morning, hope you’ve had your breakfast 🥣 Have you ever looked at your #Azure Serial connections? Did you know about them? Well, Serial is part of a well balanced attack for UNC3944. Mandiant (part of Google Cloud) #Intel and #consulting dropped another 🔥 blog! 🔗: mandiant.com/resources/blog…


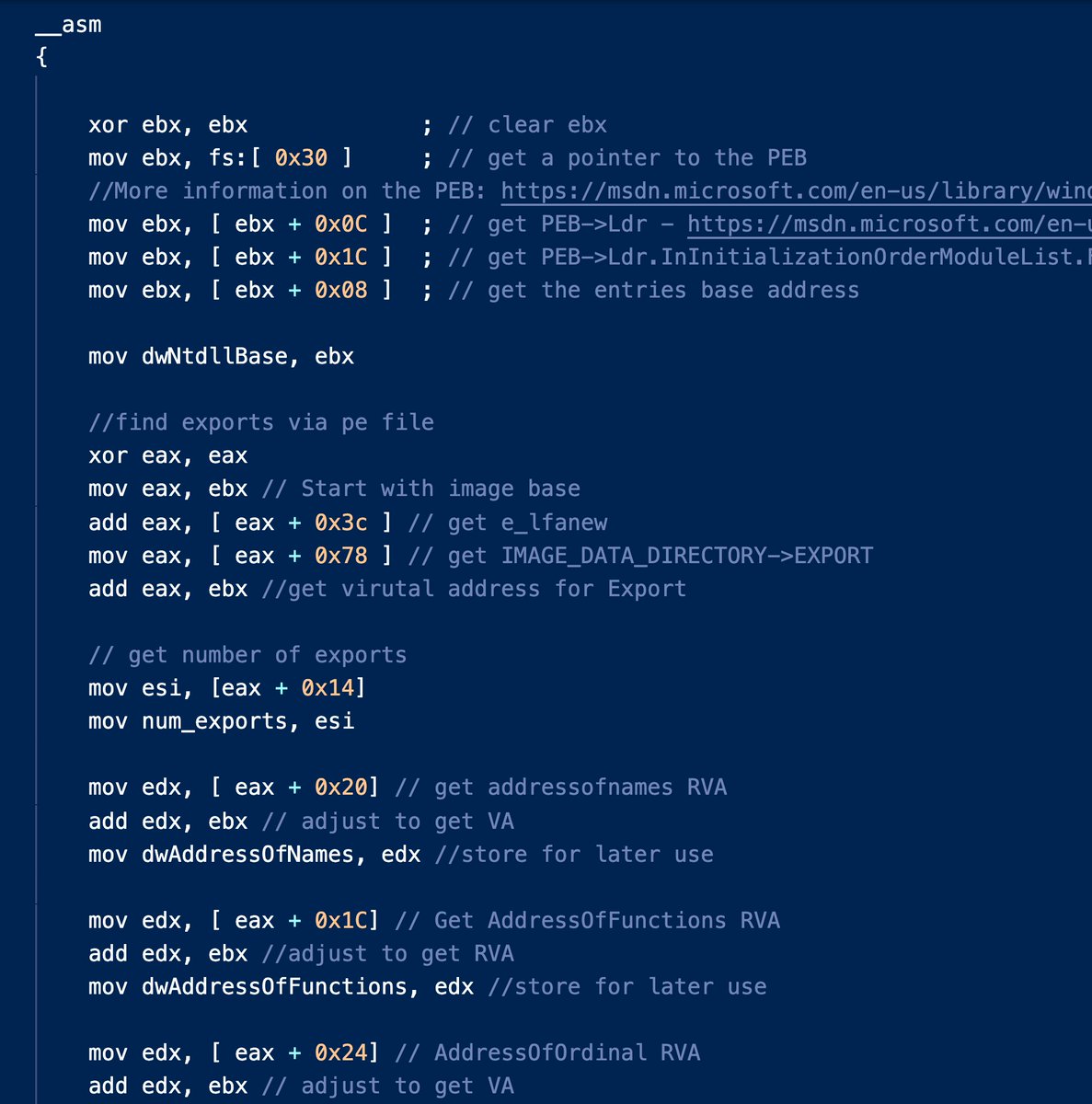
I did a thing! I created my first GPT named "MagicUnprotect". This GPT is connected to the #UnprotectProject knowledgebase. You can ask anything related to evasion techniques! I'll share it when the test is done 🤓 #infosec #malware Jean-Pierre LESUEUR