Shannon McHale
@_shannon_mchale
Red Team @ Mandiant/Google 👩🏻💻 Focused on hacking and protecting clouds. Presenter at DefCon, ShmooCon, WiCyS, and WiConnects. Ex-@RITSECclub President
ID: 1011355803234766848
https://github.com/Littlehack3r/awesome-gcp-pentesting/blob/main/README.md 25-06-2018 21:09:48
506 Tweet
1,1K Followers
692 Following

Wanted to give folks a TLDR on this one because 1. Its one of the bigger GCP vulns to come out in a while (h/t Orca Security ) 2. I know most aren't that familiar with GCP and would benefit from a TLDR; 1/8

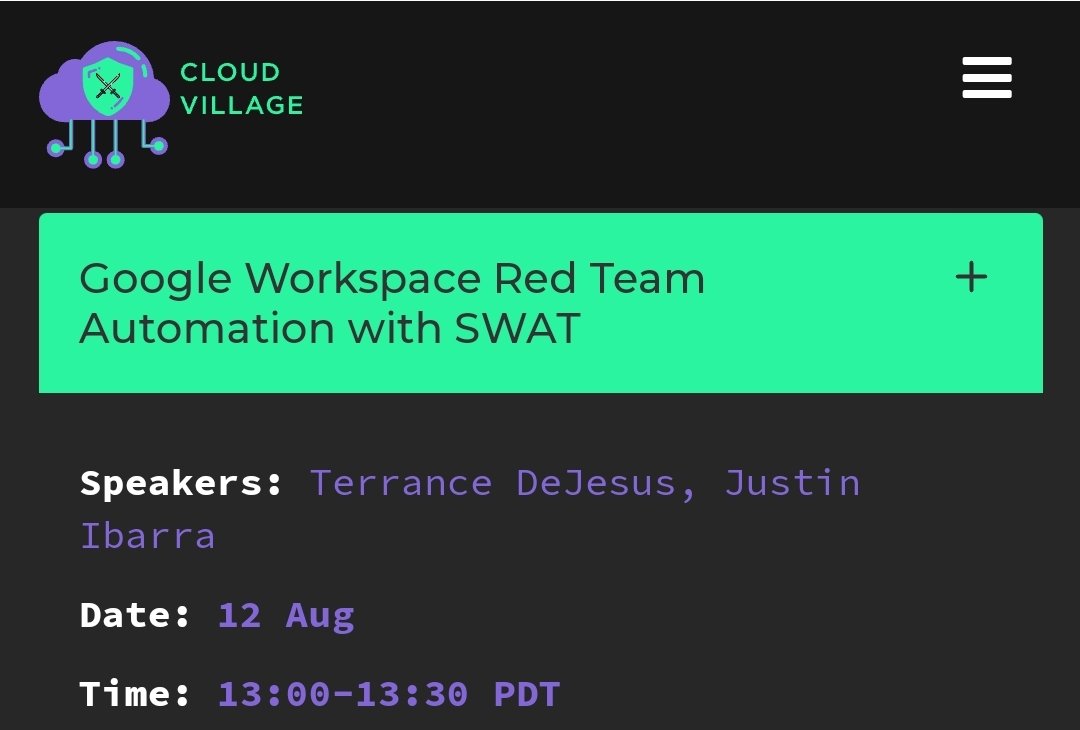
w00t! Come check us out at the DEF CON Cloud Village, where Terrance DeJesus and I will be sharing a demo tool talk about emulating attacks on #GoogleWorkspace #defcon31 #DetectionEngineering


Had so much fun recording Cloud Security Podcast we talked about learning to hack GCP and some of the common attack paths Ofc always repin RITSEC Club and stay tune to the end for a mandatory shoutout to my mom and the #CeliacsInCyber (which I just made up) youtube.com/watch?v=SqfDFI…

I am excited to announce that I will be presenting at Black Hat and DEF CON with JS0N Haddix and Gunnar Andrews! 💻 Black Hat DEF CON #InfoSec #OffensiveSecurity #OpenSource




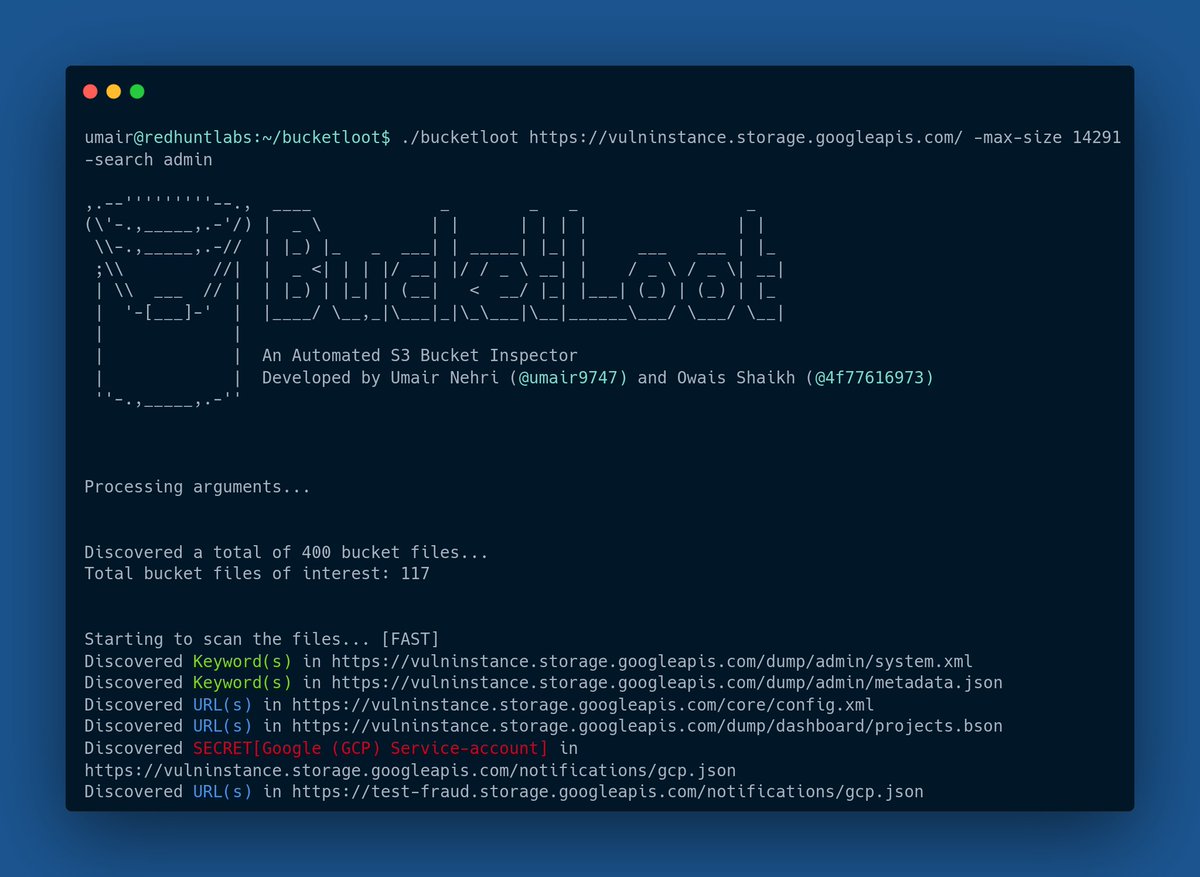
a new tool released by Justin Ibarra and Terrance DeJesus for simulating attacks against Google Workspace. github.com/elastic/SWAT



Shmoo 🫎Shmoo🫎 Shmoo🫎 Excited to see talks by Hulto Katie Nickels and Dillon Franke Even more hype to see all the homies, especially mentors/mentees

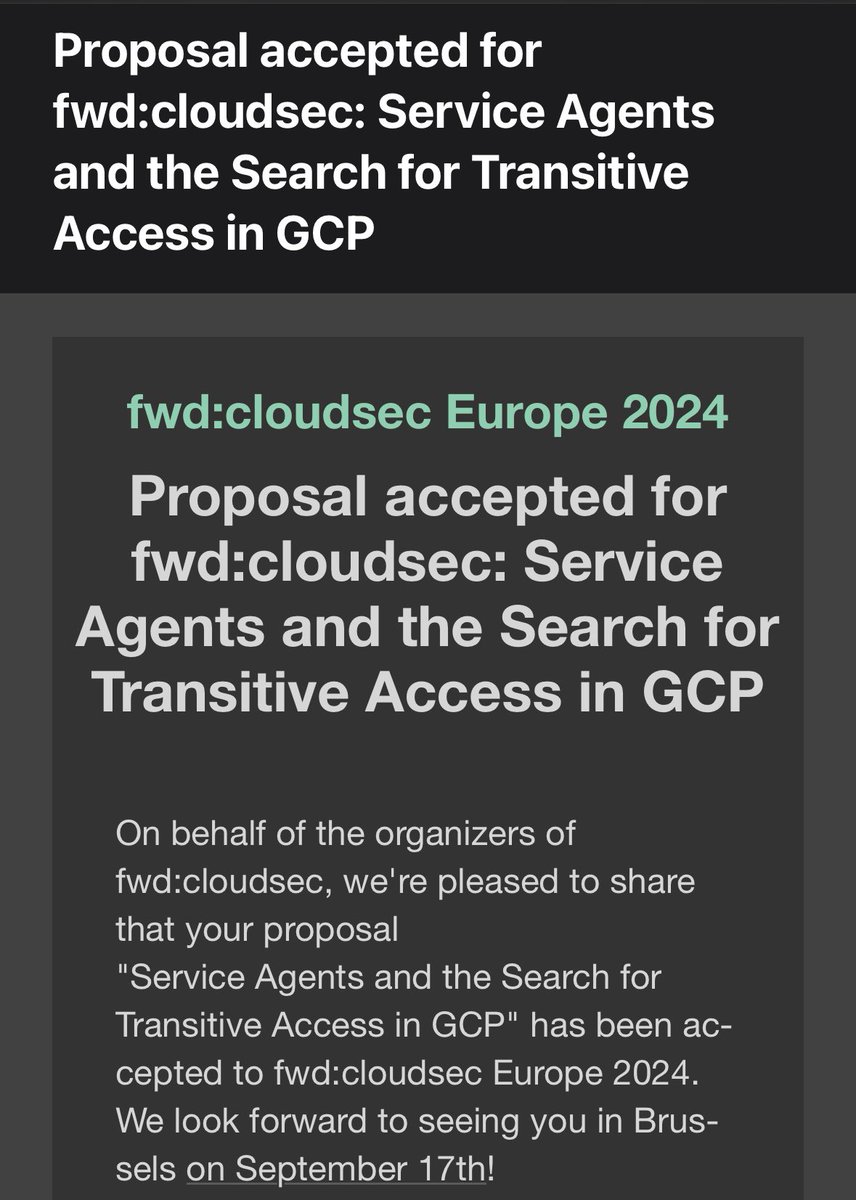
Thrilled to say I’ll be speaking at fwdcloudsec EU this September on new #GCP research covering Service Agent abuse. Hope to see you there!




Take a journey in Administrative Unit Attack Paths! Check out Katie Knowles's #SOCON2025 talk, which starts w/ scoped role assignments for privilege escalation against users & groups and finishes w/ protecting accounts using Restricted Management AUs. 👀: ghst.ly/4ksxiEx

Most companies find out about weaknesses too late. Mandiant (part of Google Cloud) Red Teamers use offensive security to spot and fix vulnerabilities before attackers can exploit them. See how they help organizations stay ahead and learn more: bit.ly/4o3OnGp